A global analysis of how intellectual property and cybersecurity laws are shaping digital policy in 2025, including key legal trends and regulatory shifts.
Intellectual property (IP) and cybersecurity laws sit at the core of global digital policy in 2025. As cyber threats escalate, artificial intelligence reshapes innovation, and cross-border data flows expand, governments are tightening legal frameworks that govern how digital assets are created, protected, and secured.
What were once treated as separate legal domains are now deeply interconnected. IP protection increasingly depends on cybersecurity compliance, while cybersecurity failures often result in intellectual property loss, regulatory scrutiny, and legal liability. This article provides a clear, global analysis of how IP and cybersecurity laws are evolving, where regulatory approaches diverge, and what these shifts mean for businesses, policymakers, and the future of the digital economy
According to Cornell Law School:
“The Digital Millennium Copyright Act (DMCA) represents a federal statute addressing copyright issues arising from digital technology and the internet.”
The Digital Millennium Copyright Act (DMCA) was enacted in 1998 and remains the cornerstone of digital copyright protection in the United States.
According to WIPO:
“IP rights are valuable assets for businesses and individuals, protecting innovative ideas, technology solutions, brands, and creative works.”
This helps in understanding the intersection of IP law and cybersecurity, which has become essential for protecting digital assets in 2025.

Source: WIPO – IP Protection System
Understanding IP in the Digital Age
Intellectual property in the digital realm encompasses creative works, inventions, brands, and proprietary information stored, transmitted, or distributed through digital channels. The fundamental challenge is that digital IP can be copied perfectly and distributed globally in seconds a reality that traditional IP laws written for physical goods never anticipated.
Wikipedia explains that the DMCA:
“Criminalizes production and dissemination of technology, devices, or services intended to circumvent measures that control access to copyrighted works (commonly known as digital rights management or DRM).”
This anti-circumvention provision represents a significant evolution in IP protection for the digital age. The digital transformation has created new IP challenges:
- Easy Replication: Digital files can be copied infinitely without quality loss
- Global Distribution: Content shared online reaches worldwide audiences instantly
- Anonymity: Online infringers can hide identities and locations
- Speed: Piracy occurs at unprecedented velocity
- Scale: Single actors can infringe millions of copyrights simultaneously
These challenges require legal frameworks that balance rightsholder protection with technological innovation and public access to information.
Core IP Categories and Online Challenges
Copyright and Digital Content
Copyright protects original creative works fixed in tangible form books, music, movies, software, and digital art.
The Law to Know explains that:
“Under the TRIPS Agreement, copyright terms must extend at least 50 years, establishing minimum global protection standards.”
Online challenges include streaming piracy, unauthorized downloads, content aggregation sites, and deepfake technology creating derivative works. Social media platforms face constant battles with users uploading copyrighted content without permission.
Trademarks and Brand Protection
Trademarks identify goods and services sources, building brand recognition and consumer trust. Online trademark challenges include:
- Cybersquatting (registering domain names with trademarked terms)
- Counterfeit goods sold through e-commerce platforms
- Social media impersonation accounts
- Search engine advertising using competitor trademarks
- Typosquatting (similar domains exploiting typos)
Patents and Trade Secrets
Patents protect inventions, granting exclusive rights for typically 20 years. Trade secrets encompass confidential business information like formulas, processes, and strategies.
TRIPS recognizes:
“Trade secrets as a form of intellectual property… obliging members to protect confidential business information from unauthorized disclosure or acquisition.”
Cyber threats to patents and trade secrets include corporate espionage, hacking to steal designs, employee data theft, and supply chain compromises exposing proprietary information.
Industrial Designs and Digital Products
Industrial designs protect ornamental or aesthetic aspects of products. In the digital realm, this includes user interfaces, website layouts, and digital product appearances. Cybersecurity concerns involve design theft, unauthorized reproduction, and reverse engineering of protected designs.
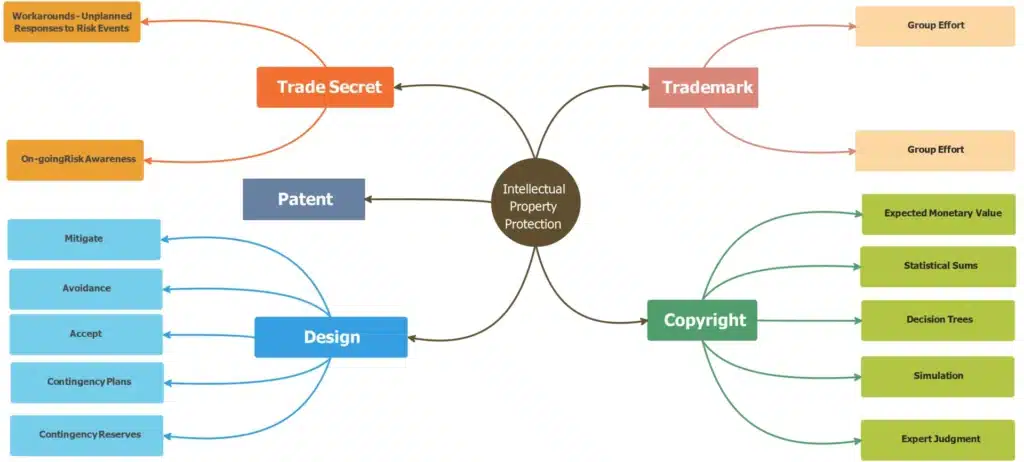
Source: Intellectual Property Categories
Why IP and Cybersecurity Laws Matter More in 2025
Several forces are driving heightened regulatory attention in 2025:
- AI-driven innovation has increased the value and vulnerability of software, algorithms, and proprietary data.
- Rising cybercrime, including ransomware and IP theft, is targeting both private companies and critical infrastructure.
- Digital trade and data flows increasingly cross borders, complicating enforcement and compliance.
- Economic dependence on digital assets has made IP protection and cybersecurity matters of national policy.
As a result, lawmakers are strengthening enforcement mechanisms and expanding compliance obligations across sectors.
How Intellectual Property Laws Are Evolving Globally
Expansion of Digital IP Protections
In 2025, IP laws have been increasingly focused on digital-first assets. Governments are clarifying protections for software, databases, AI-assisted creations, and proprietary algorithms. Trade secret laws are also being reinforced to address data exfiltration and insider threats, which often occur through cyber intrusions rather than traditional corporate espionage. Online copyright enforcement has also expanded, with greater scrutiny on digital platforms that host or distribute protected content.
Enforcement Challenges in the Digital Economy
Despite stronger laws, enforcement remains complex. Cross-border infringement, anonymous actors, and jurisdictional limits make IP violations difficult to prosecute. Policymakers are increasingly debating platform liability, notice-and-takedown standards, and the balance between innovation and rights enforcement.
Mandatory Security and Breach Reporting
Many jurisdictions now require organizations to adopt minimum security standards and report cyber incidents within defined timeframes. These obligations are designed to improve transparency, reduce systemic risk, and protect users whose data or digital assets may be compromised. Failure to comply can result in significant fines, operational restrictions, or legal exposure.
Protection of Critical Digital Infrastructure
Cybersecurity regulation increasingly prioritizes sectors considered essential to national stability, including finance, healthcare, telecommunications, and energy. Supply-chain security requirements are also expanding, placing responsibility on organizations to assess and manage third-party risks.
Key International IP Frameworks
World Intellectual Property Organization (WIPO)
WIPO, established in 1967, administers international IP treaties and promotes IP protection globally. WIPO, a specialized United Nations agency with 193 member states, administers international IP treaties and promotes IP protection globally. WIPO provides services including international patent and trademark filing systems, dispute resolution for domain names, and technical assistance to developing countries.

WIPO’s mission encompasses:
“Promoting effective and balanced IP enforcement that respects due process and fundamental freedoms.”
Key WIPO treaties include:
- Paris Convention for the Protection of Industrial Property (1883) covers patents, trademarks, and industrial designs across 177 countries. It establishes national treatment requiring countries to grant foreign nationals the same IP protection as their own citizens.
- Berne Convention for the Protection of Literary and Artistic Works (1886) protect copyrights internationally across 181 countries. Works created in one member country receive automatic protection in all other member countries without registration requirements.
- Patent Cooperation Treaty (PCT) simplifies international patent filing. A single PCT application provides a pathway to seeking patent protection in over 150 countries, though each country ultimately decides whether to grant protection.
- Madrid System for international trademark registration allows trademark owners to protect marks in multiple countries through one application in one language with one set of fees.
The 1996 WIPO treaties, often called “Internet Treaties,” specifically address digital challenges by establishing rights for online transmission and requiring protection against circumvention of technological protection measures.
TRIPS Agreement – Trade-Related Aspects of IP Rights
The TRIPS Agreement, entering into force in 1995 as part of the WTO framework, revolutionized international IP law. The Agreement on Trade-Related Aspects of Intellectual Property Rights (TRIPS), administered by the World Trade Organization, sets minimum IP protection standards for all WTO members (164 countries). TRIPS covers copyrights, trademarks, patents, trade secrets, and enforcement mechanisms, making IP protection a condition of international trade participation.
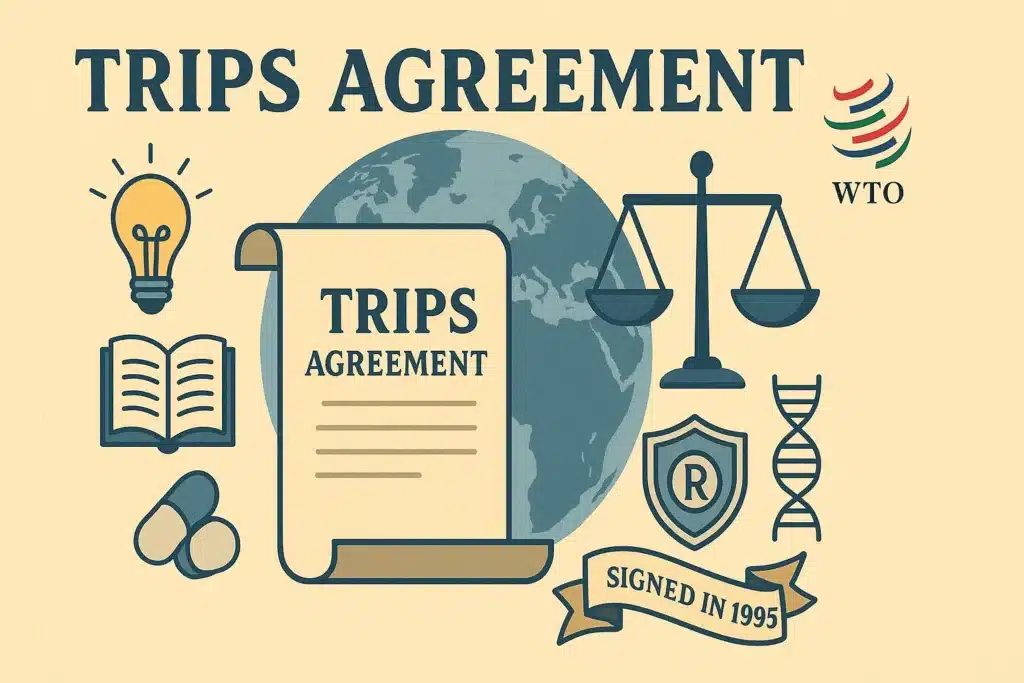
TRIPS requires member countries to provide both substantive protection (minimum standards for each IP type) and procedural protections (enforcement procedures including civil remedies, border measures, and criminal penalties for commercial-scale infringement).
The Law to Know notes that:
“TRIPS marks the first time intellectual property was treated as a matter of international trade, linking economic liberalization with the enforcement of intangible rights.”
TRIPS establishes minimum standards for:
- Copyright and related rights (50-year minimum term)
- Trademarks (renewable protection)
- Patents (20-year minimum term from filing)
- Industrial designs
- Geographical indications
- Trade secrets
- Layout designs of integrated circuits
Critically, TRIPS Part III:
“broke new ground in multilateral law by setting out general principles for the enforcement of IP rights.”
This requires WTO members to provide effective civil, criminal, and border enforcement procedures.
Unlike earlier WIPO treaties, TRIPS includes binding dispute resolution through the WTO Dispute Settlement Body, with non-compliance potentially leading to trade sanctions. This enforcement mechanism gives TRIPS unprecedented power in international IP protection.
Regional IP Laws and Enforcement
United States: DMCA and Copyright Framework
The Digital Millennium Copyright Act remains the cornerstone of US digital copyright protection.
Cornell Law explains that:
“DMCA implemented the World Intellectual Property Organization (WIPO) Copyright Treaty of 1996 into U.S. law.”
DMCA Title I – Anti-Circumvention Provisions: Section 1201 prohibits circumventing technological protection measures (TPMs) controlling access to copyrighted works.
Duke Law notes that:
“Section 1201 stops distribution of tools used to upset TPMs, creating controversial restrictions that sometimes hinder legitimate security research.”
DMCA Safe Harbor Provisions: Justia explains that:
“DMCA provides safe harbors from liability for online service providers when their users post or transmit copyright-infringing materials.”
To qualify, service providers must:
- Lack knowledge of infringing material
- Not receive direct financial benefit from infringement
- Respond promptly to takedown notices
- Implement repeat infringer policies
DMCA Takedown Process: Cloudwards describes the takedown process where copyright holders send notices to service providers identifying infringing content. Providers must remove material expeditiously upon receiving proper notice, notify uploaders, and restore content if counter-notices demonstrate legitimate use.
Controversies and Security Research: The DMCA’s anti-circumvention provisions have sparked debate.
Duke Law Research indicates that:
“Security researchers battle against the DMCA because Section 1201 prevents circumvention even for legitimate cybersecurity research, potentially leaving vulnerabilities unaddressed.”
Lanham Act: This act governs federal trademark law, providing trademark registration, infringement remedies, and protection against counterfeiting and cybersquatting.
Patent Act: The Act (Title 35 USC) governs patent rights with recent America Invents Act reforms transitioning to a first-to-file system and creating post-grant review procedures.
Economic Espionage Act and Defend Trade Secrets Act provide criminal and civil remedies for trade secret theft, including up to 15 years imprisonment and substantial damages.
Latin American IP Protection
Latin American countries participate in regional IP systems:
Andean Community Decision 486 creates common IP regime for Bolivia, Colombia, Ecuador, and Peru covering patents, trademarks, and industrial designs.
MERCOSUR coordinates IP protection among Argentina, Brazil, Paraguay, and Uruguay through various protocols.
Individual countries maintain national laws: Brazil’s Industrial Property Law and Copyright Law, Mexico’s Industrial Property Law and Federal Copyright Law, and Argentina’s Patent Law and Trademark Law.
European Union: EUIPO Digital Enforcement Rules
The EU has harmonized IP protection across member states through various directives and regulations:
EU Trade Secrets Directive (2016) harmonizes trade secret protection across the EU, defining trade secrets and providing remedies for misappropriation including injunctions and damages.
EU Copyright Directive (2019) updated copyright rules for the digital age, including provisions for online content sharing platforms, press publishers’ rights, and text and data mining exceptions. Article 17 requires platforms to obtain licenses or remove copyrighted content.
European Patent Convention enables patent protection across 39 European countries through a single application, though individual countries grant patents.
EU Trademark Regulation provides unitary trademark protection across all EU member states through a single registration.
The European Union Intellectual Property Office (EUIPO) oversees EU trademarks and designs. EU IP enforcement operates through several directives:
InfoSoc Directive (2001/29/EC): Harmonizes copyright and related rights, including reproduction, communication to the public, and distribution rights for the digital environment.
Enforcement Directive (2004/48/EC): Establishes civil enforcement procedures including injunctions, damages, and the right of information, allowing right holders to identify infringers.
E-Commerce Directive (2000/31/EC): Provides liability limitations for internet intermediaries similar to DMCA safe harbors.
WIPO’s 2025 analysis suggests that the Court of Justice of the European Union (CJEU) decisions have clarified site-blocking orders, establishing that:
“Courts ensure site blocking is a balanced and necessary response to piracy while respecting fundamental rights.”
Asia-Pacific: Emerging Enforcement Models
Asian countries have significantly strengthened IP protection in recent decades:
China: China has reformed IP laws extensively, including Copyright Law amendments (2020) increasing damages for infringement, Patent Law revisions (2020) introducing patent term extensions and strengthening enforcement, Trademark Law updates (2019) increasing penalties and combating bad faith registrations, and Civil Code provisions (2021) establishing comprehensive IP protection.
Japan: Japan maintains strong IP protection through the Copyright Act, protecting works for the author’s life plus 70 years, Patent Act providing 20-year patent protection from filing, Trademark Act offering renewable 10-year trademark protection, and Unfair Competition Prevention Act protecting trade secrets and combating counterfeiting. Copyright law provides strong protection for digital content, with particular focus on manga, anime, and gaming industries. Japan actively enforces anti-piracy measures and participates in international IP cooperation.
Singapore: The Intellectual Property Office of Singapore (IPOS) administers comprehensive IP protection including site-blocking orders for persistent copyright infringement. Singapore has implemented strong enforcement mechanisms aligned with international standards.
India: India has modernized IP laws, including the Patents Act (amended 2005), complying with TRIPS, Copyright Act (amended 2012) addressing digital issues, Trademarks Act (1999) providing comprehensive trademark protection, and Information Technology Act addressing cyber-IP issues. The Copyright Act 1957 (as amended) addresses digital challenges, with courts issuing dynamic injunctions allowing right holders to block infringing websites. Indian law increasingly addresses streaming piracy and online trademark infringement.
South Korea: Strong copyright enforcement supports the K-pop and entertainment industries, with active government cooperation in combating online piracy.
Middle East: Developing IP Frameworks
United Arab Emirates: UAE Copyright Law protects digital works, with increasing enforcement against online piracy. The UAE has established specialized IP courts and strengthened border measures against counterfeit goods.
Saudi Arabia: The Saudi Authority for Intellectual Property (SAIP) modernizes IP protection, implementing digital enforcement mechanisms and international cooperation protocols. Saudi Arabia has significantly strengthened IP protection as part of its Vision 2030 economic diversification program.
Both countries have signed international treaties and are enhancing enforcement capabilities to attract foreign investment and support domestic innovation.
Cyber Law Updates: Recent Developments in Online IP Protection
Recent legislative and regulatory developments reflect evolving digital challenges:
EU Digital Services Act and Digital Markets Act (2023-2024)
The Digital Services Act creates obligations for online platforms including content moderation requirements, transparency in algorithms, protection against illegal content, and user rights including appeals.
The Digital Markets Act regulates “gatekeeper” platforms to ensure fair competition and includes provisions affecting IP licensing and data portability.
US Copyright Office AI Guidance (2023-2025)
The Copyright Office has issued guidance on AI-generated works stating that works created by AI without human authorship cannot be copyrighted, human selection and arrangement of AI-generated elements may qualify for copyright, and registration applications must disclose AI-generated content.
WIPO AI and IP Policy Developments
WIPO has undertaken extensive consultations on IP and AI including inventorship and ownership of AI-generated inventions, copyright in AI-generated works, data protection and IP, and liability for AI systems infringing IP.
International Enforcement Cooperation
Countries have increased cooperation on cross-border IP enforcement through Interpol’s IP Crime Programme coordinating investigations, customs cooperation sharing intelligence and conducting joint operations, and mutual legal assistance treaties facilitating evidence gathering.
Budapest Convention: Addressing Cyber IP Crimes
The Council of Europe’s Convention on Cybercrime (Budapest Convention), effective since 2004, represents the primary international treaty addressing cybercrime including IP theft.
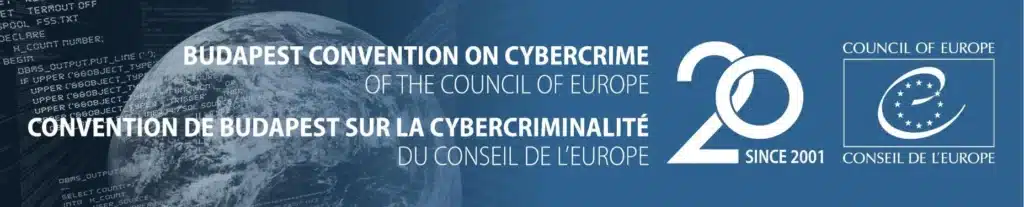
Coverage: The Convention covers computer-related offenses including copyright infringement, related rights infringement, and trademark infringement when committed through computer systems.
Procedural Powers: It establishes procedures for investigating cybercrimes including expedited preservation of computer data, production orders for electronic evidence, search and seizure of data, and real-time collection of traffic data.
International Cooperation: The Convention requires parties to provide mutual assistance including extradition for cybercrimes, preservation of stored data across borders, and sharing of investigative information.
Current Status: 68 countries have ratified the convention including the US, most European countries, and several others globally.
Handling Online Piracy, Counterfeiting, and Patent Theft
Detecting IP Infringement
Modern enforcement combines technological and legal approaches:
- Digital Fingerprinting: Identifying copyrighted content through automated comparison
- Web Scraping: Monitoring e-commerce platforms for counterfeit goods
- Brand Protection Services: Specialized firms monitoring trademark misuse
- Patent Monitoring: Tracking competitor product launches for potential infringement
Enforcement Actions
Cease and Desist Letters: Initial notices demanding infringement cessation before litigation.
DMCA Takedowns: For US-hosted content, copyright holders can request expedited removal through DMCA procedures.
Court Proceedings: Civil lawsuits seeking injunctions, damages, and destruction of infringing goods.
TRIPS requires that:
“WTO members make available effective, balanced and fair procedures.”
Site Blocking Orders: Courts can order ISPs to block access to persistent infringement sites. This remedy has gained traction globally despite concerns about overblocking.
Criminal Prosecution: For commercial-scale infringement, many jurisdictions provide criminal penalties including imprisonment. TRIPS mandates criminal procedures for willful trademark counterfeiting and copyright piracy on commercial scale.
Border Measures: Customs authorities can seize counterfeit goods at borders.
WIPO enforcement guidance emphasizes:
“The importance of border measures, criminal procedures, and penalties in comprehensive enforcement strategies.”
Challenges in Cross-Border Enforcement
Global infringement creates jurisdictional challenges. Infringers operate from jurisdictions with weak IP protection, making enforcement difficult. International cooperation through TRIPS, WIPO, and bilateral agreements facilitates cross-border enforcement, but significant gaps remain.
Legal Remedies and Court Precedents
Civil Remedies
IP holders can pursue various civil remedies:
Injunctions: Court orders preventing further infringement. Preliminary injunctions stop infringement during litigation; permanent injunctions provide ongoing protection.
Damages: Monetary compensation for losses. This includes actual damages (provable economic harm) plus infringer profits, or statutory damages (predetermined amounts per infringement).
Destruction Orders: Courts can order destruction of infringing goods and tools used to create them.
Right of Information: Rightholders can compel infringers to identify suppliers, distributors, and customers involved in infringement.
Criminal Penalties
Criminal IP enforcement addresses willful, commercial-scale infringement. Penalties include fines, imprisonment, and asset forfeiture. The DMCA includes criminal penalties for willfully circumventing TPMs for commercial advantage or private financial gain.
Landmark Cases
Chamberlain Group v. Skylink Technologies: This case clarified DMCA’s anti-circumvention provisions, establishing that circumvention alone doesn’t violate DMCA without underlying copyright infringement. Courts ruled DMCA doesn’t create new property rights beyond copyright itself.
Viacom v. YouTube: This major case tested DMCA safe harbor provisions, ultimately establishing that service providers can qualify for protection even when aware of general infringement if they lack specific knowledge of particular infringing content.
CJEU Site-Blocking Decisions: European courts have developed extensive jurisprudence on site-blocking orders, balancing IP protection with fundamental rights including freedom of expression and internet access.
These precedents shape how courts interpret and apply IP laws in cybersecurity contexts, establishing balances between rightsholder protection and legitimate interests of users, researchers, and service providers.
Challenges in Global Online IP Protection
Despite extensive legal frameworks, significant challenges remain:
Jurisdictional Complexity
Determining which country’s laws apply when infringement involves multiple countries creates complexity. Questions arise about where infringement occurred, which courts have jurisdiction, which country’s laws govern, and how to enforce judgments across borders.
Enforcement Limitations
Even with favorable judgments, enforcement proves difficult when infringers operate from countries with weak IP protection, use anonymous services hiding identities, constantly change domains and servers, or have no assets in jurisdictions where judgments are obtained.
Technological Evolution
New technologies create challenges faster than laws can adapt including AI-generated content raising authorship questions, blockchain and NFTs creating new distribution models, deepfakes enabling sophisticated infringement, and streaming technologies facilitating real-time piracy.
Developing Country Concerns
Developing countries often face tensions between IP protection and access to knowledge, technology transfer and local innovation, traditional knowledge protection, and balancing IP protection with public health and education needs.
Future of IP Law in Cybersecurity
The IP-cybersecurity intersection continues evolving rapidly:
Artificial Intelligence and IP
AI generates content raising novel IP questions such as:
- Who owns AI-created works?
- Can AI infringe copyright?
- How do we protect training datasets containing copyrighted works?
EFF suggests that:
“Section 1202 restrictions on removing copyright management information are being applied to AI training, creating new enforcement frontiers.”
Blockchain and NFTs
Non-fungible tokens (NFTs) create digital ownership records but don’t necessarily transfer IP rights. Courts are beginning to address NFT-related IP disputes, establishing that owning an NFT doesn’t automatically grant copyright ownership of the underlying work.
3D Printing and Digital Manufacturing
3D printing enables easy reproduction of patented inventions and protected designs from digital files. IP law must adapt to address distributed manufacturing where infringement occurs at endpoint rather than centralized production.
Cybersecurity Research Exemptions
Growing recognition that cybersecurity requires circumventing protection measures has led to periodic DMCA exemptions for security research.
Duke Law argues for permanent solutions, suggesting:
“Combining legislative reform with best practices like bug bounty programs to support legitimate security research.”
International Harmonization
While complete global harmonization seems unlikely, core principles continue converging. Future developments may include updated WIPO treaties addressing AI, strengthened enforcement cooperation, and balanced approaches protecting both innovation and IP rights.
Digital-First Legislation
New laws specifically designed for digital environments including platform liability frameworks, AI and IP-specific regulations, and digital content licensing systems.
Alternative Dispute Resolution
Growth in ADR mechanisms for IP disputes including WIPO Arbitration and Mediation Center, domain name dispute resolution (UDRP), and online dispute resolution platforms.
Where Intellectual Property and Cybersecurity Laws Intersect
The intersection of IP and cybersecurity law is now a defining feature of global digital policy. Cyberattacks frequently aim to steal trade secrets, source code, or proprietary datasets.
As a result:
- IP owners are expected to implement adequate cybersecurity safeguards.
- Data breaches involving protected IP may trigger both cyber and IP liability.
- Courts and regulators increasingly view security failures as contributing factors in IP loss.
In practice, effective IP protection in 2025 depends heavily on robust cybersecurity compliance.
What Policymakers and Companies Should Watch Next
Looking ahead, several trends are likely to shape digital policy beyond 2025:
- Disputes over AI-generated content and IP ownership
- Expanded cybercrime penalties and enforcement cooperation
- Tighter rules governing cross-border data transfers
- Ongoing tension between regulatory harmonization and national control
Organizations that align legal, technical, and governance strategies will be better positioned to adapt. For businesses operating across borders, the convergence of IP and cybersecurity laws creates new challenges:
- Higher compliance and operational costs
- Increased legal exposure following cyber incidents
- Need for jurisdiction-specific compliance strategies
- Greater emphasis on internal governance and risk management
Companies are increasingly expected to treat cybersecurity as a legal obligation tied directly to IP stewardship.
Conclusion
In 2025, intellectual property and cybersecurity laws function as a single regulatory framework shaping global digital policy. Governments now view digital security, innovation protection, and economic resilience as inseparable legal priorities. The legal frameworks governing this space, anchored by the DMCA in the US, TRIPS internationally, and regional implementations globally, continue evolving to address emerging technologies and threats.
For businesses and digital platforms, this convergence raises the stakes. IP protection without cybersecurity safeguards is increasingly insufficient, while cybersecurity compliance is now a prerequisite for protecting proprietary digital assets. As regulatory scrutiny intensifies worldwide, organizations that integrate legal, technical, and governance strategies will be best positioned to operate, innovate, and scale in the global digital economy.
The intersection of IP law and cybersecurity creates particular tensions. While strong IP protection incentivizes creation and innovation, overly restrictive measures can hinder legitimate cybersecurity research and create vulnerabilities. Finding the right balance requires ongoing dialogue between rightholders, technologists, policymakers, and the public.
Looking forward, AI, blockchain, 3D printing, and other emerging technologies will continue challenging traditional IP frameworks. Success requires adaptable legal structures that protect creators while fostering the innovation and security research necessary for a thriving digital ecosystem. International cooperation through WIPO, TRIPS, and bilateral agreements remains essential for addressing global infringement in an interconnected world.
Understanding these frameworks empowers businesses to protect their IP assets, helps creators enforce their rights, and enables everyone to navigate the complex landscape where intellectual property, cybersecurity, and technology intersect in 2025 and beyond.
Glossary
Anti-Circumvention: DMCA provisions prohibiting bypassing technological protection measures
Copyright Management Information (CMI): Information identifying copyrighted works and rightsholder details
Digital Rights Management (DRM): Technological measures controlling access to copyrighted digital content
Safe Harbor: Legal protection for service providers against liability for user actions if they meet specified requirements
Takedown Notice: Formal request to remove allegedly infringing content from online platforms
Technological Protection Measures (TPM): Technologies preventing unauthorized access to copyrighted works
Trade Secret: Confidential business information providing competitive advantage
TRIPS: Trade-Related Aspects of Intellectual Property Rights agreement
WIPO: World Intellectual Property Organization
Frequently Asked Questions
How do intellectual property laws impact cybersecurity policy?
Intellectual property laws support cybersecurity policy by protecting software, algorithms, and digital infrastructure while enabling enforcement against cyber theft, trade secret breaches, and unauthorized data use.
Why are cybersecurity laws becoming stricter globally in 2025?
Governments are tightening cybersecurity laws due to increased ransomware attacks, AI-driven cybercrime, critical infrastructure risks, and growing concerns over cross-border data security.
Which regions have the strongest IP and cybersecurity regulations?
The European Union, the United States, China, and parts of Asia-Pacific have some of the most developed IP and cybersecurity frameworks, though enforcement approaches and regulatory priorities vary significantly.
How do global digital policies affect multinational companies?
Multinational companies must comply with overlapping IP, cybersecurity, and data protection laws, often requiring region-specific compliance strategies and stronger internal security controls.
What legal trends should businesses watch in 2025?
Key trends include tighter software IP enforcement, mandatory breach reporting, AI governance laws, expanded cybercrime penalties, and stronger cross-border data transfer rules.
What is the difference between copyright and patents in cybersecurity?
Copyright protects original creative expression fixed in tangible form (software code, documentation), while patents protect inventions (novel technical solutions, algorithms). Copyright arises automatically upon creation; patents require application and approval. Both face unique cybersecurity challenges—copyright from piracy, patents from theft of designs and trade secrets.
How does DMCA safe harbor work?
Service providers qualify for safe harbor from user infringement liability by: lacking knowledge of infringement, not receiving direct financial benefit, responding promptly to takedown notices, and implementing repeat infringer policies. This protects platforms like YouTube from liability for user-uploaded content if they follow proper procedures.
Can cybersecurity researchers legally bypass DRM?
Generally no, though the US Copyright Office grants limited three-year exemptions for specific purposes. Current exemptions allow some security research, but researchers risk DMCA liability for circumventing technological protection measures even without copyright infringement intent. Advocacy continues for permanent security research exceptions.
What is the TRIPS Agreement’s role in IP enforcement?
TRIPS establishes minimum IP protection standards for all WTO members and provides binding dispute resolution with potential trade sanctions for non-compliance. Unlike earlier WIPO treaties, TRIPS has enforcement mechanisms making it the most powerful international IP agreement.
How are courts handling AI-generated content IP issues?
Courts are beginning to address AI IP questions, with early cases suggesting that purely AI-generated works may lack human authorship required for copyright protection. However, using AI as a tool in creative processes may still yield copyrightable works. This remains an evolving area with significant uncertainty.
