Phishing and Spear-Phishing have become the most dangerous cybercrime threats because they exploit human psychology rather than technical vulnerabilities.

According to AAG IT Support’s June 2025 statistics, phishing attacks continue to rise dramatically, with NordVPN reporting that “83% of organizations will experience at least one phishing attack annually in 2025.” Understanding how to recognize and prevent these attacks is essential for protecting yourself and your organization.
This guide explains what phishing is, the different types you’ll encounter, how to spot attacks, and proven prevention strategies.
Source: Phishing Statistics 2025
Understanding Phishing: What It Is and Why It Works
Phishing is a social engineering attack where criminals impersonate trusted entities to trick you into revealing sensitive information or clicking on malicious links. The term comes from “fishing” criminals fish for your valuable data using bait that looks legitimate.
Unlike technical hacking that exploits software vulnerabilities, phishing exploits human trust. Criminals create fake emails, websites, text messages, or phone calls that appear to come from banks, government agencies, or companies you know. When you interact with these communications, you unknowingly give criminals access to your accounts or systems.
The Psychology That Makes Phishing Effective
Phishing works because it manipulates fundamental human behaviors:
Trust: We naturally trust familiar brands and authority figures. Phishing messages impersonate entities we trust.
Urgency: False urgency, like “Your account will be closed!” or “Immediate action required!” bypasses normal caution.
Fear: Threats of account suspension or legal action trigger emotional responses that cloud judgment.
Curiosity: Messages about prizes or interesting information exploit our natural curiosity.
Helpfulness: Requests from colleagues or bosses exploit our desire to be helpful at work.
The Phishing Attack Process
Typical phishing attacks follow these steps:
Research: Criminals gather information about targets from social media, company websites, and data breaches.
Creating the Lure: Attackers create convincing fake communications that closely mimic legitimate ones using professional design and correct logos.
Delivery: The message reaches victims through email, text, social media, or phone calls.
Exploitation: Victims click links to fake websites that harvest credentials or download attachments containing malware.
Using Stolen Data: Criminals use stolen credentials to access accounts, steal money, commit fraud, or sell information on dark web marketplaces.
Types of Phishing Attacks You Need to Know
Phishing has evolved into many specialized forms:
Email Phishing (Mass Attacks)
Traditional email phishing sends mass messages to thousands of recipients. ControlD reports that:
“More than 3.4 billion phishing emails are sent daily.”
These generic attacks cast wide nets, hoping some victims will fall for the scam. Common scenarios include fake password reset requests, package delivery notifications, tax refund alerts, prize winnings, and account verification messages.
Spear-Phishing (Targeted Attacks)
Spear-phishing targets specific individuals with personalized messages. According to Astra Security:
“84% of US-based organizations experienced spear-phishing attacks,” making this extremely effective.
What makes spear-phishing dangerous is personalization. Criminals’ research targets on LinkedIn and Facebook to craft messages that reference real projects, colleagues, or situations. A spear-phishing email might mention your boss by name, reference an actual project, and use language consistent with your company’s style.
Spear-Phishing Example: An accountant receives an email appearing to be from the CEO requesting an urgent wire transfer for a confidential acquisition. The email uses the CEO’s real name, mentions an actual board meeting, and creates urgency. The accountant, believing it’s legitimate, transfers hundreds of thousands to criminals.
Whaling (Executive Targeting)
Whaling attacks target high-level executives like CEOs and CFOs. These attacks are meticulously researched and often impersonate other executives or legal authorities. The payoff can be enormous as executives have access to sensitive information, financial systems, and the authority to authorize large transactions.
Smishing (Text Message Phishing)
Smishing uses text messages to deliver attacks. SecurityScorecard suggests that:
“SMS attacks remain effective, especially when paired with spoofed caller IDs or fake urgency.”
Common smishing includes fake package delivery notifications, bank security alerts, prize winnings requiring clicks to claim, and government notifications about benefits. Smishing succeeds because people trust text messages more than email.
Vishing (Voice Phishing)
Vishing uses phone calls where criminals impersonate bank fraud departments, tech support from Microsoft or Apple, IRS officials threatening legal action, or company IT staff requesting passwords.
DeepStrike’s 2025 analysis reveals that:
“By March 2025, AI agents were 24% more effective at tricking users than human experts.”
This is because the AI can now clone voices convincingly.
QR Code Phishing (Quishing)
QR code phishing has emerged as a significant 2025 threat. Hoxhunt explains that:
“Criminals use QR codes in emails, posters, or fake parking tickets to direct victims to phishing websites.”
Security software can not scan QR codes like URLs, as users trust QR codes as modern technology. Also, mobile devices have fewer protections, and QR codes hide destinations until after scanning.
According to Norton LifeLock:
“Fake parking tickets with QR codes for payment, restaurant menus that steal credit cards, email attachments requiring mobile QR scans, and fake delivery notices with rescheduling QR codes.”
Business Email Compromise (BEC)
BEC involves criminals compromising or impersonating business email accounts to conduct fraud.
TechMagic reports that:
“BEC is one of the most common phishing scams.”
BEC attacks target finance departments with requests to change vendor payment accounts, process urgent wire transfers, update employee direct deposits, or pay fake invoices. The FBI reports BEC causes billions in losses because requests appear legitimate.

Source: Types of Phishing
Phishing Statistics: Understanding the 2025 Threat Landscape
Current statistics reveal the scale of phishing attacks:
Attack Volume
Phishing has reached unprecedented levels. Astra Security data reveals that:
“Highly impersonated brands for phishing are Amazon and Google at 13%, Facebook and WhatsApp at 9%, and Netflix and Apple at 2%.”
AI-Powered Phishing Evolution
AI integration has made phishing dramatically more effective. DeepStrike reports that:
“AI agents were 24% more effective at tricking users than human experts by March 2025.”
AI enables criminals to generate convincing emails at scale, personalize messages, create deepfake audio/video, translate perfectly, and adapt in real-time.
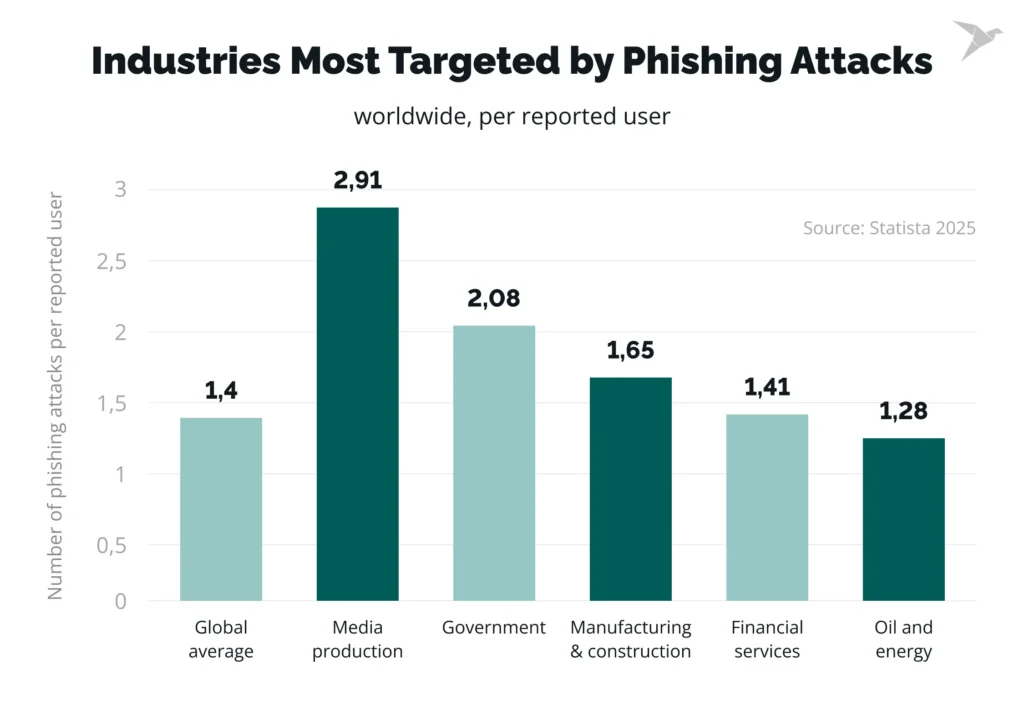
Industry Targeting
Finance offers direct money access, healthcare has valuable medical records, technology holds intellectual property, education has large user bases with limited budgets, and government stores sensitive information.
According to TechMagic:
“Finance, healthcare, and technology are prime targets.”
Financial Impact
Phishing causes billions in losses through direct theft, ransomware deployment, BEC fraud, credential theft, enabling further attacks, recovery costs, regulatory fines, and reputation damage.
Red Flags and Warning Signs
Recognizing phishing is your first defense. Here are critical warning signs:
Suspicious Sender Information
Check email addresses carefully. Phishing emails use addresses that look similar but have differences: michaelsoft.com instead of microsoft.com, paypa1.com (number 1 instead of L), amaz0n.com (zero instead of O), or extra characters like support-apple.com.
Adaptive Security points out that:
“Genuine companies send from official domains, not Gmail or Yahoo.”
Generic Greetings
AZTech IT notes that:
“Generic greetings are obvious red flags.”
Legitimate companies use your name. Phishing says “Dear Customer,” “Dear User,” or “Valued Client.”
False Urgency
Phishing creates artificial urgency: “Your account will be closed in 24 hours,” “Immediate action required,” “Suspicious activity—verify now,” “Final notice,” or “Limited time offer.” Legitimate companies provide reasonable timeframes.
Requests for Sensitive Information
Adaptive Security emphasizes that:
“Requests for sensitive information are huge red flags.”
Legitimate organizations never ask for passwords, social security numbers, credit card numbers, account verification codes, or security answers via email.
Suspicious Links and Attachments
Before clicking links, hover to see actual URLs. Look for misspelled domains, extra characters, unusual country codes, or IP addresses instead of names.
IT Governance warns that:
“Phishing links lead to credential harvesting pages, malware downloads, or fake information forms.”
Poor Grammar and Spelling
While AI has improved quality, many attacks contain spelling mistakes, awkward grammar, unusual word choices, inconsistent formatting, or mixed fonts. Professional organizations proofread communications.
QR Code Red Flags
Norton LifeLock identifies malicious QR code signs: stickers over existing codes, low-quality printing, unexpected locations, lack of official branding, and peeling edges suggesting recent addition.
Unexpected Attachments
Be suspicious of unsolicited attachments, especially .exe, .zip, .rar files, macros-enabled documents, JavaScript files, or PDFs from unknown senders. Legitimate businesses rarely send unsolicited attachments.
Source: Identify Phishing
Enterprise Security Training and Prevention
Organizations need comprehensive training and controls:
Security Awareness Training Programs
Effective training includes:
Regular Simulations: Send simulated phishing to test vigilance. Hoxhunt’s 2025 report shows regular simulations significantly improve detection rates.
Immediate Feedback: When employees click on simulated phishing, provide immediate training explaining what they missed.
Gamification: Make training engaging through competitions, rewards for reporting, and team challenges.
Real Examples: Show actual phishing your organization received and discuss dangers.
Quarterly Updates: Conduct training at least quarterly with updates for new tactics.
Technical Security Controls
Implement technical defenses:
Email Filtering: Deploy advanced email security that blocks malicious senders, scans attachments, analyzes links, quarantines suspicious messages, and uses AI for anomaly detection.
Multi-Factor Authentication: Require MFA on all accounts. Even if phishing steals passwords, MFA prevents access. Use app-based or hardware tokens over SMS.
Email Authentication: Implement SPF, DKIM, and DMARC to prevent email spoofing and verify sender authenticity.
Browser Security: Use browsers with built-in phishing protection and enable warnings for malicious sites.
Endpoint Protection: Deploy EDR solutions that detect and block malware delivered through phishing.
Incident Response Procedures
Establish procedures for handling suspected phishing:
Easy Reporting: Provide simple reporting methods like phishing report buttons or dedicated email addresses.
Rapid Response: Review reported emails quickly and act when threats are confirmed.
Communication: Alert employees when active phishing campaigns target your organization.
No Punishment: Never punish employees who report phishing, even if they clicked. Reward reporting.
Personal Protection Strategies
Individuals can protect themselves in the following manner:
Verify Before Acting
When receiving unexpected messages, contact organizations directly using official website phone numbers, don’t use contact information from suspicious messages, log into accounts by typing URLs yourself, and question if requests make sense.
Enable Security Features
Turn on multi-factor authentication everywhere, use password managers for strong, unique passwords, enable login alerts, and set up biometric authentication when possible.
Keep Software Updated
Ensure devices have current operating system updates, browser updates, security software updates, and application updates. Updates include patches for vulnerabilities, phishing-delivered malware exploits.
Use Caution with QR Codes
According to TechTarget’s prevention guide, inspect QR codes for tampering, verify URLs after scanning, be suspicious of codes in emails or unexpected locations, and use scanner apps that show URLs before opening.
Limit Social Media Information
Review privacy settings on all platforms, limit who sees posts and contact info, be cautious about what you share publicly, and don’t post about work projects, travel, or finances.
Monitor Your Accounts
Regularly check bank statements for unauthorized transactions, credit reports for fraudulent accounts, email login activity, and social media access logs. Early detection limits damage.
Conclusion
Phishing remains the most prevalent cybersecurity threat in 2025, with 83% of organizations experiencing attacks annually. From traditional email phishing to sophisticated spear-phishing, vishing, smishing, and QR code attacks, criminals continuously evolve tactics exploiting human trust. AI has made attacks 24% more effective than human-crafted attempts, creating unprecedented challenges.
However, you can protect yourself and your organization by learning to recognize warning signs: suspicious sender addresses, generic greetings, false urgency, requests for sensitive information, and suspicious links or attachments. When in doubt, verify through independent channels before taking action.
Organizations should implement comprehensive security awareness training with regular phishing simulations, technical controls like email filtering and multi-factor authentication, and clear incident response procedures. Individuals should verify before acting, enable security features, keep software updated, and limit information shared online.
The fight against phishing requires constant vigilance and ongoing education. Criminals invest significant resources into making attacks more convincing, but informed, cautious users remain the strongest defense. Stay skeptical, verify carefully, and report suspicious activity promptly. Your awareness is the best protection against phishing attacks.
Glossary of Phishing Terms
Business Email Compromise (BEC): Phishing targeting businesses through compromised or impersonated email accounts
Credential Harvesting: Stealing usernames and passwords through fake login pages
Email Spoofing: Forging email headers to make messages appear from trusted sources
Phishing: Social engineering attacks using fake communications to steal information
Quishing: QR code phishing using malicious QR codes directing victims to phishing sites
Smishing: SMS/text message phishing attacks
Social Engineering: Manipulating people into revealing information or taking harmful actions
Spear-Phishing: Targeted phishing against specific individuals using personalized messages
Vishing: Voice phishing using phone calls to trick victims
Whaling: Phishing attacks specifically targeting executives and high-level individuals
Frequently Asked Questions
What’s the difference between phishing and spear-phishing?
Phishing is a broad attack where scammers send fake emails or messages to many people, hoping someone takes the bait. Spear-phishing, on the other hand, targets specific individuals or organizations using personalized details like job titles or colleagues’ names. It is much more convincing and harder to detect because it feels genuine.
Both aim to steal personal information, credentials, or money.
How has AI changed phishing in 2025?
Attackers now use AI to create highly realistic emails, voice messages, and even deepfake videos. These tools remove spelling errors and mimic real communication styles, making scams far more believable. AI also helps hackers send thousands of personalized phishing messages in seconds. As a result, detection requires smarter AI-driven security tools and stronger user awareness.
How can I quickly spot a phishing or spear-phishing attempt?
Always check the sender’s full email address and not just the display name. Hover over links before clicking and verify if the URL matches the legitimate site. Be cautious of urgent or emotional language pushing you to act quickly. If a message seems odd, confirm it with the sender through another channel, like a phone call.
What are the best ways to prevent phishing attacks?
Enable phishing-resistant multi-factor authentication (like passkeys or security keys). Implement SPF, DKIM, and DMARC email security standards to block spoofed messages. Train employees regularly using simulated phishing tests. Use AI-based email filters and sandboxing tools to detect malicious links or attachments.
What should I do if I think I have been phished?
Stop interacting with the suspicious message immediately. Disconnect your device from the internet and change your passwords using a secure device. Notify your IT or security team and share the full email details for analysis. Run antivirus scans, monitor for unusual activity, and report the incident to relevant authorities.
