Learn how hackers steal credit card data from online stores, real-world attack examples, and the best 2025 detection and prevention strategies to protect your eCommerce website and customers from Magecart e-skimming.

Magecart attacks represent one of the most dangerous threats facing e-commerce businesses today, silently stealing payment card data from thousands of online stores.
According to Imperva’s security analysis:
“Magecart is a threat actor involved in payment card skimming operations with a focus on insecure e-commerce websites.”
Source Defense reports that:
“Magecart infections skyrocketed by 103% in just six months, understanding this threat is critical for every online merchant.”
This comprehensive guide explains what Magecart is, how e-skimming works, the anatomy of attacks, detection methods, and proven prevention strategies.
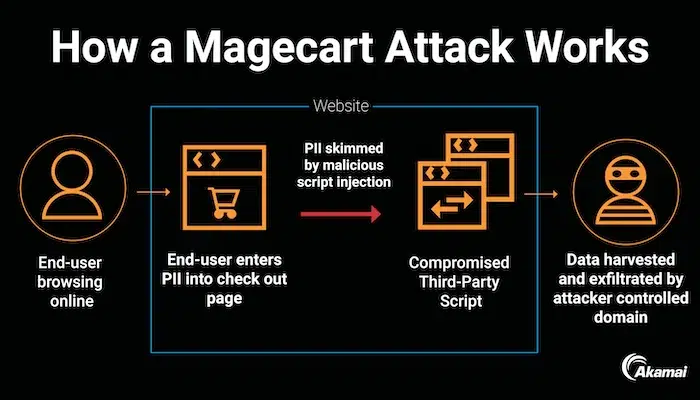
Source: Akami Magecart Attack
What Is Magecart? Understanding Digital Card Skimming
Magecart refers to both a specific cybercriminal group and a broader category of attacks involving digital credit card skimming on e-commerce websites.
Akamai explains that:
“Magecart attack refers to a type of cyberattack that targets ecommerce sites by injecting malicious code into checkout pages, allowing threat actors to ‘skim’ user credit card details.”
The name “Magecart” comes from early attacks targeting Magento shopping cart platforms, though modern Magecart attacks affect all e-commerce platforms including Shopify, WooCommerce, custom-built stores, and even major retailers.
E-Skimming Explained: Client-Side Payment Theft
E-skimming, also called client-side skimming or JavaScript skimming, is the technique Magecart attackers use to steal payment information. Unlike traditional data breaches that steal stored payment data from databases, e-skimming captures payment information in real-time as customers enter it during checkout.
How Client-Side Skimming Differs: Traditional security focuses on server-side threats, protecting databases, servers, and backend systems. Client-side attacks happen in the customer’s browser, invisible to traditional security tools. This makes e-skimming particularly dangerous and difficult to detect.
The stolen data goes directly from the customer’s browser to criminal servers before legitimate payment processing occurs, so neither merchants nor customers realize theft has happened until fraudulent charges appear.
The Evolution of Magecart Attacks
Trustwave SpiderLabs reveals that:
“They first blogged about Magecart back in 2019; fast forward five years and it is still here going strong.”
The threat has evolved from simple script injections to sophisticated, multi-stage attacks using advanced obfuscation and evasion techniques.
Modern Magecart groups operate as organized criminal enterprises with specialized roles: some compromise websites, others develop skimming scripts, and dedicated teams collect and monetize stolen payment data.
Source: What Is Magecart
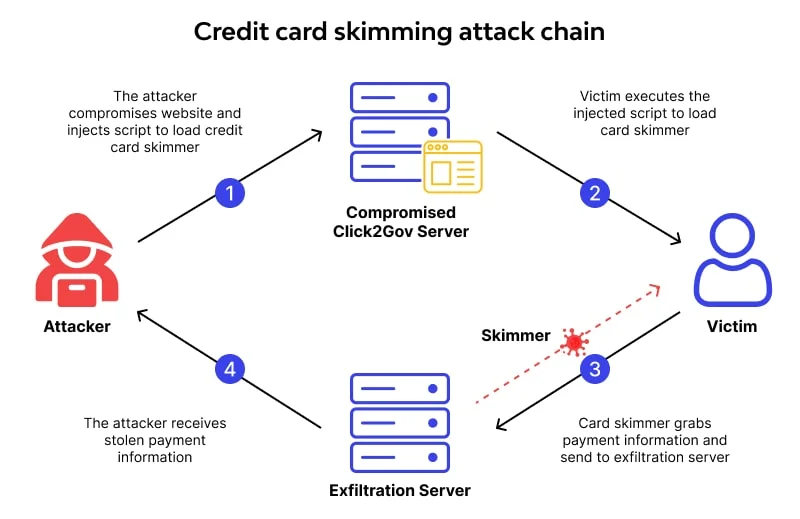
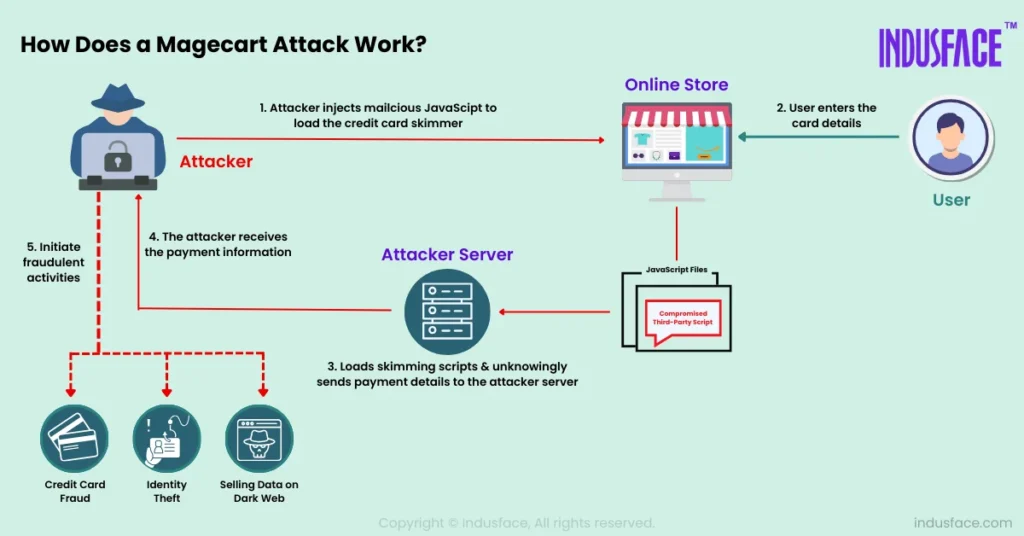
How Magecart E-Skimming Works: The Attack Process
Understanding the attack process helps merchants recognize vulnerabilities and implement effective defenses:
Step 1: Initial Compromise and Access
Magecart attacks begin when criminals gain access to e-commerce websites through various methods:
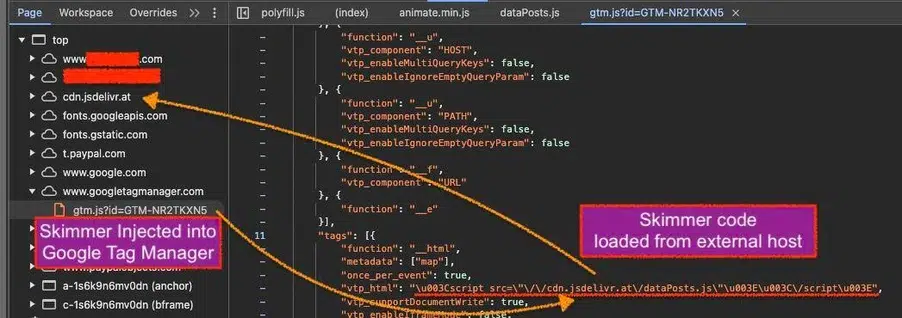
Third-Party Supply Chain Compromise: Attackers compromise legitimate third-party services like analytics tools, chat widgets, payment processors, or advertising networks that e-commerce sites use.
According to Jscrambler’s analysis:
“typical Magecart behavior includes third-party scripts tampering with payment forms.”
Direct Website Compromise: Criminals exploit vulnerabilities in e-commerce platforms, plugins, or custom code to inject malicious scripts directly into websites. Unpatched software, weak credentials, and SQL injection vulnerabilities provide common entry points.
Supply Chain Attacks on Service Providers: Attackers target hosting providers, content delivery networks (CDNs), or payment gateway providers, compromising multiple e-commerce sites simultaneously through single exploits.
Insider Threats: In some cases, malicious insiders or social engineering attacks against employees provide access to inject skimming code.
Step 2: Payment Form Injection and Malicious Code
Once attackers gain access, they inject malicious JavaScript code into checkout pages.
Human Security suggest that:
“criminals inject malicious scripts into real payment pages to change form behavior or add or modify JavaScript code to create fake payment forms.”
Code Injection Methods Include:
Direct Script Injection: Malicious code embedded directly into payment page HTML or JavaScript files.
Third-Party Script Modification: Legitimate third-party scripts compromised to include skimming functionality while maintaining normal operations.
Payment Form Replacement: Entire payment forms replaced with identical-looking fake versions that capture data while appearing legitimate.
DOM Manipulation: JavaScript code that modifies payment forms dynamically in customer browsers, adding invisible data capture functionality.
The injected code is typically heavily obfuscated to evade detection during security scans. Attackers use encryption, encoding, dynamic code generation, and anti-debugging techniques to hide malicious functionality.
Step 3: JavaScript Skimming and Data Capture
When customers enter payment information, the malicious JavaScript activates and captures data. The Feroot detection guide details how skimming scripts target multiple data types:
Primary Targets:
- Credit card numbers and CVV codes
- Expiration dates
- Cardholder names
- Billing addresses
- Email addresses and phone numbers
Advanced Data Collection: Some Magecart variants also capture login credentials, personal information from account creation forms, session tokens for account takeover, and complete checkout data including order details.
The skimming code monitors input fields, detects when customers enter payment information, captures data through keylogging or form submission interception, and triggers data transmission to criminal servers.
Step 4: Data Exfiltration to Criminal Servers
Stolen payment data gets sent to criminal-controlled servers through various methods designed to avoid detection:
Direct Transmission: Data sent immediately to external servers using XMLHttpRequest or Fetch API calls.
Image Beacon Technique: Data encoded in fake image requests that look like legitimate tracking pixels but actually transmit stolen information.
WebSocket Connections: Persistent connections established for real-time data streaming.
DNS Tunneling: Data hidden in DNS queries to evade network monitoring.
Delayed Transmission: Some sophisticated variants store data locally and transmit in batches or only under specific conditions to avoid detection.
According to Jscrambler:
“payment data being sent out to an unknown domain represents typical Magecart behavior that security systems should monitor.”
Step 5: Checkout Compromise and Ongoing Operations
The malicious code allows normal checkout to proceed, so customers complete purchases successfully without realizing their payment information was stolen. This stealth enables Magecart infections to operate for months, stealing thousands of payment cards before detection.
Attackers often implement persistence mechanisms ensuring the skimming code remains active even after website updates, security scans, or attempted removals. Sophisticated groups use multiple injection points, regularly update malicious code, and monitor infected sites to restore compromised scripts if removed.
Anatomy of Magecart Attacks: Real-World Examples
Understanding specific attack patterns helps recognize threats:
The CosmicSting Attack: 75% Platform Compromise
Trustwave documented that:
“CosmicSting impacted 75% of Adobe Commerce and Magento platforms,”
This represents one of 2024’s most widespread e-commerce compromises. This massive attack demonstrated how a single vulnerability in popular platforms can affect thousands of online stores simultaneously.
CosmicSting exploited an XML External Entity (XXE) vulnerability in Adobe Commerce allowing remote code execution. Attackers injected Magecart skimmers into checkout pages across thousands of infected stores, stealing payment data for months before detection.
Third-Party Widget Compromises
Several Magecart campaigns have targeted third-party services that e-commerce sites integrate:
Chat Widget Attack: Criminals compromised a popular customer support chat widget used by thousands of online stores. The compromised widget included hidden Magecart code affecting every site using the service.
Analytics Service Breach: A web analytics provider was compromised, and malicious code was injected into their tracking scripts. Since these scripts load on every page including checkout, attackers gained access to payment forms across hundreds of e-commerce sites.
Payment Gateway Compromise: Attackers compromised a payment gateway provider’s scripts, directly accessing payment information as it was entered across multiple merchant sites.
Supply Chain Attacks Through NPM Packages
Some Magecart groups compromise JavaScript packages in NPM (Node Package Manager) repositories. When developers install these compromised packages, they unknowingly include Magecart code in their e-commerce sites. This supply chain attack method scales efficiently, potentially affecting thousands of websites through single compromised packages.
Major Retailer Breaches
Magecart attacks have affected major retailers including British Airways (380,000 customers affected), Ticketmaster (40,000 customers), and Newegg. These high-profile breaches demonstrate that even large companies with security teams can fall victim to sophisticated Magecart campaigns.
Source: Trustwave – State of Magecart
Detecting Magecart E-Skimming: Signs and Methods
Early detection limits damage from Magecart infections. Here are detection approaches:
Behavioral Monitoring for Suspicious Activity
Jscrambler emphasizes that:
“Detecting typical Magecart behavior, like third-party scripts tampering with payment forms or payment data being sent to unknown domains, requires continuous monitoring.”
Warning Signs Include:
- Unexpected JavaScript modifications to payment forms
- New or modified third-party scripts loading on checkout pages
- Payment data transmitted to unfamiliar domains
- Obfuscated or encoded JavaScript on payment pages
- Unusual network requests during checkout processes
- Scripts loading from suspicious or newly registered domains
Client-Side Security Monitoring
Traditional server-side security tools can’t see client-side attacks happening in customer browsers. Specialized client-side security solutions monitor JavaScript execution, detect unauthorized form modifications, identify data exfiltration attempts, and block suspicious script behavior in real-time.
DataDome’s prevention guide highlights that:
“Client-side third-party management represents a critical defense against Magecart.”
Regular Security Audits and Code Reviews
Conduct regular reviews of:
- All JavaScript loading on payment pages
- Third-party services and their security practices
- Recently modified files, especially on checkout pages
- Unexpected changes to payment processing code
- New or unfamiliar domains in network requests
Subresource Integrity (SRI) Monitoring
Implement Subresource Integrity checks that verify third-party scripts haven’t been modified. SRI uses cryptographic hashes to ensure scripts load exactly as expected. When hash mismatches occur, browsers block the scripts, preventing compromised versions from executing.
Content Security Policy (CSP) Implementation
Content Security Policies restrict which scripts can execute and where data can be sent. Properly configured CSP prevents unauthorized scripts from loading and blocks data transmission to suspicious domains. Monitor CSP violation reports to identify attempted attacks.
Network Traffic Analysis
Monitor outbound traffic from payment pages for:
- Connections to unknown or suspicious domains
- Data transmissions during payment form interactions
- Unusual patterns in image requests or API calls
- DNS queries to newly registered domains
- Encrypted data in query parameters or headers
Third-Party Script Inventory and Monitoring
Maintain comprehensive inventories of all third-party scripts used on your site. Monitor for:
- Unauthorized new scripts
- Modifications to existing scripts
- Changes in script behavior or data access
- New domains hosting familiar scripts
- Expired SSL certificates on third-party domains
Source: Detect Magecart Attacks
Preventing Magecart Attacks: Comprehensive Protection
Effective Magecart prevention requires multiple security layers:
PCI DSS 4.0 Compliance Requirements
DataDome points out that:
“PCI DSS 4.0 includes specific requirements addressing client-side security.”
Requirement 6.4.3 mandates that all payment page scripts are managed and that merchants maintain inventories and justify the necessity of each script.
Key PCI DSS 4.0 Client-Side Requirements:
- Maintain inventories of all scripts on payment pages
- Implement integrity checks for payment page scripts
- Monitor for unauthorized script modifications
- Implement Content Security Policies
- Regularly review third-party script security
Client-Side Security Solutions
Deploy specialized client-side security platforms that:
- Monitor JavaScript execution in real-time
- Detect payment form tampering
- Block unauthorized data exfiltration
- Enforce script behavior policies
- Provide visibility into client-side activity
These solutions operate in customer browsers, providing protection where Magecart attacks occur.
Content Security Policy (CSP) Implementation
Implement strict CSP headers that:
- Whitelist only authorized script sources
- Prevent inline JavaScript execution
- Block data transmission to unauthorized domains
- Require integrity checks for third-party scripts
- Log policy violations for investigation
CSP provides powerful defense against script injection attacks when properly configured.
Subresource Integrity (SRI) for Third-Party Scripts
Use SRI attributes on all third-party script tags to verify scripts haven’t been modified. Include cryptographic hashes that browsers verify before executing scripts. Update hashes when legitimate script updates occur.
Third-Party Risk Management
Carefully vet all third-party services before integration by assessing their security practices, reviewing security certifications and audits, checking incident history, evaluating update and patch management, and requiring contractual security obligations.
Continuously monitor integrated third-party services and limit the number of third-party scripts to only essential services.
Regular Security Updates and Patch Management
Keep all software current including e-commerce platforms, plugins and extensions, themes and templates, server software and dependencies, and security tools. Subscribe to security bulletins for technologies you use and apply critical patches immediately.
Web Application Firewall (WAF) Protection
Deploy WAFs configured to detect and block Magecart indicators including suspicious script injections, unauthorized payment form modifications, data exfiltration attempts, and connections to known malicious domains.
Security Monitoring and Incident Response
Implement 24/7 monitoring for Magecart indicators with automated alerts for suspicious activity. Develop incident response procedures specifically for Magecart infections including rapid script removal, customer notification protocols, payment processor communication, and forensic investigation processes.
Payment Tokenization and Hosted Payment Pages
Use payment tokenization replacing card data with tokens or hosted payment pages where customers enter payment information on payment processor sites rather than merchant sites. These approaches reduce or eliminate the need to handle raw payment data, significantly reducing Magecart risk.
Employee Training and Awareness
Train staff to recognize phishing attempts targeting administrative access, follow secure coding practices, properly manage third-party integrations, respond appropriately to security alerts, and understand Magecart risks and indicators.
Conclusion
Magecart e-skimming represents a persistent and evolving threat to e-commerce security, with infections surging 103% in recent months and affecting major platforms like Adobe Commerce. The sophisticated client-side nature of these attacks makes them particularly dangerous, operating invisibly in customer browsers while traditional security tools focus on server-side threats.
Understanding how Magecart works from initial compromise through third-party services or direct exploitation, to payment form injection with obfuscated JavaScript, real-time data capture during checkout, and stealthy exfiltration to criminal servers helps merchants recognize vulnerabilities and implement effective defenses.
Detection requires specialized client-side security monitoring, behavioral analysis for suspicious script activity, regular security audits, SRI and CSP implementation, and comprehensive third-party script management. Prevention demands multiple security layers including PCI DSS 4.0 compliance, client-side security solutions, strict CSP policies, third-party risk management, regular updates, WAF protection, security monitoring, and employee training.
The 75% platform compromise rate from CosmicSting and major retailer breaches demonstrate that no e-commerce business is too large or too secure to ignore Magecart threats. By implementing the detection and prevention strategies outlined in this guide, merchants can significantly reduce their risk of becoming the next Magecart victim while protecting customer payment data and maintaining the trust essential for e-commerce success.
Glossary of Magecart E-Skimming Terms
Client-Side Attack: Cyberattack targeting code executing in user browsers rather than on servers
Content Security Policy (CSP): HTTP header restricting which resources can load and execute on web pages
E-Skimming: Digital theft of payment card data from online checkout forms
JavaScript Skimming: Using malicious JavaScript to capture payment information in customer browsers
Magecart: Cybercriminal groups specializing in e-commerce payment card skimming
Payment Form Injection: Inserting malicious code into e-commerce checkout pages to steal payment data
PCI DSS 4.0: Latest Payment Card Industry Data Security Standard including client-side security requirements
Subresource Integrity (SRI): Security feature verifying third-party resources haven’t been tampered with
Supply Chain Attack: Compromising third-party vendors to access multiple target organizations
Third-Party Script: JavaScript code from external sources loaded on websites
Frequently Asked Questions
What is Magecart e-skimming?
Magecart e-skimming is a type of cyberattack where hackers inject malicious JavaScript code into eCommerce websites to steal customers’ payment and personal information during checkout.
How do Magecart e-skimming attacks work?
Attackers exploit vulnerabilities in website code, plugins, or third-party integrations to insert hidden scripts that capture and transmit credit card data to their remote servers in real time.
What are the common signs of a Magecart infection?
Unusual JavaScript files, unauthorized code changes, slow checkout pages, or customer complaints about fraudulent charges may indicate a Magecart compromise.
How can businesses detect Magecart attacks?
Detection involves using web integrity monitoring tools, scanning scripts for unauthorized changes, employing Content Security Policies (CSP), and running regular vulnerability audits.
What are the best ways to prevent Magecart e-skimming?
Businesses can prevent e-skimming by keeping software and plugins updated, limiting third-party scripts, implementing Subresource Integrity (SRI), and using real-time monitoring to detect suspicious activities.
