Ransomware attacks have become the most destructive cyber threat, posing serious risks to businesses, government networks, and individual users worldwide.

Ransomware remains one of the most dangerous cybercrime threats in 2025, targeting individuals, corporations, and even critical infrastructure. These malicious programs encrypt files and demand payment for their release, often causing severe data loss and financial damage.
According to Fortinet’s 2025 statistics:
“The Qilin ransomware group alone carried out 81 attacks in June 2025, marking a 47.3% increase.”
TechTarget reports that:
“U.S. ransomware attacks increased by 149% year over year in the first five weeks of 2025, understanding ransomware is critical for everyone.”
This guide explains what ransomware is, how it works, notable attack examples, and most importantly, how you can protect yourself and recover if you become a victim.

Source: Fortinet-Ransomware Statistics 2025
What Is Ransomware and How Does It Work?
Ransomware is malicious software that encrypts your files, making them completely inaccessible, and demands payment (ransom) to decrypt them. Think of it like digital kidnapping, where criminals hold your data hostage until you pay. However, unlike physical kidnapping, paying the ransom does not guarantee you will get your files back.
The Ransomware Attack Process
Understanding how ransomware attacks unfold helps you recognize and prevent them:
Step 1: Initial Access Criminals gain entry to your system through phishing emails, malicious downloads, compromised websites, or exploiting software vulnerabilities.
According to CISA’s ransomware guide:
“Phishing remains the most common entry point for ransomware attacks.”
Step 2: Execution and Encryption Once inside, the ransomware executes and begins encrypting files. Modern ransomware uses strong encryption algorithms that are virtually impossible to break without the decryption key. The malware often targets document files, databases, images, and backups first.
Step 3: Ransom Demand After encryption completes, a ransom note appears on your screen. This note explains what happened, demands payment (usually in cryptocurrency like Bitcoin), and provides instructions for payment. The note often includes threats to delete files permanently or publish sensitive data if you do not pay within a deadline.
Step 4: Double Extortion Many modern ransomware groups use “double extortion” tactics. They not only encrypt your files but also steal copies of your data before encryption. They threaten to publish this stolen data publicly if you don’t pay, even if you have backups and can restore your files.
Types of Ransomware
Different ransomware variants use different tactics:
Crypto Ransomware encrypts files but leaves the system functional so you can see the ransom demand and make payment.
Locker Ransomware locks you out of your entire system, preventing access to everything.
Scareware displays fake warnings claiming your system is infected and demands payment to fix it. While less dangerous, it still tricks people into paying.
Doxware threatens to publish stolen personal or sensitive data unless you pay.
Ransomware-as-a-Service (RaaS) is a business model where ransomware developers sell or rent their malware to other criminals, making ransomware attacks more accessible to less technical criminals.
Source: CISA-Stop Ransomware Guide
Ransomware Statistics: The Growing Threat in 2025
The ransomware threat has escalated dramatically in 2025:
Attack Volume and Growth
G2’s comprehensive analysis reveals:
“Over 5,263 attacks were recorded in 2024, the highest ever since tracking began in 2021.”
The trend has continued into 2025 with even more attacks.
Astra Security reports:
“Some of the most reported strains of ransomware are Ryuk with 180.4 million targets, SamSam with 103.9 million targets, and Cerber with 28.2 million targets.”
These numbers show the massive scale of ransomware operations.
Financial Impact
The average ransom payment has increased significantly.
G2 suggests:
“LockBit accounted for $91 million worth of ransomware payments in 2025, making it the most prolific group that year.”
However, the total cost of attacks far exceeds ransom payments when you include downtime, recovery expenses, and lost business.
Organizations face devastating financial consequences:
- Average ransom demands range from $50,000 to several million dollars
- Recovery costs average 10 times the ransom amount
- Business interruption costs can exceed millions per day
- Reputation damage leads to customer loss
- Regulatory fines for data breaches
Most Active Ransomware Groups
According to Fortinet, Qilin became the most active ransomware group by June 2025. Other notable groups include:
- RansomHub was the most consistently active operator throughout 2024 and early 2025.
- LockBit, despite law enforcement disruptions, remains a significant threat with millions in ransom payments.
- Akira has shown steady growth in attack volume.
Rapid7’s Q2 2025 analysis identified 11 net new ransomware groups in Q2 2025 alone, including KaWa4096, Warlock, Devman, Nova, and Dire Wolf. This proliferation shows that taking down one group doesn’t stop the overall threat.
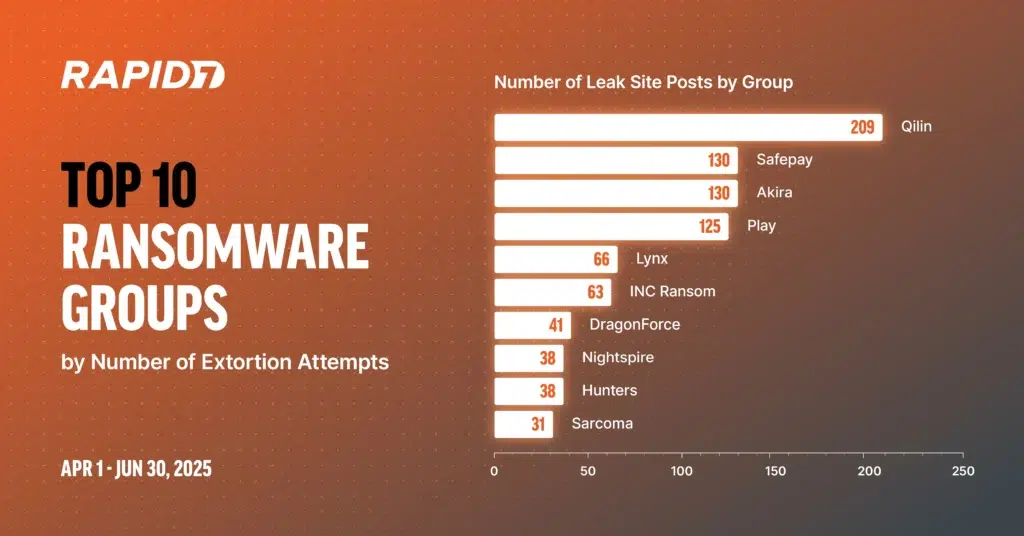
Source: Q2 2025 Ransomware Trends Analysis
Industry Targets
According to Spacelift’s statistics, Ransomware attacks target all sectors, but some industries are hit harder:
- Healthcare organizations (hospitals can’t afford downtime that endangers lives)
- Financial services (hold valuable data and can pay large ransoms)
- Government agencies (critical services and political pressure to restore quickly)
- Manufacturing (production downtime is extremely costly)
- Education institutions (limited security budgets but valuable student data)
Notable Ransomware Attack Examples
Real-world examples show the devastating impact of ransomware:
Healthcare Sector Attacks
Hospitals have been hit particularly hard because they must restore operations quickly to provide patient care. Ransomware attacks have forced hospitals to divert ambulances, cancel surgeries, and revert to paper records. In some cases, delayed treatment due to ransomware attacks has contributed to patient deaths.
One major healthcare system paid a multimillion-dollar ransom after attackers encrypted patient records and operational systems. Even after payment, full recovery took weeks and cost far more than the ransom itself.
Colonial Pipeline Attack (Historical Reference)
The 2021 Colonial Pipeline attack remains a cautionary tale. Ransomware shut down the largest fuel pipeline in the U.S., causing widespread gas shortages and panic buying. The company paid $4.4 million in ransom, though law enforcement later recovered most of it. This attack demonstrated how ransomware can disrupt critical infrastructure and affect millions of people.
Educational Institution Compromises
Universities and school districts have become frequent targets because they have limited security budgets but store valuable personal information about students and staff. CM Alliance documented major organizations hit by ransomware in June 2025, highlighting the ongoing threat to educational institutions.
Corporate Data Breaches
Major corporations have paid millions in ransom after attackers encrypted operational systems and stole sensitive business data. The double extortion tactic—threatening to publish stolen data has proven particularly effective against businesses with confidential information, trade secrets, or customer data they must protect.
Fake Ransom Campaigns
Palo Alto Networks’ Unit 42 documented a March 2025 campaign where scammers physically mailed threatening letters to executives claiming to be a known ransomware group. While no actual ransomware was deployed, these extortion attempts show the evolving tactics criminals use.
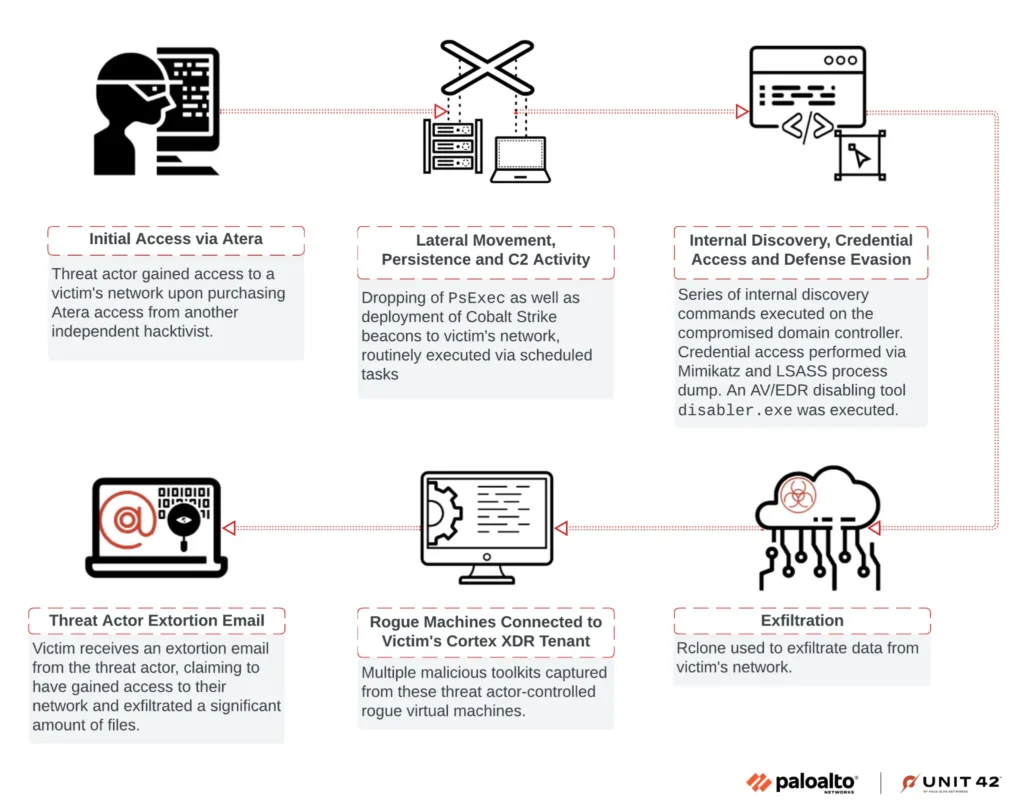
Source: Extortion and Ransomware Trends
Should You Pay the Ransom? Understanding Negotiation
This is one of the most difficult decisions organizations face during a ransomware attack:
Arguments Against Paying
Law enforcement agencies, including the FBI, strongly discourage paying ransoms:
No guarantee of recovery: Paying doesn’t ensure you’ll receive a working decryption key. Some victims pay and still lose their data.
Funds criminal operations: Your payment funds additional attacks against others. Ransomware remains profitable because victims pay.
You become a target: Organizations that pay are often targeted again because criminals know they’ll pay.
Legal implications: In some jurisdictions, paying ransoms to certain groups may violate sanctions or anti-terrorism laws.
When Organizations Consider Paying
Despite recommendations against paying, some organizations feel they have no choice:
- Critical data with no usable backups
- Life-threatening situations (hospitals needing patient records)
- Bankruptcy risk from extended downtime
- Regulatory or contractual obligations to restore customer data
- Less expensive than recovery costs in some cases
The Negotiation Process
Organizations that decide to negotiate typically hire specialized firms that:
- Verify attackers actually have decryption capabilities
- Negotiate lower ransom amounts (often achieving 50-70% reductions)
- Handle cryptocurrency transactions
- Test decryption keys before full payment
- Provide guidance on communication with attackers
However, negotiation doesn’t change the fundamental problem: you’re dealing with criminals who have no obligation to honor agreements.
Ransomware Prevention: Building Strong Defenses
Prevention is far better than dealing with an attack. Here are proven strategies:
Implement Robust Backup Systems
Backups are your most important defense against ransomware. SentinelOne emphasizes:
“Backup frequency depends on data sensitivity and business needs. Critical data must be backed up daily, even hourly.”
Follow the 3-2-1-1 Rule: According to Cypfer’s best practices:
“Follow the 3-2-1 rule (3 copies, 2 different storage types, 1 offsite).”
Modern recommendations add a fourth element: one immutable or air-gapped copy.
3 copies of your data (original plus two backups) 2 different media types (like hard drives and cloud storage) 1 offsite backup (protects against physical disasters) 1 immutable backup (cannot be encrypted or deleted by ransomware)
Use Immutable Backups: Veeam’s ransomware prevention guide stresses:
“Immutable and encrypted backups” serve as “the last line of defense against encryption or deletion by attackers.”
Immutable storage prevents anyone, including ransomware, from modifying or deleting backups for a specified retention period.
Store Backups Offline: CISA recommends backing up:
“Data often; offline or leverage cloud-to-cloud backups.”
Air-gapped backups physically disconnected from networks cannot be reached by ransomware.
Test Backup Restoration: Backups are worthless if you can’t restore from them. Regularly test your backup restoration process to ensure:
- Backups complete successfully
- Files are not corrupted
- Restoration procedures work
- Recovery time meets your needs
Security Awareness Training
Employees are often the first line of defense. Train staff to:
- Recognize phishing emails
- Avoid clicking suspicious links
- Never download attachments from unknown senders
- Report suspicious activity immediately
- Follow security policies consistently
Keep Systems Updated
According to The Hacker News, ransomware often exploits known vulnerabilities that have patches available. Implement:
- Automatic updates for operating systems
- Patch management for all software
- Vulnerability scanning to identify weaknesses
- Prioritized patching for critical vulnerabilities
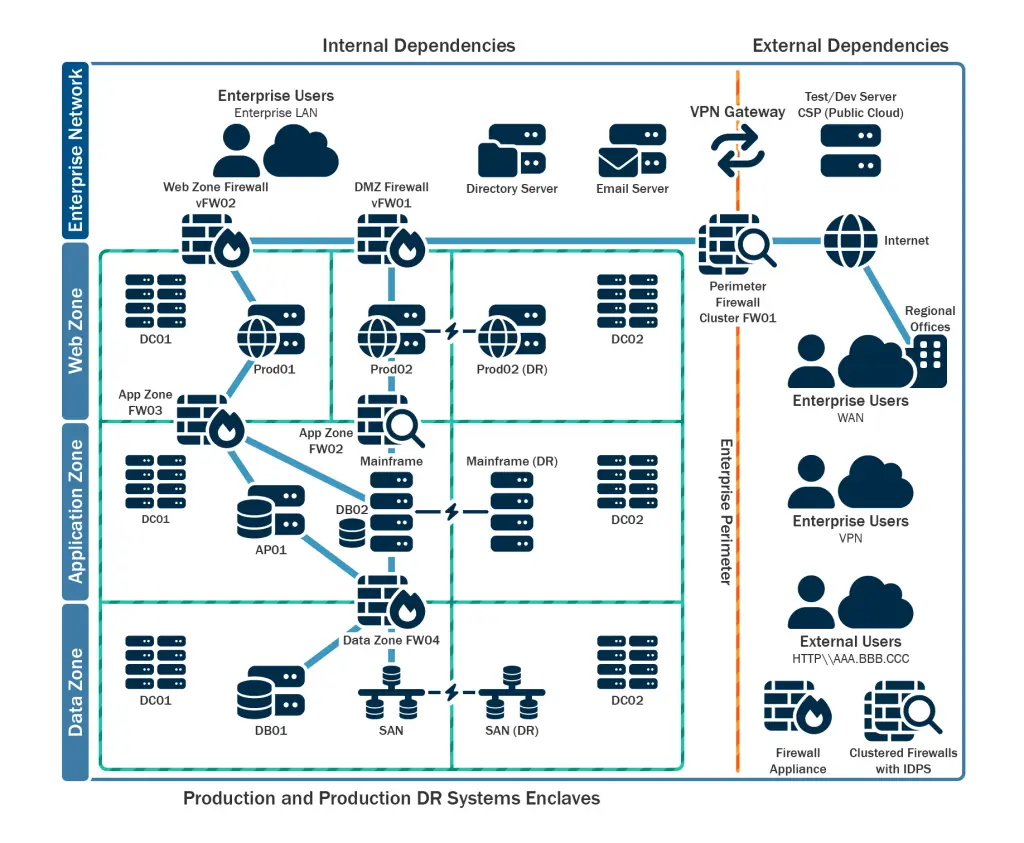
Implement Network Segmentation
Segment your network to limit ransomware spread. If one system gets infected, segmentation prevents lateral movement to other systems. Critical systems and backups should be on separate network segments with restricted access.
Deploy Endpoint Protection
Use advanced endpoint detection and response (EDR) solutions that:
- Monitor for ransomware behaviors
- Block suspicious processes
- Isolate infected systems automatically
- Provide forensic data for investigation
Enable Multi-Factor Authentication
CISA recommends MFA on all accounts, especially for:
- Remote access (VPN, RDP)
- Email accounts
- Administrative accounts
- Cloud services
- Backup systems
Restrict User Privileges
Follow the principle of least privilege—give users only the access they need to do their jobs. This limits ransomware’s ability to spread and encrypt files across your network.
Disable Unnecessary Services
Ransomware often spreads through Remote Desktop Protocol (RDP) and other remote access services. Disable services you don’t need, and secure those you must use with strong authentication and network restrictions.
Ransomware Recovery: What to Do If You’re Hit
If ransomware strikes despite your defenses, act quickly:
Immediate Response Steps
Isolate infected systems: Disconnect affected devices from the network immediately to prevent ransomware spread. According to Canadian Centre for Cyber Security, quick isolation is critical.
Don’t power off systems: Keep infected systems running so forensic investigators can analyze what happened and potentially find the ransomware variant.
Document everything: Take photos of ransom notes, record what happened and when, and preserve evidence for law enforcement and insurance claims.
Report to authorities: Contact the FBI’s Internet Crime Complaint Center (IC3), local law enforcement, and relevant regulatory agencies.
Notify stakeholders: Inform leadership, IT security team, legal counsel, insurance provider, and potentially customers depending on the breach.
Assessment and Analysis
Identify the ransomware variant: Knowing which ransomware infected you helps determine if free decryption tools exist. Websites like NoMoreRansom.org maintain databases of decryption tools.
Assess the damage: Determine which systems and data are affected, what backups are available, and how long recovery will take.
Check backups: Verify your backups are clean and functional. Canadian Centre for Cyber Security advises:
“Analyze your backup files and ensure they are free of ransomware or any other malware before restoration.”
Recovery Process
Clean infected systems: Wipe and rebuild infected systems from scratch. Don’t trust that removing ransomware is sufficient, attackers often leave backdoors.
Restore from backups: According to NIST guidelines:
“Preparing an organization to create and restore backup files can help mitigate the damage.”
Restore data from your clean, verified backups.
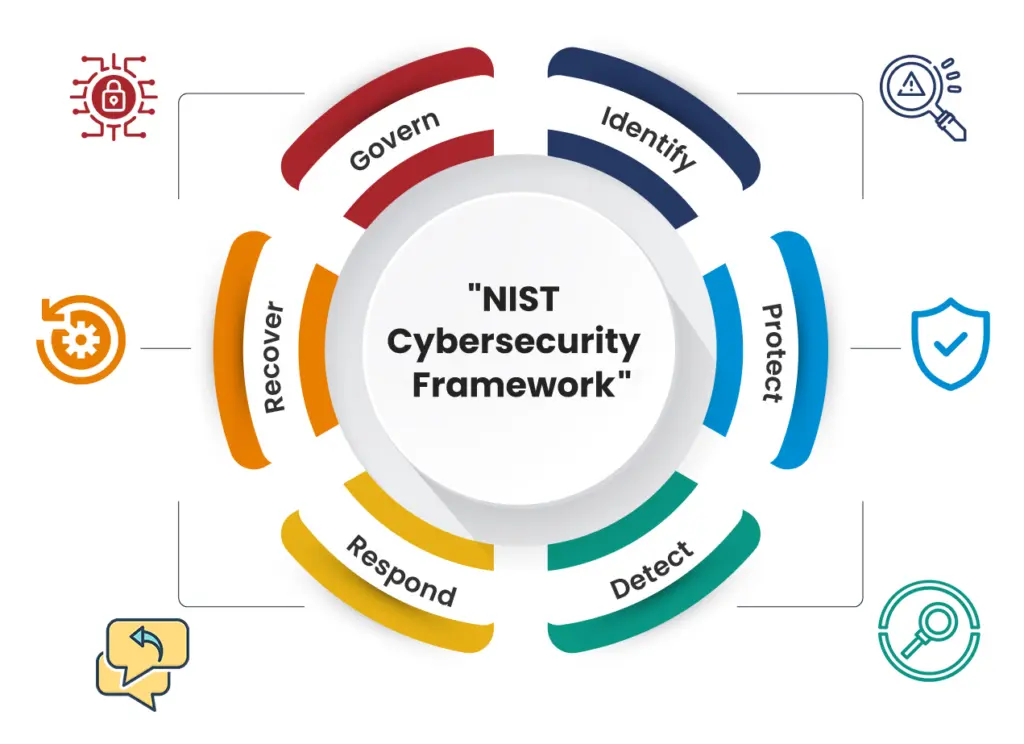
Source: NIST Cybersecurity Framework
Reset credentials: Change all passwords and security credentials. Assume attackers may have captured authentication information.
Strengthen security: Identify how ransomware entered and fix those vulnerabilities. Implement additional security controls to prevent reinfection.
Monitor closely: Watch for signs of remaining infection or reattack attempts. Ransomware groups sometimes target victims multiple times.
Long-Term Improvements
After recovery, implement lessons learned:
- Conduct post-incident review
- Update incident response plans
- Improve backup procedures
- Enhance security training
- Consider cyber insurance
- Develop business continuity plans
Conclusion
Ransomware represents one of the most serious cybersecurity threats in 2025, with attack volumes increasing 149% year over year and new groups emerging constantly. The statistics are alarming—over 5,000 attacks in 2024 alone, with the trend accelerating in 2025. Organizations across all sectors face this threat daily.
However, you’re not defenseless. Strong backup practices following the 3-2-1-1 rule provide insurance against data loss. Immutable, offline backups ensure you can recover without paying ransoms. Regular security training helps employees recognize and avoid phishing attacks that introduce ransomware. Keeping systems updated closes vulnerabilities attackers exploit.
If you do get hit, remember that law enforcement agencies discourage paying ransoms. Focus instead on isolation, recovery from backups, and strengthening defenses against future attacks. Document everything, report to authorities, and learn from the experience.
The ransomware threat will continue evolving as criminals develop new tactics and groups proliferate. Your best defense combines proactive prevention, robust backup systems, employee awareness, and a tested incident response plan. Start implementing these protections today—before you need them.
Glossary of Ransomware Terms
Air-Gapped Backup: Backup storage physically disconnected from networks, making it unreachable by ransomware
Cryptocurrency: Digital currency like Bitcoin used for ransom payments because it’s difficult to trace
Decryption Key: Digital key needed to unlock encrypted files; held by ransomware operators
Double Extortion: Tactic where attackers both encrypt files and threaten to publish stolen data
Encryption: Process of scrambling data so it’s unreadable without the decryption key
Immutable Storage: Storage that cannot be modified or deleted for a specified time period
Lateral Movement: Ransomware spreading from one system to others across a network
Payload: The malicious code that performs encryption
Ransom Note: Message from attackers explaining the attack and demanding payment
Ransomware-as-a-Service (RaaS): Business model where ransomware developers rent their malware to other criminals
Recovery Point Objective (RPO): Maximum acceptable amount of data loss measured in time
Recovery Time Objective (RTO): Maximum acceptable downtime for business operations
Zero Trust: Security model that requires verification for every access request
Frequently Asked Questions
What is ransomware and how does it work?
Ransomware is a cyberattack tool that locks or encrypts your data until a ransom is paid. It often spreads through phishing emails, infected downloads, or malicious links. Once it infects your device, ransomware blocks access to your system or files, demanding cryptocurrency payments for decryption. Understanding how ransomware works is the first step in effective ransomware protection in 2025.
How can I protect my system from ransomware in 2025?
To stay secure in 2025, use AI-powered antivirus tools, apply regular software updates, and maintain offline backups of your important data. Implement multi-factor authentication and a zero-trust security policy to limit unauthorized access. Educate employees and users about phishing awareness to strengthen your overall cybersecurity posture.
What should I do if my device is infected with ransomware?
If you face a ransomware attack, immediately disconnect your device from all networks to prevent it from spreading. Avoid paying the ransom, as it rarely guarantees recovery. Instead, contact cybersecurity professionals, report the incident to local authorities, and restore your data from a clean backup system. Quick isolation and expert guidance are key to ransomware recovery in 2025.
Can paying the ransom guarantee data recovery?
No — paying the ransom does not guarantee data restoration. Many victims never receive working decryption keys after payment. Moreover, sending money funds further cybercrime. The best solution is proactive ransomware defense: keep backups, use strong encryption, and rely on trusted recovery tools instead of giving in to demands.
What are the latest ransomware trends in 2025?
In 2025, ransomware will become more AI-driven and targeted. Hackers now use double extortion, encrypting files while threatening to leak sensitive data. Attacks are also shifting toward cloud platforms, IoT networks, and remote work environments. Companies are adopting automated response systems and real-time encryption monitoring to enhance ransomware prevention and recovery.
