A complete 2025 guide to digital privacy. This guide covers key privacy risks, data protection laws, and effective steps to enhance your online safety
Digital privacy has become one of the most important concerns for anyone who uses the internet, smartphones, or digital services.
According to IEEE Digital Privacy:
“digital privacy serves as a shield that safeguards personal information from undue exposure and misuse.”
According to Privacy Savvy reports:
“when you go online, you leave digital footprints used by companies to track your behavior,”
Therefore, understanding digital privacy is essential for protecting yourself in today’s connected world. This comprehensive guide explains what digital privacy means, why it matters, what personal information is at risk, and how you can protect your online data protection rights.
Source: What Is Digital Privacy
Understanding Digital Privacy: The Complete Definition
Digital privacy refers to the right to control how your personal information is collected, used, stored, and shared when you use digital technologies and online services.
Winston & Strawn’s legal glossary defines online privacy as:
“the level of privacy protection an individual has while connected to the Internet. It covers the amount of online security available for personal and financial data, communications, and preferences.”
What Digital Privacy Really Means
At its core, digital privacy is about your ability to decide:
- What personal information you share online
- Who has access to your data
- How your information is used by companies and organizations
- When and how your data is deleted or retained
- Whether you remain anonymous or identifiable online
Wikipedia explains that:
“digital privacy is often used in contexts that promote advocacy on behalf of individual and consumer privacy rights in e-services and is typically used in opposition to the business practices of many e-marketers, businesses, and companies to collect and use such information.”
Three Categories of Online Privacy
According to IEEE’s digital age privacy analysis, digital privacy encompasses three interconnected categories:
Information Privacy protects your personal data including names, addresses, financial information, health records, and browsing history. This category focuses on controlling who accesses your data and how they use it.
Communication Privacy safeguards your digital communications including emails, messages, phone calls, video chats, and social media interactions. It ensures your conversations remain private and confidential.
Individual Privacy protects your right to control your online identity, reputation, and presence. This includes managing your digital footprint, controlling what information appears about you online, and maintaining anonymity when desired.
The Evolution of Privacy Meaning in Digital Age
Traditional privacy meant the right to be left alone, controlling physical access to your space and limiting who could observe your activities. Privacy Savvy notes that:
“in today’s digital age, this definition has evolved to encompass protecting personal data and preventing behavior tracking without explicit consent.”
Digital privacy now includes protecting data you actively share (like filling out forms), passively generate (like browsing history and location data), and data created about you by others (like photos, tags, and mentions). Every online action creates information that can be collected, analyzed, and used in ways you might not expect or want.
Source: Privacy Savvy – What Is Internet Privacy
What Is PII? Understanding Personal Identifiable Information
Personal Identifiable Information (PII) is any data that can identify you specifically or be combined with other information to identify you. Understanding what constitutes PII helps you recognize what information needs protection.
Direct Identifiers: Information That Identifies You Alone
Direct identifiers uniquely identify individuals by themselves:
- Full name
- Social Security number or national identification numbers
- Driver’s license numbers
- Passport numbers
- Biometric data (fingerprints, facial recognition, iris scans)
- Email addresses linked to real names
- Phone numbers
- Home addresses
- Bank account numbers and credit card numbers
These identifiers pose immediate privacy risks because they directly reveal your identity. Criminals seek this information for identity theft and fraud.
Indirect Identifiers: Information That Can Identify You When Combined
Indirect identifiers don’t identify you alone but can when combined with other data:
- Date and place of birth
- Employment information
- Education records
- IP addresses
- Device identifiers (MAC addresses, device IDs)
- Location data and GPS coordinates
- Browsing history and search queries
- Purchase history and transaction data
- Social media activity and connections
- Health and medical information
Modern data analytics can combine seemingly harmless indirect identifiers to identify specific individuals. For example, combining your zip code, birthdate, and gender can uniquely identify you in many populations.
Sensitive PII Requiring Extra Protection
Some PII is particularly sensitive and requires enhanced protection:
- Financial information (account numbers, credit scores, investment details)
- Health and medical records
- Genetic and biometric data
- Religious or political affiliations
- Sexual orientation and gender identity
- Criminal records and legal proceedings
- Children’s personal information
Laws like GDPR, HIPAA, and COPPA provide special protections for sensitive PII categories, recognizing the potential harm from unauthorized disclosure.
Source: Enzuzo – Digital Privacy Definition
Why Digital Privacy Matters: The Critical Importance
Digital privacy isn’t just an abstract concept—it has real, tangible impacts on your life, security, and freedom:
Protection from Identity Theft and Financial Fraud
Identity theft represents one of the most immediate privacy threats. When criminals access your PII, they can:
- Open credit accounts in your name
- File fraudulent tax returns to steal refunds
- Take out loans you’re responsible for repaying
- Access your existing financial accounts
- Commit crimes using your identity
- Ruin your credit score and financial reputation
Identity theft recovery takes years and costs thousands of dollars. Strong digital privacy practices prevent criminals from obtaining the information they need.
Safeguarding Financial Security
Your financial information requires robust privacy protection. Bank accounts, credit cards, investment accounts, and payment information must be secured from:
- Unauthorized transactions and theft
- Account takeovers
- Wire transfer fraud
- Credit card skimming
- Investment scams targeting your assets
Smowl’s privacy guide emphasizes that
“digital privacy is about respecting the rights of users and protecting their personal information from cybercrime or unauthorized use.”
Preventing Targeted Manipulation and Exploitation
Companies collect vast amounts of data about your behavior, preferences, and psychology. This information can be used to:
- Manipulate your purchasing decisions through personalized advertising
- Influence your political opinions with targeted content
- Exploit your vulnerabilities and emotional triggers
- Discriminate in pricing, services, or opportunities
- Create filter bubbles limiting information exposure
Understanding what companies know about you helps recognize when you’re being manipulated or targeted.
Protecting Personal Safety and Security
Digital privacy directly impacts physical safety. Exposed personal information can enable:
- Stalking and harassment through location tracking
- Home burglaries when vacation posts reveal empty houses
- Domestic violence escalation when abusers track victims
- Child exploitation when predators access children’s information
- Physical confrontations from online disputes
Controlling what information is public about you, especially location and routine data, protects physical safety.
Maintaining Professional Reputation and Opportunities
Your digital presence affects professional opportunities. Employers, clients, and business partners research you online. Privacy concerns include:
- Embarrassing photos or posts affecting hiring decisions
- Political or controversial opinions limiting opportunities
- Personal information used for discrimination
- Old content that doesn’t represent current views
- Private information affecting professional credibility
Managing your digital privacy helps control your professional reputation.
Preserving Freedom of Expression and Thought
Privacy enables free expression without fear of judgment, retaliation, or persecution. Without privacy:
- People self-censor to avoid judgment or consequences
- Unpopular opinions are suppressed
- Dissent and whistleblowing become dangerous
- Research into sensitive topics leaves permanent records
- Creative exploration is chilled by surveillance
Privacy provides the freedom to explore ideas, express opinions, and develop beliefs without constant monitoring.
Protecting Relationships and Personal Connections
Private communications foster genuine relationships. Without communication privacy:
- Intimate conversations can be exposed publicly
- Confidential disclosures can be weaponized
- Trust in relationships erodes
- Honest communication becomes risky
- Personal conflicts become public spectacles
Email, messaging, and social media privacy protections help maintain healthy relationships.
Exercising Autonomy and Personal Freedom
Fundamentally, privacy is about autonomy—the right to make choices about your life without undue influence or control. Digital privacy lets you:
- Browse and research freely without judgment
- Make purchasing decisions without manipulation
- Explore ideas without permanent records
- Change opinions without past views haunting you
- Control what others know about you
Privacy preserves human dignity and self-determination in an increasingly surveilled world.

Source: Robust Privacy Regulations
User Data Collection: What Companies Know About You
Understanding what data is collected helps you make informed privacy decisions:
Voluntary Information You Provide
You explicitly share information when you:
- Create accounts with usernames, emails, and passwords
- Fill out forms with addresses and phone numbers
- Upload photos, videos, and content
- Write posts, comments, and reviews
- Make purchases with payment information
- Complete surveys and questionnaires
- Contact customer support
While you control providing this information, terms of service often grant companies broad rights to use, analyze, and share your data.
Automatically Collected Technical Data
Websites and apps automatically collect technical information including:
- IP addresses revealing approximate location
- Device types, operating systems, and browsers
- Screen resolution and device specifications
- Language and timezone settings
- Referring websites and search terms
- Cookies tracking across sites
This technical data creates detailed profiles about your habits and preferences even without explicit information sharing.
Behavioral Data and Usage Patterns
Services track how you use them:
- Which pages you visit and how long you stay
- What content you engage with
- Products you view or add to carts
- Search queries revealing interests
- Video watching patterns
- Reading habits and article preferences
- Gaming behavior and achievements
This behavioral data reveals more about you than explicit information; your actions show your true interests and tendencies.
Location and Movement Data
Location tracking has become pervasive:
- GPS coordinates from mobile devices
- Wi-Fi and Bluetooth proximity tracking
- Cell tower triangulation
- IP address geolocation
- Location tags in photos and posts
- Check-ins and place reviews
Location data reveals where you live and work, where you shop and socialize, your daily routines, and even religious or political affiliations based on visited locations.
Social Connections and Relationship Data
Social platforms map your relationships:
- Friends, followers, and connections
- Family relationships and close contacts
- Professional networks and colleagues
- Groups and community memberships
- Interaction patterns showing closest relationships
- Influence and popularity metrics
This social graph data is valuable for advertisers and can be used to infer information about you based on your connections’ characteristics.
Inferred and Predicted Information
Companies use AI and machine learning to infer information you never explicitly provided:
- Demographic characteristics (age, gender, income)
- Interests and preferences
- Political and religious views
- Personality traits and psychological profiles
- Future behaviors and likely actions
- Purchasing propensity and price sensitivity
- Health conditions based on searches and purchases
These inferences can be inaccurate but affect the content you see and opportunities you receive.

Source: Digital Safety Guide 2025
Achieving Anonymity and User Data Protection
Protecting your digital privacy requires active measures:
Understanding True Anonymity vs. Pseudonymity
True anonymity means no one, including service providers, can identify you. Achieving true online anonymity is extremely difficult because:
- IP addresses link to internet service providers who know your identity
- Payment methods reveal identity
- Behavioral patterns can re-identify supposedly anonymous users
- Device fingerprints track across anonymization attempts
Pseudonymity means using fake names or handles while the service provider might know your real identity. This protects you from other users but not from companies or law enforcement.
Most online privacy measures provide pseudonymity or privacy from other users rather than true anonymity.
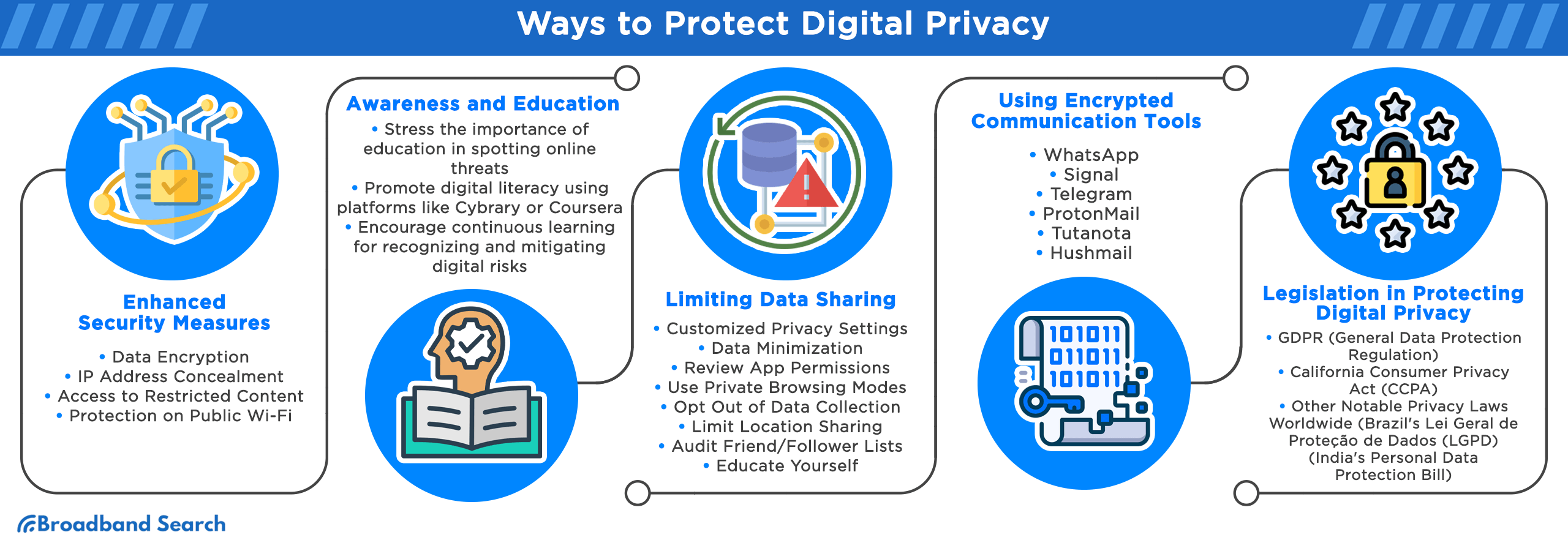
Practical Steps for Digital Privacy Protection
Use Strong, Unique Passwords: Create complex passwords for every account using password managers to store them securely. Never reuse passwords because one breach can compromise multiple accounts.
Enable Multi-Factor Authentication: Add extra security layers requiring multiple verification forms. Even if passwords are stolen, MFA prevents unauthorized access.
Review Privacy Settings: Regularly check privacy settings on social media, apps, and services. Default settings often prioritize data collection over privacy. Customize settings to minimize information sharing.
Limit Information Sharing: Only provide necessary information. Question why services need certain data and whether you’re comfortable sharing it. Less shared information means less exposure risk.
Use Privacy-Focused Tools: Choose services that prioritize privacy including encrypted messaging apps, privacy-focused browsers, VPNs hiding your IP address and encrypting traffic, and search engines that don’t track queries.
Be Selective with App Permissions: Review and limit app permissions on mobile devices. Apps often request unnecessary access to contacts, location, camera, and microphone. Deny permissions apps don’t legitimately need.
Clear Browsing Data Regularly: Delete cookies, browsing history, and cached data periodically. This limits tracking across websites and reduces stored personal information.
Use Email Aliases: Create separate email addresses for different purposes. This prevents data brokers from linking activities across services and reduces spam to primary addresses.
Read Privacy Policies: While lengthy and complex, privacy policies reveal how services use your data. Focus on sections about data sharing, retention, and your rights.
Exercise Data Rights: Many privacy laws grant rights to access your data, request corrections, delete information, and opt-out of certain uses. Exercise these rights when available.
Teaching Children About Digital Privacy
Children require special privacy protection and education:
- Supervise online activities and accounts
- Teach them never to share personal information online
- Use parental controls and kid-safe services
- Explain why privacy matters in age-appropriate terms
- Monitor who they communicate with online
- Set clear rules about acceptable online behavior
DLA Piper notes that
“in January 2025, the Federal Trade Commission (FTC) finalized significant changes to the federal Children’s Online Privacy Protection Act (COPPA), enhancing online safety for children.”
Conclusion
Digital privacy in 2025 means controlling how your personal information is collected, used, and shared across the vast digital landscape where every click, search, and interaction generates data. From understanding what PII is, including direct identifiers like Social Security numbers and indirect identifiers like browsing history, to recognizing why privacy matters for preventing identity theft, maintaining security, protecting freedom, and preserving autonomy, digital privacy affects every aspect of modern life.
Companies collect enormous amounts of user data including information you voluntarily provide, automatically gathered technical details, behavioral patterns, location tracking, social connections, and inferred characteristics. This comprehensive data collection enables targeted advertising, personalized services, and unfortunately, potential manipulation and exploitation.
Protecting your online privacy requires understanding that true anonymity is difficult to achieve, but practical measures significantly enhance privacy. Using strong passwords, enabling multi-factor authentication, reviewing privacy settings, limiting information sharing, choosing privacy-focused tools, controlling app permissions, clearing browsing data, and exercising data rights under privacy laws all contribute to better digital data protection.
Digital privacy isn’t just a technical or legal issue; it’s a fundamental human right that enables freedom of expression, protects personal safety, preserves professional opportunities, and maintains human dignity in an increasingly connected world. By understanding what digital privacy means and taking concrete steps to protect it, you can navigate the digital age while maintaining control over your personal information and online identity.
Frequently Asked Questions
What is digital privacy in 2025?
Digital privacy means controlling how your personal information is collected, used, and shared online. It protects your identity, data, and freedom from misuse, surveillance, and unauthorized tracking.
Why is digital privacy important?
Digital privacy protects you from identity theft, hacking, manipulation, and tracking. It ensures your personal data stays secure, maintains freedom of expression, and safeguards your financial and social information.
What personal information is at risk online?
How can I protect my digital privacy?
