Have you ever locked your front door before leaving home? Or maybe you’ve kept your wallet in a safe place?

Cybersecurity works similarly, but instead of protecting your house or wallet, it safeguards your computer, phone, and the information stored on them. Every day, malicious individuals attempt to steal information from computers and phones. They want your passwords, your bank details, and your personal photos.
According to Cybersecurity Ventures, these criminals are expected to cause damage worth $10.5 trillion by 2025. That’s more money than most countries have!
In this guide, you will learn everything about cybersecurity in simple words. You don’t need to be a computer expert. If you can use a smartphone or send an email, you should be able to understand this guide. By the end, you will know how to keep yourself safe online.
What Is Cybersecurity?
Cybersecurity is the practice of defending your digital assets from unauthorized access, attacks, damage, or theft. These digital assets include your computer systems, networks, programs, and data.
The goal of cybersecurity is to create a secure computing environment where you can work, communicate, and store information without worrying about criminals stealing or damaging your valuable data.
Here’s what cybersecurity protects:
- Your passwords and login information
- Your bank account and credit card details
- Your personal photos and videos
- Your emails and messages
- Your work documents and files
- Your social media accounts
According to the National University’s research, there are now approximately 4.7 million people worldwide who work in cybersecurity. That’s how important this has become! These experts help protect companies, governments, and regular people like you and me.
Think of cybersecurity like a shield. Just as a shield protects a knight from arrows and swords, cybersecurity protects you from digital attacks. The difference is that in the digital world, attacks can happen so quickly and quietly that you might not even notice them until it is too late.
Why Cybersecurity Matters in 2025?
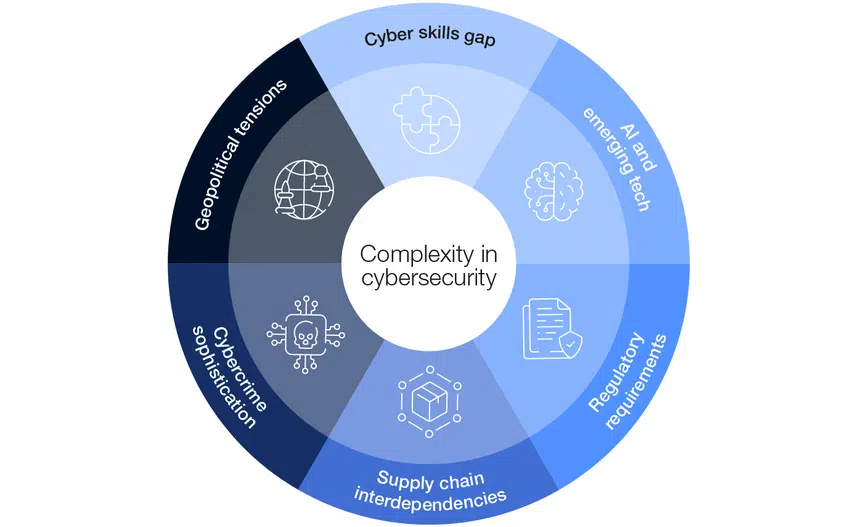
The importance of cybersecurity has reached unprecedented levels in 2025. According to Fortinet’s latest statistics, “66% of organizations expect AI to impact cybersecurity in 2025,” showing how the landscape continues to evolve with new technologies bringing both opportunities and threats.
Here’s why cybersecurity matters more than ever:
Financial Impact: The cost of cybercrime continues to skyrocket. Cobalt’s 2025 research reveals that “Worldwide cybercrime costs are estimated to hit $10.5 trillion annually by 2025.” This staggering figure surpasses the GDP of many countries, underscoring the substantial economic harm that cyberattacks inflict worldwide.
Increasing Attack Frequency: Astra Security’s data shows that “there are 2,200 cyber attacks per day, with a cyber attack happening every 39 seconds on average.” This constant barrage of attacks means that organizations and individuals must maintain 24/7 vigilance to protect their digital assets.
Data Breach Costs: In the United States, a single data breach now costs an average of $9.44 million, according to recent statistics. This enormous financial burden can destroy small businesses and significantly damage even large corporations’ bottom lines and reputations.
Remote Work Vulnerabilities: SentinelOne’s 2025 trends report explains that “With the global shift to telecommuting and flexible work arrangements, the potential attack surfaces have widened. The risks (phishing, endpoint compromise, and data exfiltration) are higher for employees accessing sensitive systems from home or public networks.”
Supply Chain Attacks: According to an analyst firm, Gartner, by 2025, 45% of global organizations are expected to be affected in some way by a supply chain attack, as analyzed by TechTarget.

Source: Viking Cloud – Cybersecurity Statistics
Different Ways to Protect Your Digital Life
Cybersecurity is not just one thing. There are many different ways to stay safe. Let me break them down in simple terms:
Protecting Your Internet Connection (Network Security)
Your internet connection is like the road that leads to your house. If the road is not protected, anyone can use it to reach you. Network security keeps that road safe.
This includes items such as your home Wi-Fi router. You need to put a strong password on it so that strangers can’t use your internet. It also contains firewalls, which act as security guards that monitor who comes in and out of your network.
When using public Wi-Fi at a coffee shop or airport, you need to be extra cautious. It is like leaving your house door open. Anyone nearby can see what you are doing online. That is why many people use a VPN (Virtual Private Network), which creates a private tunnel for their internet connection.
Protecting Your Apps and Software (Application Security)
Every app on your phone and every program on your computer can have weak spots that criminals can exploit. Application security refers to ensuring that these apps and programs are secure and safe to use.
Software companies regularly send you updates. These updates often fix security problems. When your phone or computer asks you to update, do not ignore it! Those updates can protect you from new threats.
Some apps ask for permissions to access your camera, location, or contacts. Always think before you say yes. Does a flashlight app really need to know your location? Probably not.
Protecting Information Stored Online (Cloud Security)
You probably use cloud services even if you’re not aware of it. When you save photos to Google Photos or iCloud, that is the cloud. When you use Dropbox or OneDrive for storing documents, that’s considered cloud storage as well.
Cloud security ensures that your information remains safe when stored on someone else’s servers. You should use strong passwords for these services and enable additional security features, such as two-factor authentication.
Think of cloud storage like a storage unit. You want to ensure the storage company has good security, but you also need to secure your own unit properly.
Protecting Your Devices (Endpoint Security)
Every device you own, such as your phone, laptop, tablet, or smartwatch, is referred to as an “endpoint.” Endpoint security refers to the protection of each device.
This includes installing antivirus software on your computer, keeping your phone’s operating system up to date, and exercising caution when downloading files. Each device is like a door to your digital life, and you need to put a lock on every door.
Many people make the mistake of only protecting their computer and forgetting about their phone. However, your phone likely contains more personal information than your computer does.
Protecting Your Personal Information (Data Security)
Your personal information, including your name, address, birthday, Social Security number, and bank details, is highly valuable. Criminals can use this information to steal your identity or your money.
Data security refers to the protection of this information. You should encrypt sensitive files (scrambling them so only you can read them), use password protection, and be very careful about who you share your information with.
Never send sensitive information, such as credit card numbers or passwords, through regular email. Email is like sending a postcard, which anyone along the way can read.
Controlling Who Can Access Your Accounts (Identity and Access Management)
Identity and Access Management, or IAM, is about ensuring that only authorized individuals can access your accounts and information. This is where passwords come in.
You should have a different password for every account. I know that sounds hard, but there are tools called password managers that can remember them all for you. These work like a secure notebook that only you can open.
You should also enable two-factor authentication (also known as 2FA or MFA) whenever possible. This means that even if someone steals your password, they still cannot access your account without a second form of verification, such as a code sent to your phone.
Never Trust, Always Verify (Zero Trust Security)
Zero trust is a new approach to security. In the old days, people thought,
“If you’re inside the building, you must be allowed to be here.”
Zero trust says
“I don’t care if you’re inside or outside—prove who you are every time.”
For you, this means being skeptical. Even if an email looks like it’s from your bank, verify it before clicking any links. Even if a text message appears to be from a family member, double-check if something seems suspicious.
This might sound paranoid, but in today’s world, it’s smart. Criminals are very good at pretending to be people you trust.
Common Cyber Threats You Need to Know
Now, let’s discuss what you are protecting yourself from. These are the most common dangers:
Malware (Bad Software)
Malware is short for “malicious software.” This refers to any program designed to harm your computer or steal your information. It’s like a digital virus that infects your device.
According to the Cyber Strategy Institute, malware in 2025 has become very smart. It can hide from antivirus programs and spread to other devices automatically.
You can get malware by downloading files from suspicious websites, clicking on bad links in emails, or even by visiting infected websites. Once it’s on your device, it can steal your passwords, watch what you type, or damage your files.
Ransomware (Digital Kidnapping)
Imagine if someone broke into your house, locked all your belongings in a safe, and demanded money to give you the key. That’s precisely what ransomware does to your computer files.
SentinelOne explains that ransomware locks your files by encrypting them. Then the criminals demand payment (usually in cryptocurrency) to unlock them. Even if you pay, there’s no guarantee they’ll give you the key.
University of San Diego reports that ransomware attacks are becoming more common and more sophisticated in 2025. They can affect individuals, but they often target businesses, hospitals, and schools because these organizations are more likely to pay.
Phishing (Digital Fishing for Your Information)
Phishing is when criminals pretend to be someone you trust to trick you into giving them your information. The name comes from “fishing” as they are fishing for your data.
You might receive an email that appears to be from your bank, requesting that you click a link to “verify your account.” Alternatively, you might receive a text message claiming to be from a delivery company, requesting that you confirm your address. These are traps.
Datamation found that phishing is now the number one cause of ransomware attacks in 2025. Criminals are using artificial intelligence to make their fake emails and messages look even more real.
The World Economic Forum warns that criminals are now using AI to create fake voice messages and even fake video calls. They can make it look and sound like your boss, family member, or friend is calling you.
DDoS Attacks (Digital Traffic Jams)
DDoS stands for “Distributed Denial of Service.” This occurs when criminals flood a website with so much fake traffic that legitimate users are unable to access it. It is as if someone sent thousands of cars to block your street, so you cannot leave your house.
For most individuals, you will not be targeted by DDoS attacks, which usually target businesses and websites. However, it is beneficial to be aware of them because they can prevent you from accessing the services you need.
Social Engineering (Tricking Your Brain)
Social engineering occurs when criminals manipulate individuals into violating security protocols. They do not attack your computer; they attack your emotions and psychology.
For instance, a criminal might call you pretending to be from tech support, saying your computer has a virus. They sound professional and create a sense of urgency. Before you know it, you have given them remote access to your computer.
Or someone might send you an email saying you have won a prize, but you need to pay a small “processing fee” first. They play on your excitement to trick you. These attacks work because humans naturally want to be helpful and trusting. Criminals take advantage of these good qualities.
Insider Threats (Danger from the Inside)
Sometimes the danger comes from people who already have access to your information. This could be an angry employee at a company, a family member who knows your passwords, or a friend who accidentally shares your information.
Insider threats are a big concern in the workplace. But even at home, you should be careful about who has access to your devices and accounts.
Advanced Persistent Threats (Long-Term Spying)
APT is when sophisticated criminals (often working for governments or organized crime) sneak into a network and stay hidden for months or even years, slowly stealing information.
For most individuals, this is not a concern. But if you work for a government agency, military contractor, or company with valuable secrets, you should be aware that these threats exist.
Zero-Day Vulnerabilities (Unknown Weaknesses)
Sometimes, software has security problems that even the company that created it is unaware of. These are called zero-day vulnerabilities because there have been “zero days” to fix them.
When criminals discover these weaknesses before the company does, they can exploit them before any protection is available. This is why keeping your software up to date is so essential. Updates often fix these vulnerabilities after they’re discovered.
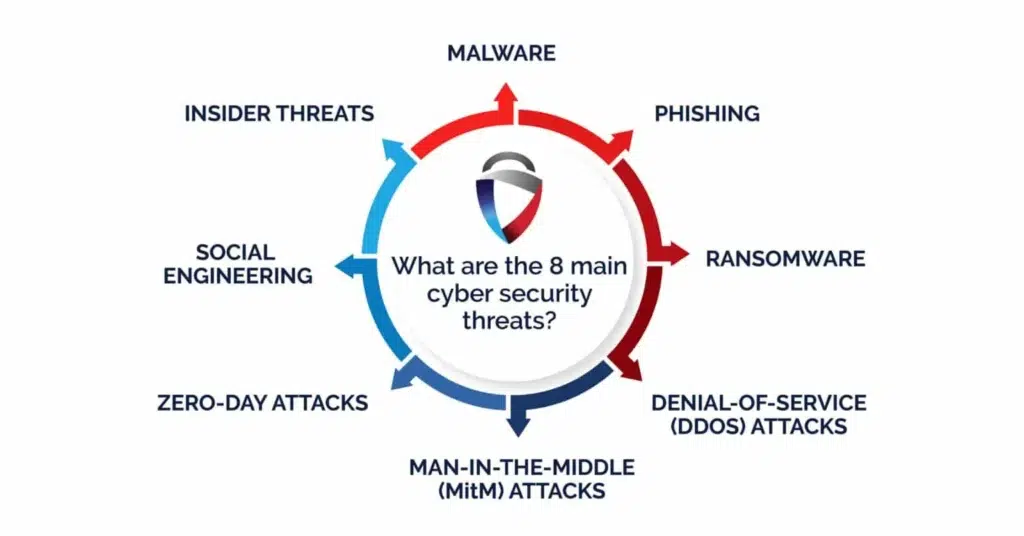
Source: fortifydata-Cyber Threats Guide
Essential Cybersecurity Tools and Defenses
Protecting yourself from cyber threats requires multiple layers of defense. Here are the essential tools and practices:
Firewalls
Firewalls act as barriers between your trusted internal network and untrusted external networks, such as the Internet. They monitor and control incoming and outgoing network traffic based on predetermined security rules, blocking potentially harmful traffic while allowing legitimate communications to pass through.
Encryption
Encryption converts your data into a coded format that can only be read by someone who has the decryption key. This protects your sensitive information even if attackers intercept it during transmission or steal it from storage.
Multi-Factor Authentication (MFA)
MFA adds extra layers of security by requiring users to provide two or more verification factors to gain access to an account or system. This typically includes something you know (such as a password), something you have (like a phone or security token), and something you are (like a fingerprint or facial recognition).
Antivirus and Anti-Malware Software
These programs scan your systems for known malware signatures and suspicious behaviors, blocking or removing threats before they can cause damage. Modern solutions utilize artificial intelligence and machine learning to identify new, previously unknown threats.
Security Information and Event Management (SIEM)
SIEM systems collect and analyze security-related data from across your network in real-time, helping security teams detect and respond to potential threats quickly. They provide a centralized view of your organization’s security posture.
Penetration Testing and Ethical Hacking
Penetration testing involves hiring security professionals to attempt to break into your systems using the same techniques that real attackers would use. This helps identify vulnerabilities before malicious hackers can exploit them.
Regular Software Updates and Patch Management
Keeping your software up to date is one of the simplest yet most effective security measures. Updates often include patches for security vulnerabilities that hackers could exploit.
Key Cybersecurity Frameworks and Standards
Organizations use established frameworks to structure their cybersecurity programs. Here are the most important ones:
NIST Cybersecurity Framework
Developed by the National Institute of Standards and Technology, this framework provides a policy framework of computer security guidance for how private sector organizations can assess and enhance their ability to prevent, detect, and respond to cyberattacks.
ISO/IEC 27001
This international standard specifies requirements for establishing, implementing, maintaining, and continually improving an information security management system. Organizations can get certified to demonstrate their commitment to information security.
CIS Controls
The Center for Internet Security Controls provides a prioritized set of actions that collectively form a defense-in-depth set of best practices to mitigate the most prevalent cyber attacks.
PCI DSS
The Payment Card Industry Data Security Standard is mandatory for any organization that handles credit card information. It includes requirements for security management, policies, procedures, network architecture, and software design.
SOC 2
Service Organization Control 2 is an auditing procedure that ensures service providers securely manage data to protect the interests of their clients and the privacy of their clients’ customers.
Important Cybersecurity Laws and Regulations
Governments worldwide have enacted cybersecurity regulations to protect citizens and organizations. Here are the key regulations by region:
North America
HIPAA (Health Insurance Portability and Accountability Act) protects sensitive patient health information in the United States. Healthcare providers, insurers, and their business associates are required to comply with stringent security and privacy standards.
CCPA (California Consumer Privacy Act) gives California residents rights over their personal information, including the right to know what data is collected, the right to delete data, and the right to opt out of data sales.
PIPEDA (Personal Information Protection and Electronic Documents Act) governs how private sector organizations in Canada collect, use, and disclose personal information.
Europe
The GDPR (General Data Protection Regulation) is one of the world’s strictest laws regarding privacy and data security. It applies to any organization operating in the EU or handling data of EU citizens, with penalties of up to 4% of the organization’s annual global revenue.
NIS2 Directive strengthens cybersecurity requirements across the European Union, expanding the scope of organizations that must comply with security measures and incident reporting requirements.
Asia
The China Cybersecurity Law (CSL) requires network operators to store select data within China and permits Chinese authorities to conduct spot checks on network operations.
India DPDP Act 2023 (Digital Personal Data Protection Act) establishes comprehensive data protection rules for Indian citizens’ personal information.
Japan APPI (Act on the Protection of Personal Information) regulates how organizations handle personal information in Japan.
Other Regions
LGPD (Brazil) – Brazil’s general data protection law modeled after GDPR
POPIA (South Africa) – Protection of Personal Information Act
Privacy Act 1988 (Australia) – Regulates handling of personal information
Source: World Economic Forum-Cybersecurity Regulations
Cybersecurity Best Practices for Everyone
You don’t need to be a cybersecurity expert to protect yourself. Here are practical steps anyone can take:
Create Strong, Unique Passwords
Use passwords that are at least 12 characters long and include a mix of uppercase letters, lowercase letters, numbers, and symbols. Never reuse passwords across different accounts. Consider using a password manager to store and generate strong passwords.
Enable Multi-Factor Authentication
Turn on MFA wherever it is available, especially for email, banking, and social media accounts. This adds an extra layer of protection even if someone steals your password.
Keep Software Updated
Install updates promptly when they become available. Enable automatic updates for your operating system, applications, and security software to ensure you are always protected against the latest known vulnerabilities.
Be Skeptical of Emails and Messages
Do not click on links or download attachments from unknown senders. Be suspicious of urgent requests for personal information or money, even if they appear to come from legitimate sources. When in doubt, contact the organization directly using a phone number or website you find independently.
Back Up Your Data Regularly
Maintain regular backups of important files to an external hard drive or cloud service. This protects you from data loss due to ransomware, hardware failure, or accidents.
Use Secure Networks
Avoid accessing sensitive information over public Wi-Fi networks. If you must use public Wi-Fi, use a VPN to encrypt your connection. At home, secure your Wi-Fi router with a strong password and WPA3 encryption.
Limit Information Sharing
Be careful about what personal information you share on social media and other online platforms. Cybercriminals can use this information for identity theft or to craft convincing phishing attacks.
Practice Good Mobile Security
Install apps only from official app stores, review app permissions carefully, and keep your mobile operating system up to date. Use device encryption and remote wipe capabilities in case your phone is lost or stolen.
Cybersecurity Careers and Opportunities
The cybersecurity field offers excellent career opportunities with strong growth prospects. According to the National University, the global cybersecurity workforce has reached 4.7 million professionals; however, a significant skills gap remains, with many positions still unfilled.
Popular Cybersecurity Roles
- Security Analyst: Monitors networks for security breaches and investigates when they occur
- Penetration Tester: Tests systems by attempting to break into them to find vulnerabilities
- Security Architect: Designs robust security structures for organizations
- Chief Information Security Officer (CISO): Executive-level position overseeing all aspects of information security
- Incident Responder: Handles security breaches and cyber attacks when they occur
- Security Engineer: Builds and maintains security systems and tools
Valuable Certifications
- CompTIA Security+: Entry-level certification covering basic security concepts
- Certified Ethical Hacker (CEH): Focuses on penetration testing and ethical hacking skills
- CISSP (Certified Information Systems Security Professional): Advanced certification for experienced security professionals
- CISM (Certified Information Security Manager): For those in management roles
- GIAC Certifications: Specialized certifications in various security domains
Career Outlook
The demand for cybersecurity professionals continues to outpace supply, making it an excellent field for job security and competitive salaries. Entry-level positions often start at $60,000-$80,000 annually, with experienced professionals earning well over $100,000. Executive-level positions, such as CISO, can command salaries exceeding $200,000.
The Future of Cybersecurity
The cybersecurity landscape continues to evolve rapidly. Here are key trends shaping the future:
Artificial Intelligence in Security
AI and machine learning are revolutionizing both cyber attacks and defenses. According to the World Economic Forum’s 2025 report, “66% of organizations expect AI to impact cybersecurity in 2025. However, only 37% have processes to assess AI tool security before deployment.”
AI helps security teams detect anomalies, predict threats, and respond more quickly than humans can. However, attackers also use AI to create more sophisticated and convincing attacks.
Quantum Computing Threats
Quantum computers, when they become practical, could render current encryption methods obsolete, necessitating entirely new approaches to cryptography. Organizations are already preparing for this “quantum threat” by developing quantum-resistant encryption algorithms.
IoT Security Challenges
The Internet of Things continues to expand, with billions of connected devices from smart home appliances to industrial sensors. Each device represents a potential entry point for attackers, making IoT security increasingly critical.
DevSecOps Integration
Organizations are integrating security into every stage of the software development lifecycle rather than treating it as an afterthought. This DevSecOps approach helps catch vulnerabilities early when they’re easier and cheaper to fix.
Privacy-Enhancing Technologies
As privacy regulations become increasingly stringent globally, technologies that enable data analysis while protecting individual privacy, such as differential privacy and homomorphic encryption, are gaining importance.
Conclusion
Cybersecurity might have seemed complicated when you started reading this guide, but now you understand the basics. You know what threats exist, how to protect yourself, and why it matters. The internet is a fantastic tool that connects us, educates us, and entertains us. But like anything valuable, it needs to be protected. You would not leave your car unlocked with the keys inside, and you should not leave your digital life unprotected either.
The good news is that you do not need to be a tech expert to stay safe. To remain secure, follow these guidelines: use strong passwords, keep your software up to date, think before you click, and back up your important files. Cybersecurity is everyone’s responsibility. By protecting yourself, you also protect your family, friends, and coworkers. When we all take security seriously, the internet becomes safer for everyone.
Start with one small change today. Perhaps it’s as simple as updating your phone, changing a weak password, or enabling two-factor authentication. Then tomorrow, make another small change. Before you know it, you’ll have built strong defenses that will keep you safe for years to come.
Frequently Asked Questions
What is cybersecurity in simple terms?
Cybersecurity is the practice of protecting computers, servers, mobile devices, networks, and data from malicious attacks, unauthorized access, or damage. It’s like having locks and alarms for your digital property.
Why is cybersecurity important?
Cybersecurity is critical because cyber attacks can result in financial losses, identity theft, privacy violations, and operational disruptions. With cybercrime costs projected to reach $10.5 trillion by 2025, protecting digital assets has become essential for everyone.
What are the main types of cybersecurity threats?
The main threats include malware, ransomware, phishing, DDoS attacks, social engineering, insider threats, and zero-day vulnerabilities. Each requires different defense strategies.
How can I protect myself from cyber attacks?
Use strong, unique passwords, enable multi-factor authentication, keep software up to date, be cautious with emails and links, back up data regularly, use secure networks, and limit the personal information you share online.
What are the best cybersecurity certifications?
Top certifications include CompTIA Security+ (entry-level), CEH (Certified Ethical Hacker), CISSP (for experienced professionals), and specialized GIAC certifications. Choose based on your career goals and experience level.
How much do cybersecurity professionals earn?
Entry-level positions typically start at $60,000-$80,000 annually, while experienced professionals earn $ 100,000 or more, and executive-level roles, such as CISO, can exceed $200,000. Salaries vary by location, experience, and specialization.
What is the difference between cybersecurity and information security?
The terms are often used interchangeably, but technically, information security protects all information (digital and physical), while cybersecurity protects explicitly digital information and systems connected to networks.
