The global cybersecurity legal landscape has undergone transformative changes in 2025, with governments worldwide implementing comprehensive frameworks to address escalating digital threats.

Cybersecurity laws represent the legal frameworks that govern how organizations and individuals must protect digital assets, respond to cyber incidents, and maintain the confidentiality, integrity, and availability of information systems. These laws establish mandatory obligations for reporting breaches, implementing security controls, and establishing accountability mechanisms that span across borders and jurisdictions.
This comprehensive guide examines cybersecurity laws from a global perspective, providing both novice readers and experienced professionals with detailed insights into regulatory requirements, compliance obligations, enforcement mechanisms, and emerging trends shaping the 2025 cybersecurity legal landscape.
According to Cloud Security Alliance, as of June 30, 2025, only 14 EU Member States have fully transposed NIS2 into national law, highlighting the ongoing evolution of cybersecurity legislation globally.

Source: Cloud Security Alliance – EU Compliance Update
What Are Cybersecurity Laws? Foundational Principles
Cybersecurity laws constitute statutory and regulatory frameworks designed to protect information systems, networks, and data from unauthorized access, disclosure, disruption, modification, or destruction. Unlike privacy laws that primarily focus on personal data protection, cybersecurity laws address the broader technical and organizational measures required to maintain system security and operational resilience.
The CIA Triad: Core Legal Objectives
The fundamental principles underlying cybersecurity laws rest on the CIA triad:
- Confidentiality ensures that information remains accessible only to authorized individuals and entities. Legal frameworks require access controls, encryption, and authentication mechanisms to prevent the unauthorized disclosure of sensitive data.
- Integrity guarantees that information and systems remain accurate, complete, and unaltered except through authorized processes. Laws require organizations to implement change management procedures, audit trails, and verification mechanisms to detect and prevent unauthorized modifications.
- Availability ensures that information systems remain accessible to authorized users when needed. Regulatory frameworks mandate business continuity planning, disaster recovery capabilities, and resilience measures to maintain operational continuity during and after cyber incidents.
Distinguishing Laws, Regulations, and Standards
Understanding the hierarchical structure of cybersecurity requirements proves essential for compliance:
- Laws represent legislative acts passed by governmental bodies that establish broad legal obligations and penalties. Examples include the Computer Fraud and Abuse Act (CFAA) in the United States or the Network and Information Security Directive (NIS2) in the European Union.
- Regulations constitute detailed rules issued by administrative agencies to implement statutory requirements. These provide specific technical and procedural requirements that organizations must follow, often with more granular specifications than the underlying laws.
- Standards represent voluntary technical specifications and best practices developed by industry bodies or standards organizations. While not legally binding themselves, standards like ISO 27001 often become mandatory through their incorporation into regulatory requirements.
Compliance obligations emerge from the combination of laws, regulations, and contractual requirements, creating the specific duties organizations must fulfill to maintain legal conformity.
Cybercrime Prevention vs. Organizational Obligations
Cybersecurity laws serve dual purposes with distinct legal mechanisms:
- Criminal provisions punish malicious actors who conduct unauthorized access, deploy malware, engage in fraud, or perpetrate other cybercrimes. These provisions typically involve criminal penalties, including imprisonment and fines, enforced through prosecutorial action.
- Organizational obligations require entities to implement proactive security measures, conduct risk assessments, report incidents, and maintain resilience capabilities. These administrative requirements use civil penalties, regulatory sanctions, and compliance orders as enforcement mechanisms.
This regulatory tension highlights why organizations must clearly distinguish between compliance-driven security controls and individual data rights, a distinction explored in detail in our analysis of privacy vs security in 2025.
Major Cybersecurity Laws by Region and Country
The global cybersecurity legal landscape reflects diverse approaches influenced by regional priorities, governance models, and varying perceptions of threats. This section examines major jurisdictions and their regulatory frameworks.
United States: Federal and Sectoral Approach
The United States employs a sectoral regulatory model, where different laws apply to specific industries and government operations, resulting in a complex compliance landscape.
Computer Fraud and Abuse Act (CFAA)
The CFAA represents America’s primary federal statute addressing cybercrime, criminalizing unauthorized access to computer systems. According to NRI Secure’s compliance guide, the CFAA permits victims to sue entities responsible for unauthorized system access, with businesses facing potential lawsuits from customers or partners after breaches.
The CFAA prohibits:
- Accessing computers without authorization or exceeding authorized access
- Obtaining information from protected computers
- Transmitting programs, information, codes, or commands that cause damage
- Trafficking in computer passwords
- Threatening to damage protected computers for extortion purposes
Penalties range from civil damages to criminal prosecution with imprisonment up to 20 years for aggravated offenses.
Federal Information Security Modernization Act (FISMA)
FISMA 2014 updates the Federal Government’s cybersecurity practices by codifying the Department of Homeland Security’s (DHS) authority to administer the implementation of information security policies for non-national security federal Executive Branch systems, according to CISA’s official guidance.
FISMA requires federal agencies to:
- Develop, document, and implement agency-wide information security programs
- Provide security awareness training to personnel
- Conduct annual independent evaluations of security programs
- Report security incidents to CISA within one hour of discovery
- Implement NIST Risk Management Framework controls
The law establishes accountability through agency Inspector General audits and congressional reporting requirements.
Cybersecurity Information Sharing Act (CISA)
The Cybersecurity Information Sharing Act facilitates voluntary sharing of cyber threat indicators between private sector entities and government agencies. The law provides liability protection for entities sharing threat information in good faith, encouraging collaborative defense against emerging threats.
Sector-Specific Regulations
The HIPAA (Health Insurance Portability and Accountability Act) mandates comprehensive security controls for healthcare entities that handle protected health information. The Security Rule requires administrative, physical, and technical safeguards with penalties reaching $1.5 million annually per violation category.
The GLBA (Gramm-Leach-Bliley Act) requires financial institutions to implement information security programs that protect customer information. The Safeguards Rule mandates risk assessments, access controls, encryption, and incident response capabilities.
Critical Infrastructure Protection regulations from sector-specific agencies (like NERC CIP for power grids) impose stringent security requirements on critical infrastructure operators.
Emerging US Requirements
The Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) establishes mandatory reporting requirements for critical infrastructure entities that experience significant cyber incidents. Organizations must report covered incidents within 72 hours and ransomware payments within 24 hours of occurrence.
State-level regulations, such as the California Consumer Privacy Act (CCPA) and the New York SHIELD Act, create additional security and breach notification requirements at the state level.
European Union: Harmonized Comprehensive Framework
The European Union has developed the world’s most comprehensive and stringent cybersecurity regulatory framework, comprising multiple interconnected regulations that create a unified security regime.
NIS2 Directive: Enhanced Cybersecurity Across the EU
The NIS2 Directive, Cyber Resilience Act (CRA), and Digital Operational Resilience Act (DORA) collectively harmonize cybersecurity standards across critical sectors, including infrastructure, digital products, and financial services, according to Infosecurity Magazine’s 2025 analysis.
The NIS2 Directive (Directive (EU) 2022/2555) significantly expands the scope and requirements of the original NIS Directive:
Expanded Scope: NIS2 covers 18 sectors, including energy, transport, banking, financial market infrastructures, health, drinking water, wastewater, digital infrastructure, public administration, space, postal and courier services, waste management, manufacturing, food production, chemical production, and digital providers.
Entity Categories: The directive distinguishes between “essential entities” (larger organizations with stricter requirements) and “important entities” (medium-sized organizations with proportionate requirements).
Key Obligations:
- Implement comprehensive risk management measures
- Report significant incidents within 24 hours (early warning) and 72 hours (detailed notification)
- Address supply chain security risks
- Implement security measures, including incident handling, business continuity, supply chain security, network security, access control, and encryption.
- Conduct regular security audits and vulnerability assessments
Penalties: Member states must ensure penalties of at least €10 million or 2% of the entity’s annual worldwide turnover for essential entities, and €7 million or 1.4% of the entity’s turnover for crucial entities.
Implementation Status: As of June 30, 2025, only 14 EU Member States have fully transposed NIS2 into national law, while the European Commission continues to monitor implementation.
Digital Operational Resilience Act (DORA)
DORA (Regulation (EU) 2022/2554) establishes comprehensive digital operational resilience requirements for the financial sector. Unlike NIS2, DORA applies as a regulation directly binding across all EU member states without the need for national transposition.
Scope: DORA applies to approximately 22,000 financial entities, including credit institutions, payment institutions, investment firms, crypto-asset service providers, insurance companies, and critical third-party ICT service providers.
Five Pillars of Requirements:
- ICT Risk Management: Comprehensive governance frameworks, business continuity planning, and disaster recovery capabilities
- Incident Reporting: Mandatory reporting of significant ICT-related incidents to competent authorities
- Digital Operational Resilience Testing: Regular vulnerability assessments and penetration testing, with threat-led penetration testing (TLPT) for significant entities
- Third-Party ICT Risk Management: Stringent requirements for managing risks from ICT service providers, including contractual provisions and exit strategies
- Information Sharing: Frameworks for sharing cyber threat intelligence and vulnerabilities
Enforcement: Direct supervision of critical ICT service providers by EU authorities, with penalties up to €10 million or 5% of annual worldwide turnover.
Implementation Timeline: DORA became applicable on January 17, 2025, with phased implementation of technical standards.
Cyber Resilience Act (CRA)
The Cyber Resilience Act (Regulation (EU) 2024/2847) aims to ensure that digital products, including hardware and software, meet minimum cybersecurity requirements, focusing on product security rather than operational response, as per the analysis of the NIS2 Directive.
The CRA establishes cybersecurity requirements for products with digital elements placed on the EU market:
Product Categories:
- Default Cybersecurity Class: Standard digital products requiring basic security
- Class I (Important Products): Products with elevated cybersecurity risks
- Class II (Critical Products): Products with the highest cybersecurity risks requiring a stringent conformity assessment
Manufacturer Obligations:
- Secure by design and by default, product development
- Vulnerability handling and coordinated disclosure
- Security updates throughout the product lifecycle (minimum 5 years)
- Transparency regarding security properties
- CE marking indicating conformity
Supply Chain Requirements: Due diligence obligations for components and development processes, including software bill of materials (SBOM) requirements.
Penalties: Up to €15 million or 2.5% of annual worldwide turnover, demonstrating the EU’s commitment to product security.
Effective Date: The CRA will take effect from December 2027, with vulnerability handling requirements commencing in December 2026.
GDPR and Cybersecurity Overlaps
While primarily a privacy regulation, the General Data Protection Regulation (GDPR) creates significant cybersecurity obligations:
Article 32: Mandates appropriate technical and organizational security measures, including encryption, pseudonymization, regular testing, and resilience capabilities.
Article 33: Requires notification of personal data breaches to supervisory authorities within 72 hours of becoming aware of the breach.
Data Protection Impact Assessments: Required for high-risk processing activities, incorporating cybersecurity risk analysis.
The GDPR’s maximum penalties of €20 million or 4% of annual global turnover create a substantial incentive for robust security implementation.
Cyber Solidarity Act
The proposed Cyber Solidarity Act aims to establish EU-wide incident response and recovery mechanisms, creating a European Cybersecurity Alert System and Emergency Response Fund. While still under legislative process, it represents the EU’s commitment to collective cyber defense capabilities.

Source: Secforce- NIS2 vs DORA
United Kingdom: Post-Brexit Cybersecurity Framework
The United Kingdom maintains a sophisticated cybersecurity legal framework that parallels EU requirements while developing independent regulatory approaches:
Network and Information Systems Regulations: The UK’s NIS Regulations implement cybersecurity requirements for operators of essential services and relevant digital service providers. Following Brexit, the UK is developing its own Cyber Security and Resilience Bill to modernize and enhance these requirements.
Data Protection Act 2018: The Data Protection Act 2018 incorporates GDPR-equivalent requirements into UK law, maintaining stringent data security obligations with penalties up to £17.5 million or 4% of global annual turnover.
Computer Misuse Act 1990: The Computer Misuse Act criminalizes unauthorized access to computer systems, unauthorized acts with the intent to impair computer operation, and creating or supplying tools for committing computer misuse offenses.
Regulatory Bodies:
- Information Commissioner’s Office (ICO): Enforces data protection and privacy regulations.
- National Cyber Security Centre (NCSC): Provides technical guidance and incident response support.
- Ofcom: Regulates telecommunications security.
Emerging UK Framework: The proposed Cyber Security and Resilience Bill will introduce:
- Enhanced incident reporting requirements
- Expanded scope of regulated entities
- Supply chain security obligations
- Improved enforcement powers for regulators
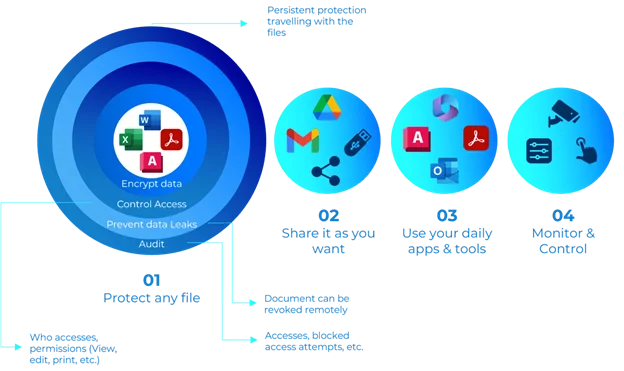
Source: Sealpath – NIS2 Directive Guide
Canada: Evolving Federal Framework
Canada employs a combination of federal and provincial laws addressing cybersecurity and privacy:
Personal Information Protection and Electronic Documents Act (PIPEDA): PIPEDA establishes privacy and security requirements for private sector organizations, mandating the implementation of reasonable security safeguards appropriate to the sensitivity of the information.
Security Breach Notification: Organizations must report breaches of security safeguards involving personal information that pose a real risk of significant harm.
Proposed Bill C-26: Bill C-26 represents Canada’s most significant cybersecurity legislation, expected to pass in 2025:
Critical Cyber Systems Protection Act: Establishes cybersecurity program requirements for critical infrastructure sectors, including telecommunications, energy, transportation, and finance.
Key Requirements:
- Implement comprehensive cybersecurity programs
- Conduct regular risk assessments and audits
- Report cybersecurity incidents to authorities
- Designate responsible persons for cybersecurity
- Comply with ministerial orders during cyber emergencies
Penalties: Administrative monetary penalties up to CAD $15 million and criminal penalties, including imprisonment.
Communications Security Establishment (CSE) Act: Authorizes CSE to provide cybersecurity and information assurance services to federal institutions and critical infrastructure operators.
Regulatory Authority: CSE provides technical guidance, threat intelligence, and incident response support to critical infrastructure sectors.

Source: Everbridge – EU Regulations Guide
India: Comprehensive Digital Governance
India has developed an extensive cybersecurity legal framework addressing both criminal conduct and organizational obligations:
Information Technology Act 2000 (IT Act)
The IT Act provides the foundational legal framework for cybersecurity in India:
- Section 43: Establishes civil liability for unauthorized access, data theft, virus introduction, and service disruption, with compensation up to INR 5 crores.
- Section 66: Criminalizes hacking with imprisonment up to 3 years and fines up to INR 5 lakhs.
- Section 70: Protects critical information infrastructure, with penalties including imprisonment up to 10 years.
- Section 72A: Criminalizes disclosure of personal information obtained during service provision, protecting data confidentiality.
CERT-In Cyber Security Directions 2022
The Indian Computer Emergency Response Team (CERT-In) issued comprehensive cybersecurity directions requiring:
Incident Reporting: Mandatory reporting of cybersecurity incidents within 6 hours to CERT-In, covering 20 categories of incidents including data breaches, ransomware, unauthorized access, and malware.
Logging Requirements: Organizations must maintain system logs for a period of 180 days and traffic logs for a rolling 180-day period.
Vulnerability Reporting: Mandatory disclosure of vulnerabilities to CERT-In before public disclosure or patching.
KYC Requirements: Service providers must maintain accurate customer information and verify the identity of users.
Penalties: Non-compliance can result in imprisonment up to one year and removal of certifications or licenses.
Digital Personal Data Protection Act 2023 (DPDP Act)
While primarily focused on privacy, the DPDP Act creates security obligations:
- Implement reasonable security safeguards to prevent data breaches
- Notify Data Protection Board and affected individuals of breaches
- Maintain data accuracy and limit retention
- Penalties up to INR 250 crores for violations
Sector-Specific Regulations
Reserve Bank of India (RBI): Mandates comprehensive cybersecurity frameworks for banks and financial institutions, including penetration testing, vulnerability assessments, and incident response capabilities.
Securities and Exchange Board of India (SEBI): Requires stock exchanges, brokers, and market intermediaries to implement robust cybersecurity controls.
Telecom Regulatory Authority of India (TRAI): Establishes security requirements for telecommunications service providers.
Regulatory Authority: CERT-In serves as the national nodal agency for cybersecurity incident response, with the Ministry of Electronics and Information Technology (MeitY) providing policy direction.

Source: industrialcyber – Federal Security Requirements
China: State-Centric Cybersecurity Regime
China has constructed one of the world’s most comprehensive and restrictive cybersecurity legal frameworks, emphasizing state security and data sovereignty:
Cybersecurity Law (2017)
The foundational Cybersecurity Law establishes broad security obligations:
Network Operator Obligations:
- Implement graded cybersecurity protection systems
- Conduct security assessments and testing
- Monitor and record network operations
- Respond to security incidents promptly
- Cooperate with government supervision
Critical Information Infrastructure (CII): Enhanced requirements for sectors including public communications, information services, energy, transportation, finance, public services, and e-government.
Data Localization: CII operators must store personal information and important data collected in China within China’s borders.
Security Review: Network products and services used by CII operators must undergo a security review before procurement.
Penalties: Include Warnings, fines of up to RMB 1 million, business suspension, and revocation of licenses.
Data Security Law (2021)
The Data Security Law complements the Cybersecurity Law by establishing data classification and protection requirements:
Data Classification: Three-tier system of general, critical, and core data with corresponding protection measures.
Data Security Review: Cross-border data transfers and data processing activities affecting national security require government review.
Data Trading Regulations: Rules governing legitimate data collection, use, processing, and trading.
Penalties: Fines ranging from RMB 500,000 to RMB 10 million, with severe cases resulting in business suspension.
Personal Information Protection Law (PIPL, 2021)
China’s comprehensive privacy law creates significant security obligations:
Security Requirements: Technical and organizational measures commensurate with the sensitivity of the information and the volume of processing.
Breach Notification: Mandatory notification to authorities and affected individuals without undue delay.
Cross-Border Transfers: Restrictions on personal information transfers outside China, requiring security assessments or certification.
Penalties: Fines up to RMB 50 million or 5% of annual revenue.
- Cyberspace Administration of China (CAC): Primary regulator with authority over internet content, data security, and cross-border data flows.
- Ministry of Industry and Information Technology (MIIT): Regulates telecommunications and internet infrastructure security.
- Ministry of Public Security (MPS): Enforces cybercrime laws and conducts security inspections.
Enforcement Approach: China employs an aggressive enforcement approach, including mandatory security reviews, on-site inspections, and swift penalties for non-compliance.
Asia-Pacific and Global Regions
- Singapore: Risk-based Cybersecurity Act 2018, focusing on critical infrastructure, with penalties up to SGD 1 million.
- Japan: Collaborative framework through the Cybersecurity Basic Act with 14 critical sectors and emphasis on public-private partnerships.
- Australia: Security of Critical Infrastructure Act with enhanced obligations across 11 sectors and penalties up to AUD 15.6 million.
- Middle East: UAE, Saudi Arabia, and Qatar are developing comprehensive frameworks with severe penalties for cybercrimes.
- Africa: South Africa’s POPIA and Cybercrimes Act; Nigeria’s NDPR and Cybercrimes Act establishing regional leadership.
- Latin America: Brazil’s LGPD and Mexico’s data protection laws are creating privacy-driven security requirements.
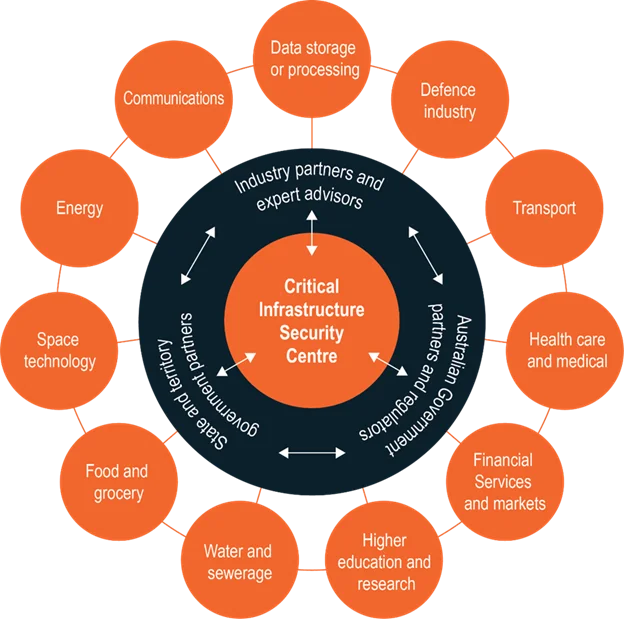
Source: Cisc.gov.au – Critical Infrastructure
Beyond cybersecurity, organizations operating digital platforms must also navigate overlapping legal risks, including intellectual property enforcement and liability exposure, as outlined in our copyright infringement challenges guide for 2025.
Conclusion
The first part of this guide establishes a foundational understanding of global cybersecurity laws in 2025, examining the core principles that underpin these regulations and the major frameworks across key jurisdictions. From the United States’ sectoral approach to the European Union’s comprehensive harmonized model, and from China’s state-centric regime to emerging frameworks in Asia-Pacific, the Middle East, Africa, and Latin America, the diversity of approaches reflects different governance philosophies and threat priorities.
Understanding these foundational elements, such as the CIA triad, the distinction between laws and regulations, and the dual purpose of criminal provisions versus organizational obligations, provides the essential context for navigating the complex compliance landscape. As we have seen, major jurisdictions have implemented increasingly stringent requirements, with the EU leading the way through NIS2, DORA, and the upcoming Cyber Resilience Act. At the same time, other regions develop parallel frameworks tailored to their unique contexts.
The second part of this guide will examine the practical aspects of compliance, including core obligations that organizations must fulfill, the enforcement mechanisms that regulators employ, emerging trends shaping 2025, and actionable guidance for beginners starting their compliance journey. Together, these two articles provide the comprehensive understanding necessary for organizations to navigate the evolving cybersecurity legal landscape effectively.
Glossary
Understanding cybersecurity law terminology facilitates comprehension and compliance:
Advanced Persistent Threat (APT): A Prolonged, targeted cyber attack where intruders establish an ongoing presence in networks to steal sensitive data.
Breach: Unauthorized access, acquisition, disclosure, or loss of personal information or sensitive data compromising security or confidentiality.
CIA Triad: Core cybersecurity principles of Confidentiality, Integrity, and Availability that laws seek to protect.
Compliance: Meeting legal, regulatory, and contractual security requirements through implementation of required controls and processes.
Critical Infrastructure: Systems and assets essential to national security, economic security, public health, or safety whose incapacity would have debilitating impacts.
Encryption: The Process of converting information into a coded format readable only with a decryption key, protecting data confidentiality.
Incident: Security event compromising confidentiality, integrity, or availability of information systems or data.
Penetration Testing: Authorized simulated cyber attack evaluating system security by attempting exploitation of vulnerabilities.
Personal Data/Information: Information relating to identified or identifiable individuals, subject to privacy law protections.
Risk Assessment: A Systematic process identifying, analyzing, and evaluating cybersecurity threats, vulnerabilities, impacts, and likelihood.
Security Controls: Technical, administrative, and physical safeguards protecting information systems from threats and ensuring compliance.
Supply Chain: A Network of entities involved in creating and delivering products or services, creating potential security dependencies and risks.
Threat Intelligence: Evidence-based knowledge about existing or emerging threats used to inform security decisions and response.
Vulnerability: Weakness in a system, application, or process that could be exploited to compromise security.Zero-Day: Previously unknown software vulnerability for which no patch exists, making it particularly dangerous until discovered and remediated.
Frequently Asked Questions
What are the main global trends in cybersecurity laws in 2025?
Governments are moving toward stricter, risk‑based cybersecurity regimes with mandatory incident reporting, stronger governance, and higher penalties for non‑compliance. International guidance such as the Cyber Law Toolkit 2025 update also reinforces due diligence, responsibility, and cross‑border cooperation in cyber incidents.
Which key international and regional frameworks shape cybersecurity obligations?
Core influences include EU instruments like NIS2, DORA, and the Cyber Resilience Act, as well as global guidance on international cyber law from NATO‑linked initiatives and sectoral standards. These frameworks set expectations for risk management, resilience testing, supply‑chain security, and coordinated response across borders.
How do cybersecurity requirements differ by region (EU, US, Asia‑Pacific, etc.)?
The EU applies a harmonized model with horizontal obligations on critical sectors and digital services, backed by substantial turnover‑based fines. The US and many Asia‑Pacific states rely more on a mix of sector‑specific rules and state or national legislation, with growing emphasis on critical infrastructure obligations and incident reporting
What types of controls do these laws typically require from organizations?
Common requirements include governance structures, ICT risk management, business continuity and disaster recovery, regular vulnerability and penetration testing, and third‑party risk management. Many laws also expect logging, access control, MFA, encryption, and formal incident response plans as baseline controls.
How can organizations operating in multiple countries stay compliant across different regimes?
Organizations usually adopt a unified internal framework aligned with leading standards, then map local legal requirements (EU, US, APAC, Middle East, etc.) onto that baseline. Maintaining a cross‑jurisdictional register of obligations, supported by centralized policies and region‑specific procedures, helps manage overlapping and sometimes conflicting rules.
