This comprehensive guide breaks down the key differences between privacy and security, explores their connection through the CIA Triad, and reveals why both are critical for strong digital protection.
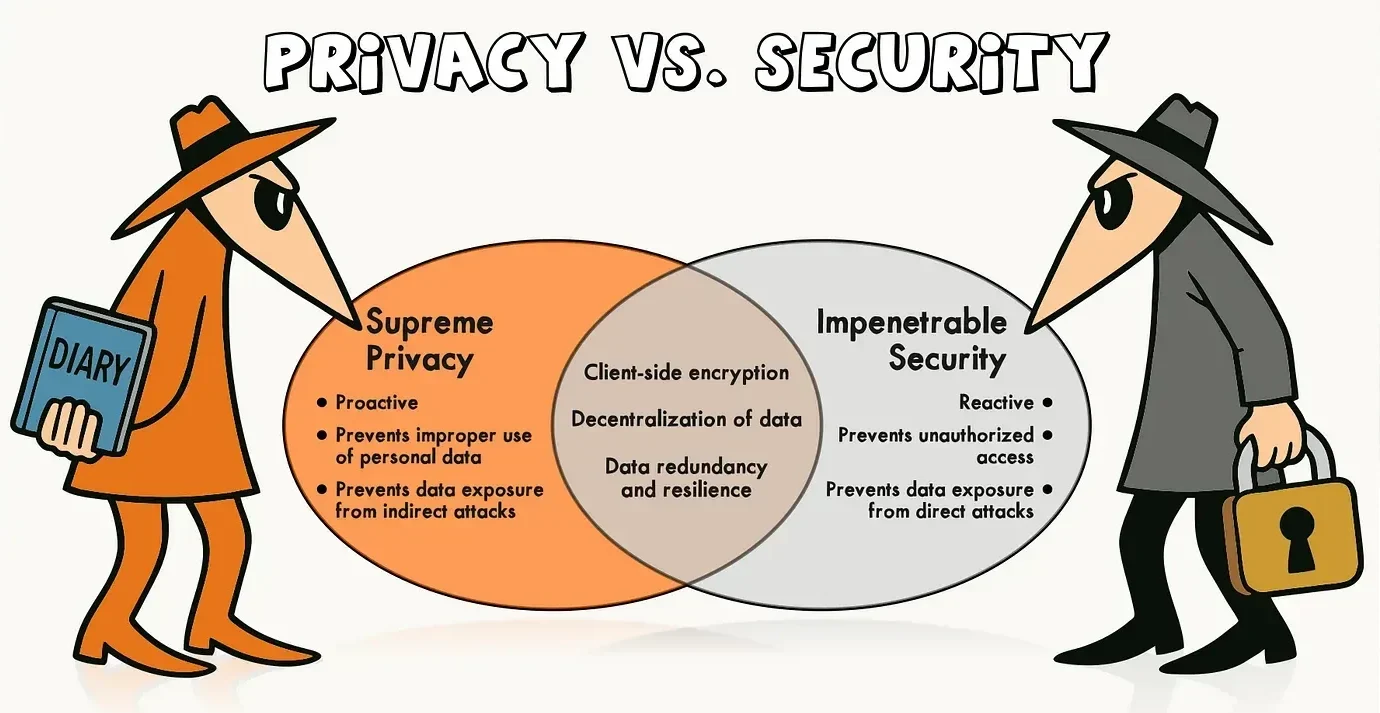
In today’s digital age, the debate of privacy vs. security has become more important than ever. While privacy focuses on protecting personal data and controlling who has access to it, security involves the tools and strategies used to defend that data from cyber threats. Understanding the key differences between privacy and security helps individuals and businesses make informed decisions about data protection, online safety, and compliance. Privacy and security are terms people often use interchangeably, but they represent distinct concepts that work together to protect your digital life.
According to Web Asha Technologies:
“Security focuses on protecting systems and data from threats, while privacy is about controlling how personal data is collected and used.”
Understanding these differences is critical, according to Okta:
“The main difference between data privacy and security is that Data Privacy involves how your data is used and controlled, while security protects this data.”
Privacy and Security Overview: Defining the Concepts
Before exploring differences, it is important to have a clear understanding of what privacy and security actually mean in the digital context.
What Is Security?
AuditBoard defines security as:
“Focusing on the protection of systems, assets, information, facilities, and data that an organization decides to safeguard, as well as the methods it employs to do so.”
Security is about protection against threats, unauthorized access, attacks, damage, or theft.
Security concerns the following queries:
- How do we protect data from unauthorized access?
- What measures prevent breaches?
- How do we detect and respond to attacks?
- Can we maintain system availability during incidents?
Security implements technical controls like firewalls, encryption, access controls, antivirus software, intrusion detection systems, and multi-factor authentication. These measures protect against external threats (hackers, malware) and internal risks (employee errors, insider threats).
What Is Privacy?
Privacy concerns about who has access to your information and how they use it.
Norton explains:
“Privacy relates to any rights you have to control your personal information.”
Privacy concerns the following:
- Who can access my data?
- How is my information being used?
- Can I control what’s shared?
- Do I have rights to delete my data?
- Am I informed about data collection?
Privacy involves legal rights, consent mechanisms, data usage policies, and individual control over personal information. While security protects data from unauthorized access, privacy governs what authorized parties can do with your information once they access it.
The Fundamental Difference
BlackFog clarifies the core distinction:
“Security is all about protecting access to your data, whereas privacy is about controlling what people are allowed to do with the information once it is accessed.”
Think of it this way: Security is the lock on your door, preventing burglars from entering your house. Privacy is the rules about what guests who are allowed inside can do, which rooms they can enter, what they can touch, and what they can tell others about what they saw.
Many of these security obligations are shaped by evolving regulatory frameworks, which are examined in detail in our Global Cybersecurity Laws: 2025 framework and regional requirements.
Understanding the CIA Triad: The Security Foundation
The CIA Triad provides a framework for understanding security principles and how they relate to privacy:

Confidentiality: Keeping Information Private
Confidentiality ensures that information is accessible only to authorized individuals. This is where security and privacy most directly overlap.
US Cybersecurity Magazine notes that:
“Security implements protection of sensitive data against unauthorized access.”
Security’s Role in Confidentiality: Encryption protects data from unauthorized viewing, access controls limit who can view information, authentication verifies user identities, and authorization determines what users can access.
Privacy’s Role in Confidentiality: Privacy defines who should be authorized, establishes consent requirements for data access, specifies legitimate purposes for accessing information, and grants individuals rights to control their data.
Example: A hospital’s security systems ensure only authorized staff can access medical records (confidentiality through security). Privacy rules determine which staff members should have authorization and what they can do with accessed information (confidentiality through privacy).
Integrity: Maintaining Data Accuracy
Integrity ensures that information remains accurate, complete, and unaltered except through authorized processes. This protects against unauthorized modification, corruption, or deletion of data.
Security’s Role in Integrity: Digital signatures verify data hasn’t been tampered with, checksums detect unauthorized modifications, version control tracks changes, and backup systems enable recovery from data corruption.
Privacy’s Role in Integrity: Privacy laws often include data accuracy requirements, individuals have rights to correct inaccurate information, organizations must maintain current and accurate records, and data minimization reduces integrity risks.
Example: Security systems prevent hackers from modifying your bank balance (integrity through security). Privacy rights let you correct errors in your credit report (integrity through privacy).
Availability: Ensuring Access When Needed
Availability ensures that information and systems remain accessible to authorized users when needed. This involves maintaining uptime, redundancy, and recovery capabilities.
Security’s Role in Availability: DDoS protection prevents attacks that shut down systems, redundant systems maintain operations during failures, disaster recovery restores operations after incidents, and backup systems provide alternative access.
Privacy’s Role in Availability: Privacy regulations require organizations to provide data access to individuals, timely responses to data requests, and continued service availability while respecting privacy rights.
Example: Security teams prevent ransomware from locking your files (availability through security). Privacy laws require companies to provide your data when you request it (availability through privacy).
Key Differences Between Privacy and Security
Understanding specific differences helps organizations and individuals implement both effectively:
Focus and Scope
Security Focus: Protecting against threats, preventing unauthorized access, detecting attacks, and responding to incidents. Security is threat-centric, focusing on what could go wrong and how to prevent it.
Privacy Focus: Controlling appropriate use of data, respecting individual rights, ensuring consent and transparency, and managing data throughout its lifecycle. Privacy is rights-centric, focusing on proper data handling even by authorized parties.
Secureworks explains that:
“Security controls are put in place to control who can access the information, while privacy is more granular, controlling what and when they can access specific data.”
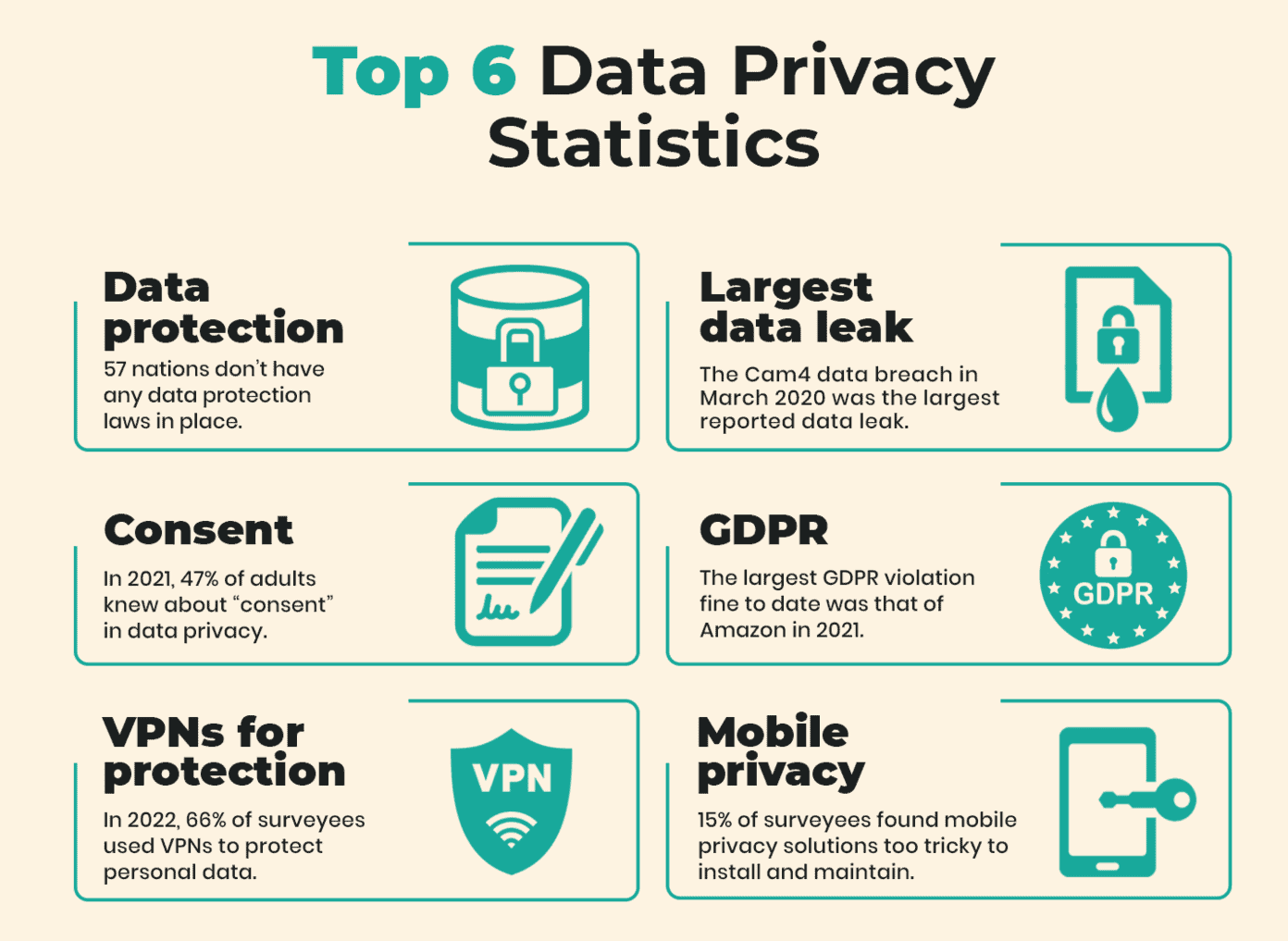
Source: Data Privacy Statistics
Questions Each Addresses
Security Asks:
- Can unauthorized people access our systems?
- Are we protected from malware and attacks?
- Can we detect and respond to breaches?
- Do we have backups if systems fail?
- Are our communications encrypted?
Privacy Asks:
- Do we have consent to collect this data?
- Are we using data only for stated purposes?
- Can individuals control their information?
- Are we transparent about data practices?
- Do we delete data when no longer needed?
Implementation Methods
Security Implementation:
- Technical controls (firewalls, encryption, authentication)
- Monitoring and detection systems
- Incident response procedures
- Vulnerability management
- Security testing and audits
Privacy Implementation:
- Privacy policies and notices
- Consent management systems
- Data mapping and inventories
- Individual rights request processes
- Data retention and deletion schedules
- Privacy impact assessments
Regulatory Frameworks
Security Regulations: Following are some known security regulations:
- FISMA (Federal Information Security Management Act)
- PCI DSS (Payment Card Industry Data Security Standard)
- NIST Cybersecurity Framework
- Industry-specific security standards
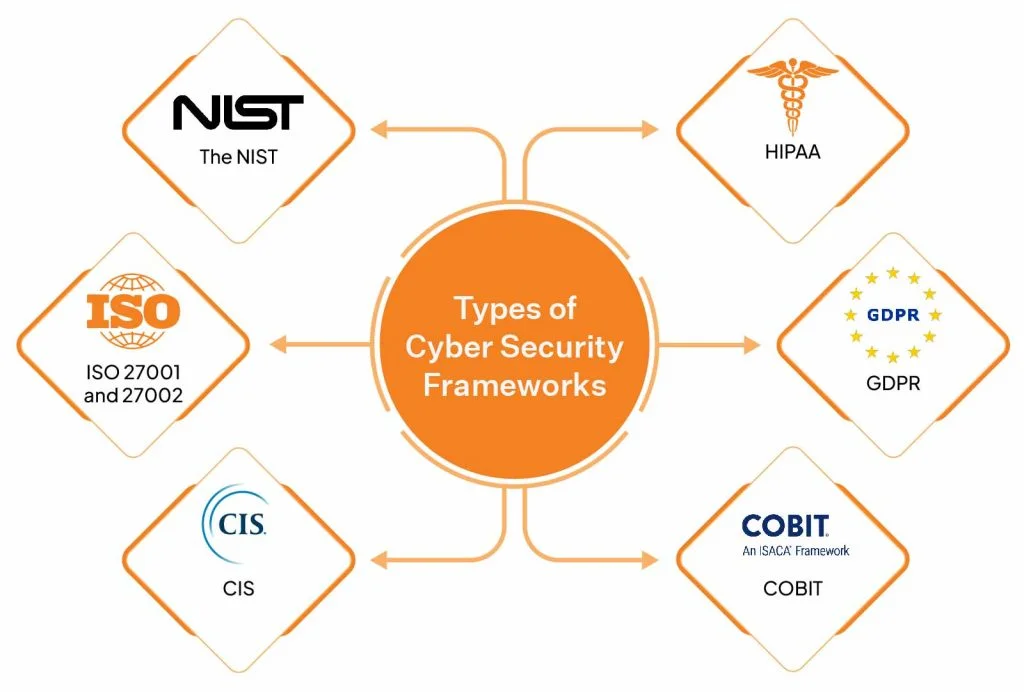
Privacy Regulations: Following are some known privacy regulations:
- GDPR (General Data Protection Regulation)
- CCPA (California Consumer Privacy Act)
- HIPAA Privacy Rule
- COPPA (Children’s Online Privacy Protection Act)
NIST announced in April 2025 that:
“It updates Privacy Framework, tying it to recent cybersecurity guidelines, recognizing that Privacy risk is closely related to, and often overlaps with, cybersecurity risk.”
Responsibility and Ownership
Security Responsibility: Typically falls to IT departments, security teams, and Chief Information Security Officers (CISOs). Security is seen as a technical function protecting infrastructure and systems.
Privacy Responsibility: Often managed by legal departments, compliance teams, and Chief Privacy Officers (CPOs) or Data Protection Officers (DPOs). Privacy is viewed as a governance and compliance function managing data rights and obligations.
However, effective programs require collaboration between security and privacy teams since they address interconnected challenges.
Success Metrics
Security Metrics:
- Number of prevented attacks
- Time to detect and respond to incidents
- Vulnerability patching speed
- System uptime and availability
- Compliance with security standards
Privacy Metrics:
- Consent rates and opt-in percentages
- Data subject request response times
- Privacy policy transparency scores
- Data retention compliance
- Privacy complaint numbers
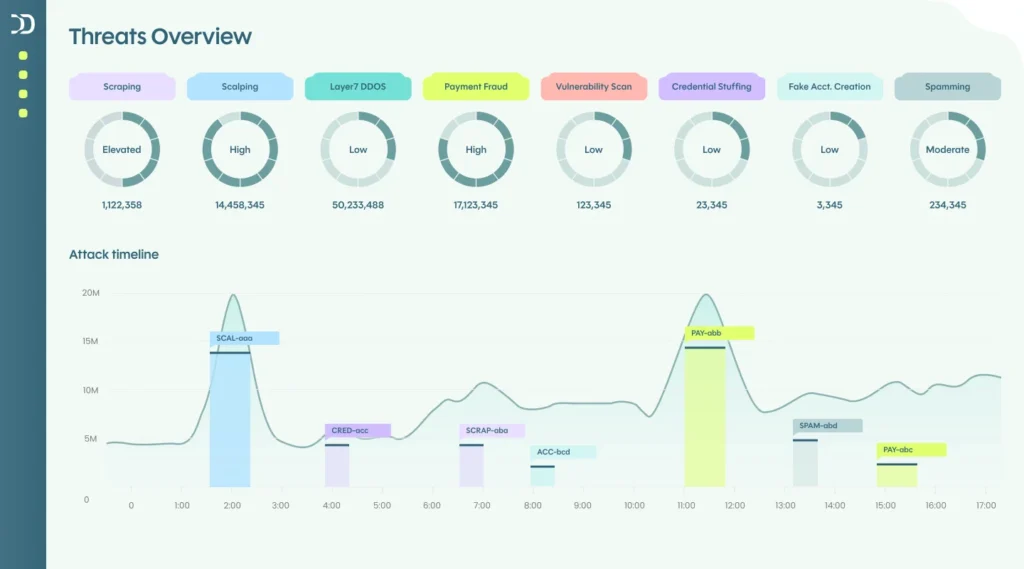
Source: DataDome – Cybersecurity and Data Protection
The Interconnection: Why You Need Both
While privacy and security differ, they’re deeply interconnected and mutually reinforcing:
Security Enables Privacy
You cannot have privacy without security. If your systems aren’t secure, unauthorized parties can access private information regardless of privacy policies.
Web Asha Technologies states:
“You need security to enforce privacy.”
Strong security measures are prerequisites for privacy protection. Encryption, access controls, and authentication mechanisms provide the foundation that privacy policies build upon.
Privacy Guides Security
Privacy requirements shape security implementations. Privacy laws mandate specific security controls, data protection impact assessments identify security risks, and consent requirements determine who should have access.
DataDome suggest that:
“Cybersecurity implements access and security protections.”
However, it doesn’t respond to all the types of user rights covered by privacy laws. For a comprehensive cybersecurity and data privacy program, you need to have the technologies, people, and processes to achieve all three requirements.
Real-World Examples of Interconnection
Healthcare Scenario: HIPAA includes both Security Rule (protecting patient data from breaches) and Privacy Rule (governing who can access records and for what purposes).
US Cybersecurity Magazine explains:
“The Security Rule requires protection of sensitive data against unauthorized access, while the Privacy Rule specifies who is granted authorization or has the right to grant authorization.”
Banking Example: Bank security systems prevent hackers from accessing accounts. Privacy rules determine which bank employees can view your transactions and prohibit sharing your financial information without consent.
Social Media Case: Platform security protects your account from unauthorized access. Privacy settings control which authorized users (your friends, the platform itself) can see your posts and how the platform uses your data.
The Risk of Focusing on Only One
Organizations that focus solely on security without privacy:
- May collect excessive data creating unnecessary risks
- Might violate privacy regulations despite strong security
- Could lose customer trust even with no breaches
- Face legal penalties for improper data use
Organizations that focus on privacy without security:
- Have policies that can’t be enforced without technical controls
- Remain vulnerable to breaches exposing private information
- Cannot fulfill privacy promises if systems are compromised
- Risk both security breaches and privacy violations
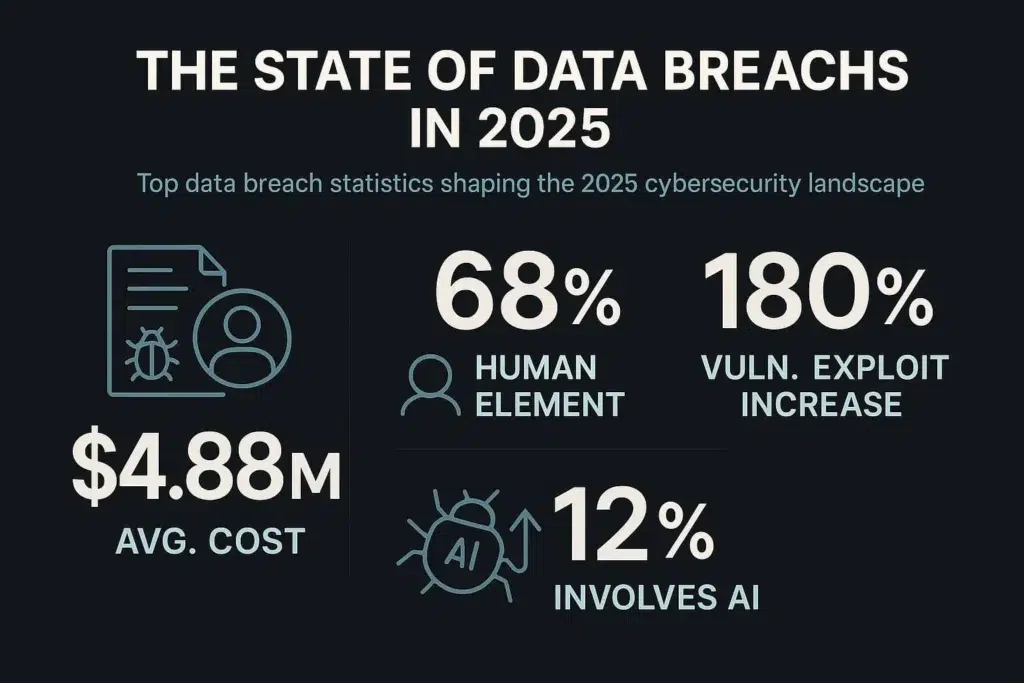
Source: Data Breaches 2025
Practical Implications for Organizations and Individuals
Understanding privacy versus security has practical applications:
For Organizations
Build Integrated Programs: Don’t treat privacy and security as separate initiatives. Create programs where security teams and privacy officers collaborate from the start.
Conduct Risk Assessments: Evaluate both security threats and privacy risks. Use frameworks like NIST’s Privacy Framework alongside its Cybersecurity Framework.
Implement by Design: Build privacy and security into products and services from inception rather than adding them later. Privacy by design and security by design should be standard practices.
Train Employees: Ensure staff understand both security procedures and privacy obligations. Many breaches result from employees who understand security but violate privacy through improper data use.
Balance Requirements: Sometimes privacy and security create tensions. For example, data minimization (privacy) versus logging for threat detection (security). Organizations must carefully balance competing requirements.
For Individuals
Use Security Tools: Employ strong passwords, multi-factor authentication, encryption, and antivirus software to protect your data from unauthorized access.
Exercise Privacy Rights: Review privacy policies, adjust privacy settings, opt-out of unnecessary data collection, and request deletion of data you no longer want shared.
Understand Limitations: Recognize that strong security doesn’t guarantee privacy. A secure platform can still misuse your data or share it with third parties.
Make Informed Choices: Consider both security and privacy when choosing services. A secure platform that shares your data extensively may be less desirable than a somewhat less secure one that respects privacy.
Stay Informed: Privacy laws and security threats constantly evolve. Stay current on your rights and emerging threats to make informed decisions.
Conclusion
Privacy and security are distinct but complementary concepts essential for protecting your digital life. Security focuses on defending systems and data against threats through technical controls, monitoring, and incident response. Privacy concerns controlling how personal information is collected, used, and shared through policies, consent, and individual rights.
The CIA Triad, which includes confidentiality, integrity, and availability, provides a framework showing how security and privacy intersect. Security protects confidentiality through technical controls, while privacy defines who should be authorized. Security maintains integrity through technical measures while privacy grants correction rights. Security ensures availability through redundancy, while privacy requires access to personal data.
Key differences include their focus (threats vs rights), questions addressed (protection vs control), implementation methods (technical vs governance), regulatory frameworks (security standards vs privacy laws), and success metrics. However, these differences don’t make privacy and security separate concerns; they’re deeply interconnected. You need security to enforce privacy, and privacy requirements guide security implementations.
For organizations, effective data protection requires integrated programs addressing both security threats and privacy obligations. For individuals, protecting yourself means using security tools while exercising privacy rights. Understanding the difference between privacy and security empowers you to make informed decisions about your digital protection in 2025’s complex technological landscape.
Frequently Asked Questions
What is the difference between privacy and security in 2025?
Why are privacy and security important for data protection?
Privacy and security protect your personal data from misuse and attacks. Security prevents breaches, while privacy ensures ethical use and compliance with global data protection laws like GDPR.
How does the CIA Triad relate to privacy and security?
The CIA Triad, which includes Confidentiality, Integrity, and Availability, links privacy and security by keeping data safe, accurate, and accessible while ensuring authorized and ethical information use.
What are examples of privacy and security working together?
