Cybercrime has become one of the biggest threats in our digital world. Learn what cybercrime is, its main types, and simple ways to stay safe online in this beginner’s guide.

According to Britannica, Cybercrime is:
“The use of a computer as an instrument to further illegal ends, such as committing fraud, trafficking in child pornography and intellectual property, stealing identities, or violating privacy.”
With cybercrime costs projected to reach $23.82 trillion annually by 2027, understanding this threat is essential for everyone.
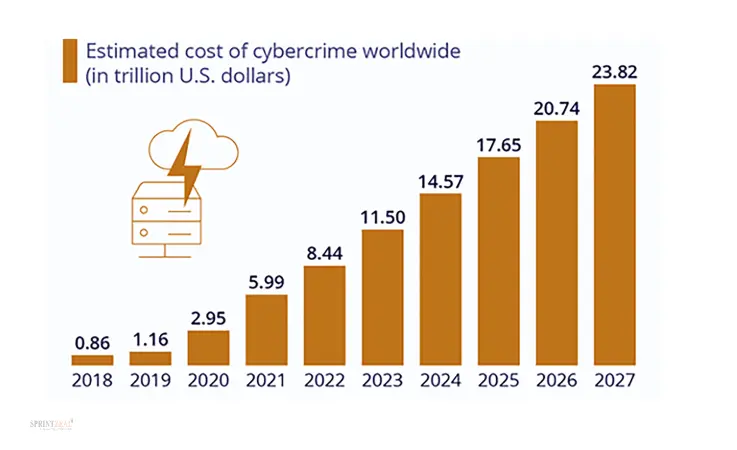
Source: Estimated Cost of Cybercrime
This guide explains what cybercrime is, the different types you should know about, how it affects businesses, and, most importantly, how you can protect yourself from becoming a victim.
What Makes Cybercrime Different
Cybercrime is a criminal activity that involves computers, networks, or digital devices. What makes cybercrime different from traditional crime is not just the use of technology; it is how criminals can commit crimes across borders, hide their identities easily, and target thousands of victims simultaneously.
According to Britannica:
“Cybercrime highlights the centrality of networked computers in our lives, as well as the fragility of such seemingly solid facts as individual identity.”
In the digital age, our virtual identities, the collection of data about us stored in multiple databases, have become targets for criminals.
The challenge with cybercrime is its non-local character. A criminal in one country can attack victims in another country, making it difficult for law enforcement to investigate and prosecute. This is why international cooperation through treaties like the Council of Europe Convention on Cybercrime, which came into effect in 2004, has become necessary.
The CIA Triad: What Criminals Attack
When cybercriminals attack, they typically target one or more elements of the ‘CIA Triad’. The CIA Triad is a fundamental model for information security consisting of three core principles:
Confidentiality is about keeping information private. Criminals break confidentiality when they steal passwords, hack accounts, or access private data without permission.
Integrity means keeping information accurate and unaltered. Criminals attack integrity when they change data in databases, modify financial records, or tamper with medical information.
Availability ensures that systems and data are accessible when needed. Criminals attack availability through ransomware that locks files or DDoS attacks that shut down websites.
It serves as a foundational framework for developing and evaluating security policies by ensuring data is protected from unauthorized access, remains accurate and consistent, and is accessible to authorized users when needed. Understanding these concepts helps you see what cybercriminals are trying to achieve and how to defend against their attacks.
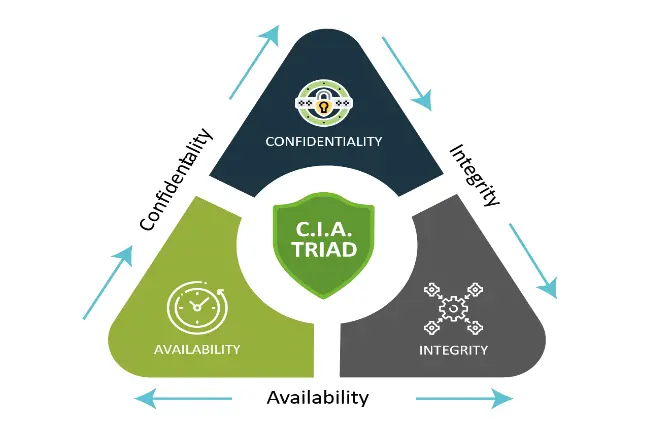
Source: CIA Triad
Types of Cyber Crime
According to Britannica’s classification:
“Cybercrime ranges across a spectrum of activities.”
Let’s examine the major types:
Privacy Breaches and Data Theft
At one end of the spectrum are crimes involving breaches of personal or corporate privacy. These include assaults on the integrity of information held in digital databases and using illegally obtained information to blackmail or harm individuals and companies.
Identity theft has become one of the fastest-growing cybercrimes. The FBI’s Internet Crime Complaint Center reports:
“Identity theft causes billions in losses annually.”
Criminals steal personal information like social security numbers, birth dates, and financial data to open fraudulent accounts, file fake tax returns, or commit crimes in someone else’s name.
Data breaches expose millions of customer records containing sensitive information. When companies get hacked, criminals steal names, addresses, credit card numbers, and passwords. This stolen data gets sold on dark web marketplaces where other criminals buy it to commit fraud.
Malware: Malicious Software Attacks
Malware is software specifically designed to damage or gain unauthorized access to computer systems. Huntress found that:
“54% of people reported experiencing malware infections in the past year, making it the most common cybercrime.”
Viruses attach to legitimate programs and spread when users run those programs. They can delete files, corrupt data, or steal information.
Trojans disguise themselves as useful software but contain hidden malicious code. Once installed, they give criminals remote access to your computer.
Spyware secretly monitors everything you do, recording keystrokes to capture passwords, tracking websites visited, and sending this information back to criminals.
Ransomware encrypts your files and demands payment for the decryption key. According to Astra:
“Ransomware costs are predicted to reach $265 billion by 2031.”
Phishing: Social Engineering Attacks
Phishing uses deception rather than technical exploits. Criminals send fake emails or messages that appear to come from trusted sources like banks, government agencies, or popular companies. Keepnet’s 2025 research shows:
“Phishing scams using AI to generate convincing emails have led to a spike in identity theft and financial fraud.”
When you click links in phishing messages, you’re taken to fake websites that look real. If you enter your username and password, criminals capture this information and use it to access your real accounts.
Spear-Phishing targets specific individuals with personalized messages based on information gathered from social media. It also includes:
Transaction-Based Crimes
According to Britannica:
“Midway along the spectrum lie transaction-based crimes such as fraud, trafficking in child pornography, digital piracy, money laundering, and counterfeiting.”
These crimes have specific victims, but criminals hide behind the internet’s anonymity.
Business Email Compromise (BEC) has become particularly costly. University of San Diego explains:
“Criminals hack or impersonate business email accounts to trick companies into transferring money.”
The FBI reports that BEC causes billions in losses because criminals carefully study how companies operate before striking.
Online fraud includes fake shopping websites, investment scams, romance scams, and cryptocurrency fraud. Criminals create convincing fake websites or profiles to steal money from unsuspecting victims.
Infrastructure Attacks
According to Britannica:
“At the far end of the spectrum are crimes that involve attempts to disrupt the actual workings of the Internet.”
These include:
Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks overwhelm websites or services with traffic, making them unavailable to legitimate users. Criminals use networks of infected computers called botnets to launch massive attacks.
Hacking involves unauthorized access to computer systems to steal data, install malware, or cause damage. Some hackers work for criminal organizations, while others are state-sponsored actors conducting cyber espionage.
Cyberterrorism uses the internet to cause public disturbances, disrupt critical infrastructure, or even cause death. Britannica explains that:
“Cyberterrorism focuses upon the use of the Internet by nonstate actors to affect a nation’s economic and technological infrastructure.”
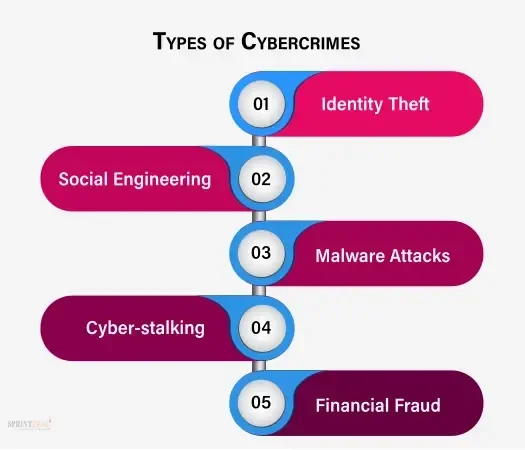
Source: Cybercrime Types
Common Cybercrime Targets
Understanding real-world attacks helps you recognize threats:
Healthcare Data Breaches
Hospitals and healthcare providers have become prime targets because medical records contain complete personal information, names, addresses, social security numbers, insurance details, and medical history. This data sells for high prices on criminal marketplaces. Recent attacks have forced hospitals to shut down systems, cancel appointments, and revert to paper records.
Ransomware Against Businesses
The Cl0p ransomware group attacked multinational corporations by exploiting vulnerabilities in file transfer software. Victims faced both data encryption and threats to publish stolen data publicly, a double extortion tactic that increases pressure to pay ransoms.
Social Media Account Hijacking
High-profile social media account takeovers have been used for cryptocurrency scams, spreading misinformation, and manipulating markets. When criminals hack verified accounts, their messages reach millions of followers who trust the account’s authenticity.
Government and Critical Infrastructure Attacks
State-sponsored hackers have targeted government agencies, power grids, water treatment facilities, and other critical infrastructure. These attacks can disrupt essential services and threaten public safety.
How Cybercrime Affects Businesses
Businesses face devastating consequences from cybercrime:
Financial Losses
Bright Defense reports that:
“The average cost of a data breach reached $4.88 million globally in 2024.”
These costs include immediate theft, ransom payments, investigation expenses, legal fees, regulatory fines, customer notification, lost business during downtime, and increased insurance premiums.
Operational Disruption
Cyber attacks can completely shut down business operations. Manufacturing stops, stores can’t process sales, hospitals cancel surgeries, and schools close. Every hour of downtime costs money and damages customer relationships.
Reputation Damage
When customers learn their data was stolen, they lose trust. This reputation damage can exceed immediate financial losses. Customers leave for competitors, partnerships end, and investors lose confidence. Some businesses never recover.
Legal Consequences
Companies face lawsuits from affected customers, regulatory investigations, and substantial fines for failing to protect data adequately. In some cases, officers and directors face personal liability.
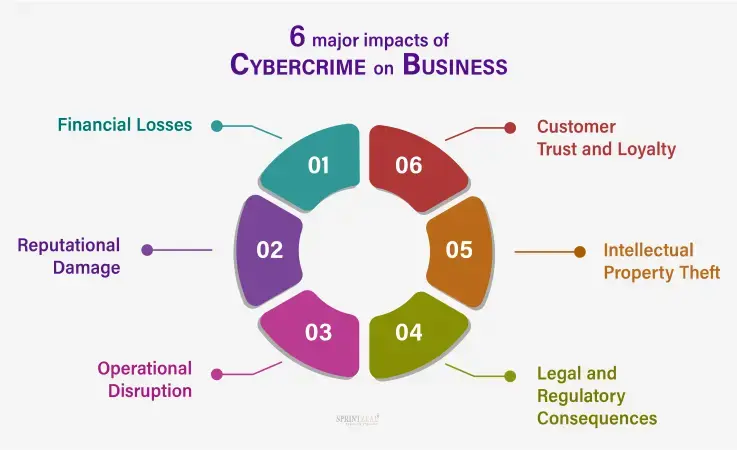
Source: Cybercrime On Business
Laws and Reporting Cybercrime
Governments around the globe have drafted several laws along with their reporting mechanism to combat cybercrime:
Major Cybercrime Laws
United States: The Computer Fraud and Abuse Act (CFAA) criminalizes unauthorized computer access. The Identity Theft and Assumption Deterrence Act specifically addresses identity theft. Each state has additional laws.
International: The Council of Europe Convention on Cybercrime helps countries cooperate in fighting cybercrime across borders. The convention came into effect in 2004 and has been ratified by over 60 countries.
Other Countries: The EU has comprehensive data protection and cybersecurity regulations. China, India, Singapore, and many other countries have robust cybercrime laws with severe penalties.
How to Report Cybercrime
In the United States, a cybercrime is reported to the:
FBI’s Internet Crime Complaint Center (IC3) at ic3.gov
Federal Trade Commission at IdentityTheft.gov for identity theft
- Your local police department for immediate threats
How to Protect Yourself from Cybercrime
You can significantly reduce your risk with these precautionary measures:
Strong Authentication
Use passwords that are at least 12 characters with uppercase, lowercase, numbers, and symbols. Never reuse passwords. Enable multi-factor authentication (MFA) on all important accounts, email, banking, and social media.
Keep Software Updated
Install updates immediately when available. Updates include security patches that fix vulnerabilities that criminals exploit. Enable automatic updates for your operating system, applications, and security software.
Be Skeptical of Messages
Before clicking links in emails or messages, verify the sender’s address, check for urgency or threats, look for grammar mistakes, and hover over links to see actual URLs. When in doubt, go directly to the company’s website by typing the address yourself.
Secure Your Network
Use strong passwords on your home Wi-Fi router with WPA3 or WPA2 encryption. Avoid sensitive transactions on public Wi-Fi. If you must use public networks, use a Virtual Private Network (VPN) to encrypt your connection.
Back Up Your Data
Regularly back up important files to an external hard drive or cloud service. Follow the 3-2-1 rule: three copies of data, on two different media types, with one copy off-site. Test backups to ensure they work.
Use Security Software
Install reputable antivirus and anti-malware software on all devices. Keep it updated and run regular scans. Modern security software uses AI to detect new threats.
Monitor Your Accounts
Check bank accounts, credit cards, and credit reports regularly for suspicious activity. Set up alerts for transactions. Review credit reports annually from all the major bureaus.
Educate Yourself
Stay informed about new cyber threats and scams. Criminals constantly develop new techniques. Also, share what you learn with family and friends to protect them.
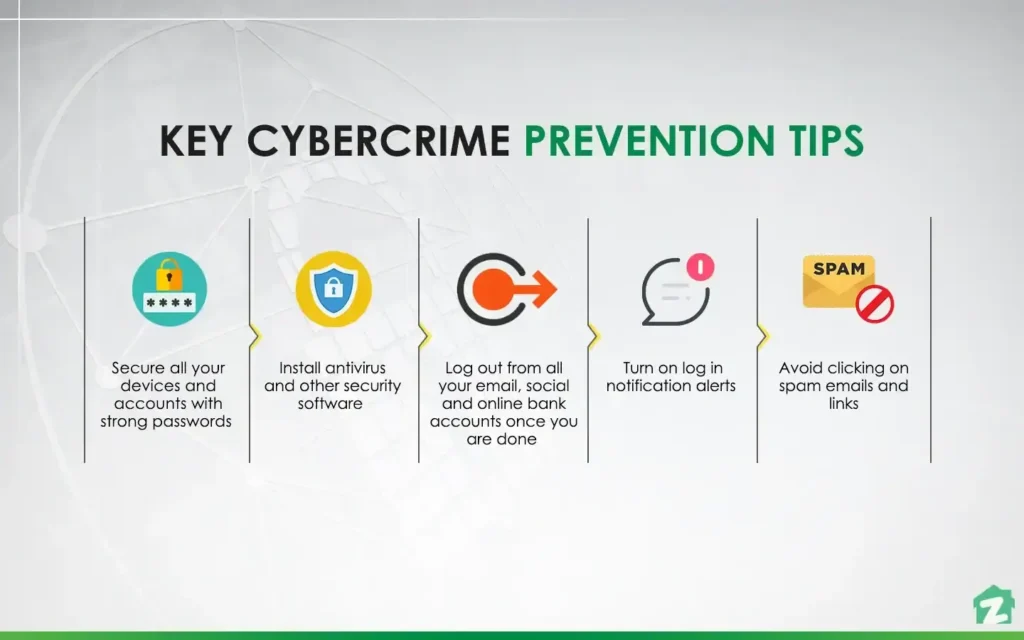
Source: Cybercrime Prevention Tips
Conclusion
Cybercrime represents a serious and growing threat in our increasingly digital world. With costs reaching trillions of dollars annually, understanding cybercrime is essential for protecting yourself and your organization.
Remember that cybercriminals are sophisticated and constantly evolving. The phishing email that looks fake today might be incredibly convincing tomorrow. Ransomware attacks that once targeted only large corporations now affect small businesses and individuals.
However, you do not need to be a cybersecurity expert to protect yourself. Follow basic practices like using strong authentication, keeping software updated, being skeptical of unexpected messages, backing up your data, and educating yourself about current threats. These simple steps block most cyber attacks because criminals target easy victims first.
If you become a victim, report the crime to the appropriate authorities immediately and take steps to limit damage. The fight against cybercrime requires everyone’s participation. When you protect yourself, you help protect others by not becoming a link in the chain criminals use to spread attacks.
Stay vigilant, stay informed, and take cybersecurity seriously. Your digital safety depends on the actions you take today.
Glossary of Cyber Crime Terms
Botnet: A Network of infected computers controlled by criminals to launch attacks
CIA Triad: Confidentiality, Integrity, and Availability, the three core security principles
Cybercriminal: A Person who commits crimes using computers and networks
DDoS: Distributed Denial of Service attack that overwhelms systems with traffic
Encryption: Converting data into a coded format to protect confidentiality
Hacker: A Person who gains unauthorized access to computer systems
Identity Theft: Stealing personal information to impersonate victims
Malware: Malicious software designed to damage systems or steal data
Phishing: Fake messages that trick people into revealing sensitive information
Ransomware: Malware that encrypts files and demands payment for decryption
Social Engineering: Manipulating people into breaking security procedures
Trojan: Malware disguised as legitimate software
Virus: Self-replicating malware that spreads through infected files
VPN: Virtual Private Network that encrypts internet connections
Zero-Day: Previously unknown vulnerability with no available patch
Frequently Asked Questions
What is cybercrime?
What are common types of cybercrime?
Common types include phishing, ransomware, data theft, online fraud, and hacking into personal or business accounts.
Why is cybercrime increasing?
Cybercrime is rising because more people use the internet for shopping, banking, and communication, giving criminals more opportunities to exploit users.
How can I protect myself from cybercrime?
Use strong passwords, update software regularly, avoid suspicious links or emails, and use trusted antivirus and security tools.
What should I do if I become a victim of cybercrime?
Report the incident to your local cybercrime authorities, change your passwords, and secure your accounts immediately.
