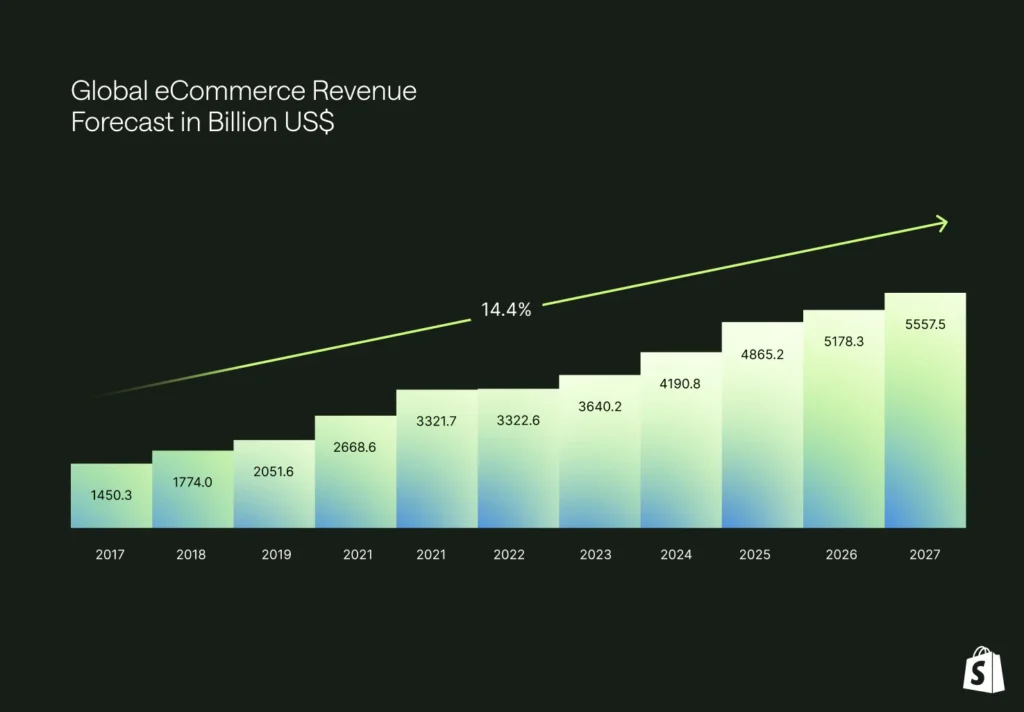
E-commerce cybersecurity has become critical as online shopping dominates retail, with cybercriminals targeting the valuable payment and personal data flowing through online stores.

According to RSI Security’s 2025 trends, e-commerce businesses face evolving threats requiring comprehensive security measures. Therefore, understanding e-commerce security is essential for merchants and customers. This guide explains what e-commerce cybersecurity is, why it matters, common threats, and how to protect your online business and customer data.
Indusface reports that:
“Cybersecurity threats continue to evolve rapidly in 2025, with the latest data revealing a sharp rise in vulnerabilities, active exploits, and large-scale breaches.”
Source: E-commerce Risk Trends 2025
Understanding E-commerce Cybersecurity
E-commerce cybersecurity refers to the practices, technologies, and protocols that protect online stores, payment systems, and customer data from cyber threats.
It encompasses everything from securing website infrastructure and protecting payment processing to safeguarding customer personal information and maintaining business operations during attacks.
What E-commerce Security Protects
E-commerce security protects multiple critical elements:
Payment Data: Credit card numbers, bank account information, and payment credentials that criminals target for financial fraud.
Customer Personal Information: Names, addresses, email addresses, phone numbers, and purchase histories that enable identity theft.
Business Data: Product catalogs, pricing information, supplier details, and proprietary business intelligence.
Website Infrastructure: Servers, databases, applications, and networks that keep online stores operational.
Customer Trust: The reputation and confidence that drives customers to shop with your business.
The CIA Triad in E-commerce Security
E-commerce cybersecurity is built on the CIA triad—three fundamental principles:
Confidentiality ensures that sensitive information like payment data and customer details remains accessible only to authorized parties. E-commerce sites must use encryption, access controls, and secure authentication to prevent unauthorized access.
Integrity guarantees that data remains accurate and unaltered. Product prices, order details, payment amounts, and customer information must be protected from tampering. If criminals can change prices or redirect payments, both customers and merchants suffer losses.
Availability ensures that online stores remain accessible to legitimate customers. DDoS attacks, server failures, or ransomware can shut down e-commerce operations, causing immediate revenue loss and long-term reputation damage.
Why E-commerce Security Matters
According to Shopify’s retail cybersecurity analysis, e-commerce security directly impacts business survival. The consequences of inadequate security include:
Financial Losses: Direct theft through payment fraud, business interruption costs, recovery expenses, and regulatory fines.
Customer Trust Erosion: Once customers learn their data was compromised, they abandon the merchant permanently and warn others.
Legal Consequences: Non-compliance with PCI DSS and data protection laws results in fines, lawsuits, and potential business closure.
Reputation Damage: News of security breaches spreads quickly, destroying years of brand building overnight.
Competitive Disadvantage: Customers choose competitors with better security reputations.
Source: Retail Cybersecurity 2025
Types of E-commerce Security Threats
E-commerce businesses face numerous cybersecurity threats, each requiring specific defenses:
Payment Card Fraud and Data Theft
Payment card fraud represents the primary threat to e-commerce. Criminals use various methods to steal payment information:
Card Not Present (CNP) Fraud: Criminals use stolen card details for online purchases. According to Shopify, this fraud type particularly affects e-commerce because transactions don’t require physical card presence.
Credit Card Skimming: Malicious code injected into e-commerce websites captures payment information as customers enter it. This digital skimming, often called “Magecart” attacks, affects even major retailers.
Data Breaches: Hackers compromise databases storing payment information, stealing thousands or millions of card records simultaneously. Astra Security notes that:
“E-commerce security threats are continuing to cause havoc and losses in the world of online trading.”
Phishing and Social Engineering
Phishing attacks target both merchants and customers. Criminals send fake emails appearing to come from e-commerce platforms, banks, or shipping companies to steal login credentials or payment information.
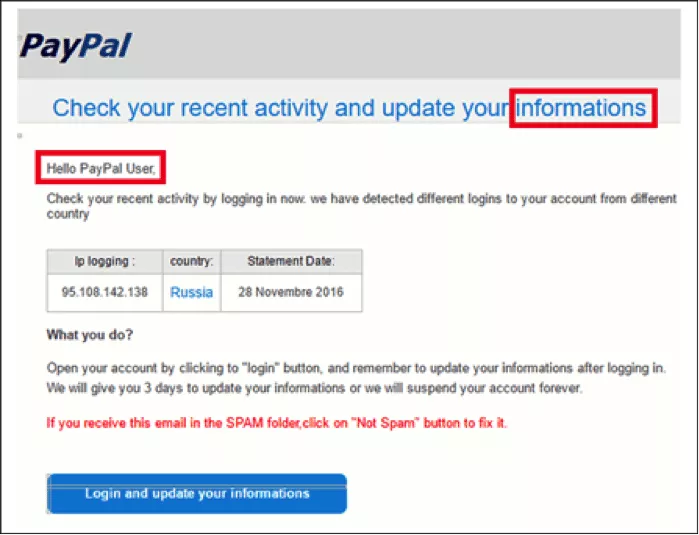
Source: infosecinstitute
For merchants, phishing might impersonate payment processors requesting account updates or internal emails requesting wire transfers. For customers, fake order confirmations or shipping notifications lead to credential theft.
DDoS Attacks (Denial of Service)
Distributed Denial of Service (DDoS) attacks overwhelm e-commerce websites with traffic, making them unavailable to legitimate customers. According to Frontiers research:
“Denial of services represents a major cybersecurity concern for e-commerce.”
DDoS attacks cause immediate revenue loss during downtime and may serve as distractions while criminals conduct other attacks. Attackers sometimes demand ransom to stop attacks, creating additional extortion threats.
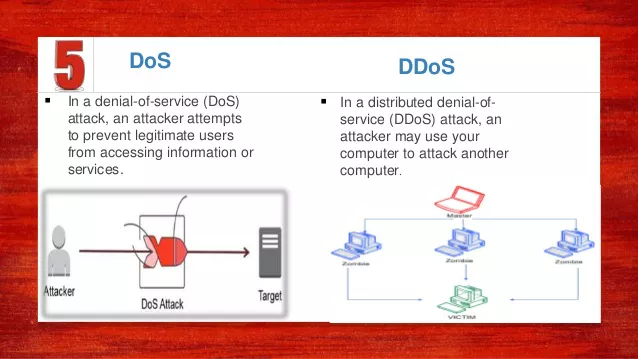
Source: Slideshare.net
SQL Injection Attacks
SQL injection exploits vulnerabilities in e-commerce database queries. Criminals insert malicious SQL code through website forms, search boxes, or URL parameters to:
- Extract customer data and payment information from databases
- Modify product prices or inventory levels
- Delete critical business data
- Gain administrative access to websites
Aalpha’s 2025 security analysis emphasizes that:
“Security plugins can detect and block code injections, XSS, and SQL injections when properly implemented.”
Cross-Site Scripting (XSS)
XSS attacks inject malicious JavaScript into e-commerce websites that executes in customer browsers. This enables criminals to:
- Steal session cookies and hijack customer accounts
- Redirect customers to phishing sites
- Modify page content to capture payment information
- Spread malware to website visitors
Malware and Ransomware
Malware infections target e-commerce infrastructure to steal data or disrupt operations. Ransomware encrypts business data and demands payment for decryption, potentially shutting down online stores completely.
E-commerce malware often includes:
- Backdoors providing persistent access to systems
- Keyloggers capturing administrator credentials
- Banking trojans targeting payment processing
- Cryptominers use server resources for cryptocurrency mining
Account Takeover (ATO)
Account takeover occurs when criminals gain access to customer accounts through stolen credentials. Shopify explains that:
Attackers use stolen credentials to hack into customer accounts, make unauthorized purchases, or steal personal information.”
Criminals obtain credentials through phishing, data breaches, or credential stuffing attacks that test leaked passwords across multiple sites. Once inside accounts, they make fraudulent purchases, steal stored payment methods, or gather information for identity theft.
E-skimming (Digital Skimming)
E-skimming injects malicious JavaScript into payment pages to capture card details as customers enter them. Unlike traditional database breaches, e-skimming steals data in real-time without requiring direct access to stored payment information.
These attacks are difficult to detect because the malicious code often loads from external servers and may only activate during specific conditions, evading security scans.
Chargeback Fraud (Friendly Fraud)
Chargeback fraud occurs when customers dispute legitimate charges with their banks, claiming they did not authorize purchases or receive products. Shopify suggest that:
“Customers dispute legitimate charges after receiving products or services.”
While sometimes resulting from genuine confusion, organized chargeback fraud costs merchants significant revenue and can lead to payment processor penalties or account termination.
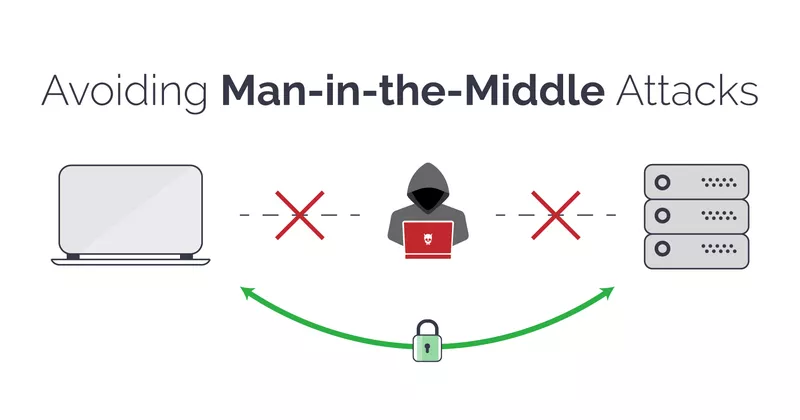
Man-in-the-Middle (MITM) Attacks
MITM attacks intercept communication between customers and e-commerce sites. Criminals position themselves between the two parties to:
- Capture unencrypted payment information
- Steal login credentials
- Modify transaction amounts
- Redirect payments to criminal accounts
Public Wi-Fi networks and compromised home routers commonly facilitate MITM attacks.
Source: Invicti (Formerly Netsparker)
Impact on Customers: The Human Cost
E-commerce security breaches affect customers severely:
Financial Losses
Customers experience direct financial harm through unauthorized charges on compromised payment cards. While banks typically reimburse fraud, the process causes stress and inconvenience. Some victims suffer significant losses before detecting fraud.
Identity Theft
Stolen personal information enables criminals to open credit accounts, file fraudulent tax returns, apply for loans, or commit crimes using victims’ identities. Identity theft recovery can take years and significantly damage credit scores.
Loss of Privacy
Data breaches expose private information, including purchase histories, addresses, and contact details. This information can be used for targeted scams, harassment, or sold to other criminals.
Inconvenience and Time Loss
Customers must cancel compromised cards, monitor accounts for fraud, dispute unauthorized charges, and potentially freeze credit. These activities consume significant time and cause substantial frustration.
Loss of Trust
After experiencing breaches, customers become hesitant to shop online or share payment information, reducing their participation in e-commerce and limiting their purchasing options.
Impact on Businesses: The Merchant Perspective
E-commerce security failures devastate merchants:
Direct Financial Costs
Businesses face enormous costs, including immediate theft losses, fraud reimbursements, forensic investigation expenses, legal fees, regulatory fines, increased insurance premiums, and security improvement investments.
Operational Disruption
Security incidents shut down online stores during investigation and remediation. Every hour offline means lost sales, abandoned shopping carts, and customers choosing competitors. RSI Security highlights that operational disruption represents a critical emerging risk.
Regulatory Penalties
Non-compliance with PCI DSS, GDPR, or other regulations results in substantial fines. According to Feroot’s PCI DSS 4.0.1 analysis:
“PCI DSS 4.0.1 became mandatory on March 31, 2025, bringing in 47 new requirements.”
Violations can cost millions in penalties.
Customer Loss
Breached businesses lose customers permanently. Competitors capitalize on security failures, gaining market share that proves difficult to reclaim. Studies show most customers never return to merchants that compromised their data.
Reputation Damage
Security breach news spreads rapidly through social media, news outlets, and word-of-mouth. Rebuilding reputation takes years and requires significant marketing investment that may never fully restore trust.
Payment Processor Penalties
Payment processors impose fines, increase transaction fees, or terminate merchant accounts after security failures. Losing the ability to accept card payments effectively ends e-commerce operations.
Legal Liability
Customers and payment card companies file lawsuits seeking damages for negligence. Class action lawsuits can bankrupt small e-commerce businesses and significantly harm larger ones.
Basic E-commerce Security Protections
Implementing fundamental security measures protects merchants and customers:
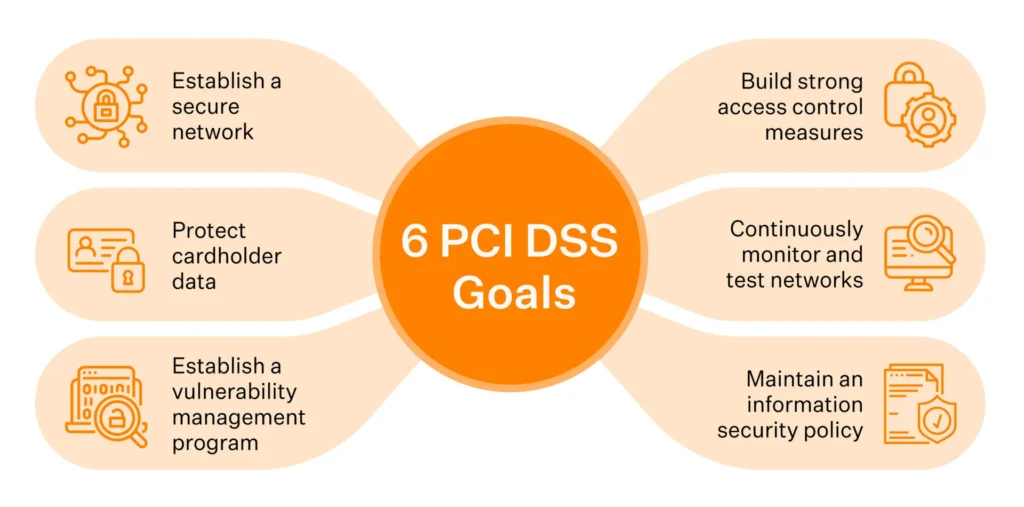
PCI DSS Compliance
The Payment Card Industry Data Security Standard (PCI DSS) establishes requirements for securely handling payment card data. According to Ampcus Cyber’s 2025 guide:
“PCI DSS compliance is essential and an ongoing journey for U.S. eCommerce businesses aiming to secure payment data and build customer trust.”
Shopify emphasizes that:
“PCI DSS compliance is a requirement for ecommerce stores that keep credit card information, handle any financial transactions, or accept payments using credit cards.”
Non-compliance risks fines or account closure. Key PCI DSS requirements include:
- Installing and maintaining firewalls
- Not using vendor-supplied passwords and security parameters
- Protecting stored cardholder data
- Encrypting transmission of cardholder data across public networks
- Using and regularly updating antivirus software
- Developing and maintaining secure systems and applications
- Restricting access to cardholder data
- Assigning unique IDs to each person with computer access
- Restricting physical access to cardholder data
- Tracking and monitoring all access to network resources
- Regularly testing security systems and processes
- Maintaining an information security policy
SSL/TLS Encryption
Secure Sockets Layer (SSL) and Transport Layer Security (TLS) encrypt data transmitted between customers and e-commerce websites. This encryption prevents MITM attacks from capturing payment information or credentials.
All e-commerce sites must use HTTPS with valid SSL/TLS certificates. Modern browsers warn customers about insecure sites, causing immediate trust loss and abandoned purchases.
Secure Payment Gateways
Payment gateways process transactions securely without exposing merchants to raw payment card data. Using reputable payment processors like Stripe, PayPal, or Square provides:
- PCI DSS-compliant payment processing
- Fraud detection and prevention
- Tokenization replaces card numbers with secure tokens
- 3D Secure authentication for additional verification
- Regular security updates and monitoring
Strong Authentication
Multi-factor authentication (MFA) protects administrative access to e-commerce platforms and customer accounts. Require MFA for:
- All administrative accounts
- Customer accounts (optional but recommended)
- Payment processing systems
- Database access
- Hosting and server management
Use strong password policies requiring complex passwords that change regularly.
Web Application Firewalls (WAF)
WAFs filter malicious traffic before it reaches e-commerce websites. They protect against:
- SQL injection attacks
- Cross-site scripting (XSS)
- DDoS attacks
- Malicious bots
- Credential stuffing
Cloud-based WAF services protect without requiring complex on-site infrastructure.
Regular Security Updates
Keep all software current, including:
- E-commerce platforms (Shopify, WooCommerce, Magento, etc.)
- Content management systems
- Plugins and extensions
- Server operating systems
- Database software
- Security tools
Outdated software contains known vulnerabilities that criminals actively exploit.
Security Monitoring and Logging
Implement continuous monitoring to detect suspicious activity:
- Failed login attempts indicate brute force attacks
- Unusual transaction patterns suggesting fraud
- Database queries indicating SQL injection attempts
- Traffic spikes indicating DDoS attacks
- File modifications suggesting compromise
Maintain detailed logs for forensic investigation if breaches occur.
Data Minimization
Only collect and store data you absolutely need. The less sensitive information you store, the less you can lose in breaches. According to ISMS.online’s compliance guide:
“Minimizing stored data reduces PCI DSS scope and risk.”
Never store full payment card numbers, CVV codes, or PINs. Use tokenization to replace sensitive data with non-sensitive equivalents.
Employee Training
Train all employees on security best practices:
- Recognizing phishing attempts
- Creating strong passwords
- Handling customer data securely
- Reporting suspicious activity
- Following security policies
Employees represent both the greatest vulnerability and strongest defense in e-commerce security.
Incident Response Planning
Develop plans for responding to security incidents, including:
- Containment procedures to limit damage
- Communication protocols for notifying customers and authorities
- Forensic investigation processes
- Recovery and restoration procedures
- Legal and regulatory compliance requirements
Test incident response plans regularly through tabletop exercises.
Regular Security Assessments
Conduct periodic security assessments, including:
- Vulnerability scans identify weaknesses
- Penetration testing simulating real attacks
- Code reviews find security flaws
- Compliance audits verifying regulatory adherence
- Third-party security audits provide independent validation
Source: PCI DSS Compliance 2025
Conclusion
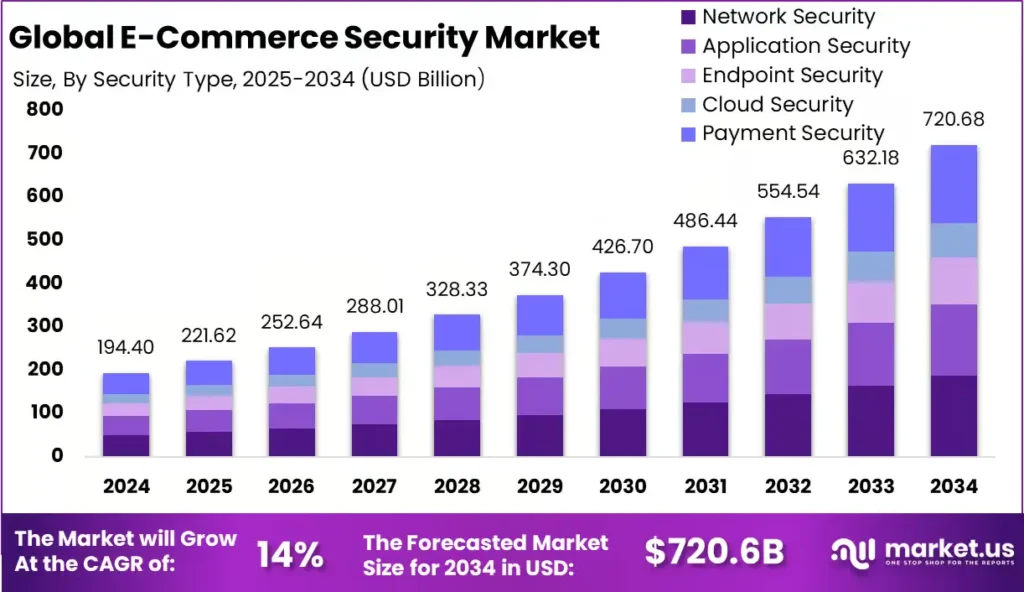
E-commerce cybersecurity is essential for protecting the billions of dollars flowing through online stores and safeguarding the personal and payment data of millions of customers. As cyber threats continue evolving in 2025, with increasingly sophisticated attacks leveraging AI and automation, merchants must implement comprehensive security measures to survive and thrive.
The foundation of e-commerce security rests on the CIA triad, maintaining confidentiality of sensitive data, ensuring integrity of transactions and information, and guaranteeing availability of online services. PCI DSS compliance provides the baseline security framework, but effective protection requires multiple layers, including encryption, secure payment processing, authentication, monitoring, and employee training.
The impact of security failures extends far beyond immediate financial losses. Customers suffer identity theft, financial fraud, and loss of privacy, while businesses face regulatory penalties, customer abandonment, reputation damage, and potential closure. These consequences make cybersecurity not just an IT concern but a fundamental business priority.
By implementing the basic protections outlined in this guide, PCI DSS compliance, SSL/TLS encryption, secure payment gateways, strong authentication, web application firewalls, regular updates, security monitoring, data minimization, employee training, incident response planning, and regular assessments, e-commerce merchants can significantly reduce their risk and protect both their businesses and their customers.
The investment in e-commerce cybersecurity pays dividends through maintained customer trust, avoided breach costs, regulatory compliance, competitive advantage, and sustainable business growth. In 2025’s increasingly dangerous cyber landscape, security is no longer optional—it’s the price of doing business online.
Glossary of E-commerce Security Terms
Account Takeover (ATO): Unauthorized access to customer accounts using stolen credentials
Chargeback: Customer dispute of credit card charges with their bank
CIA Triad: Confidentiality, Integrity, and Availability—core security principles
E-skimming: Malicious code capturing payment data from online checkout pages
Encryption: Converting data into a coded format, protecting it from unauthorized access
PCI DSS: Payment Card Industry Data Security Standard for securing card payments
Phishing: Fake communications tricking people into revealing sensitive information
SQL Injection: Exploiting database vulnerabilities to steal or modify data
SSL/TLS: Encryption protocols securing data transmission over networks
Tokenization: Replacing sensitive payment data with non-sensitive token equivalents
Web Application Firewall (WAF): A Security system that filters malicious web traffic
XSS (Cross-Site Scripting): Injecting malicious scripts into websites viewed by users
Frequently Asked Questions
What is E-commerce Cybersecurity?
E-commerce cybersecurity refers to the set of practices, technologies, and strategies used to protect online retail platforms, customer data, and financial transactions from cyber threats such as hacking, phishing, malware, and data breaches. It ensures a safe and trustworthy shopping experience for both businesses and customers.
Why is cybersecurity important for e-commerce businesses in 2025?
In 2025, as online shopping continues to expand and AI-driven systems handle sensitive data, cybersecurity has become more critical than ever. Strong protection safeguards your business from financial losses, protects customer trust, ensures compliance with data privacy laws, and prevents reputation damage caused by cyberattacks.
What are the most common cybersecurity threats to e-commerce websites?
The main threats include phishing scams, payment fraud, ransomware attacks, DDoS (Distributed Denial-of-Service) attacks, malware infections, and insider threats. Cybercriminals target weak payment gateways, unsecured databases, and outdated plugins to steal personal and financial data.
How can e-commerce websites enhance their cybersecurity in 2025?
To strengthen cybersecurity, businesses should:
Use SSL certificates and HTTPS for secure transactions
Implement two-factor authentication (2FA)
Regularly update software and plugins
Conduct frequent security audits and penetration testing
Use AI-based fraud detection systems
Educate employees and customers on cybersecurity awareness
What are the best cybersecurity tools for e-commerce protection in 2025?
Some top tools and solutions for 2025 include:
Cloudflare (DDoS and firewall protection)
Norton Small Business (endpoint protection)
Sucuri (website monitoring and malware removal)
Trustwave (PCI compliance and threat detection)
AI-driven fraud prevention tools like Forter or Riskified
