Social engineering attacks are rising fast. This guide explains what social engineering is, how cybercriminals exploit human behavior, and the steps you can take to stay protected in 2025.
Cybersecurity threats have evolved dramatically, but one attack method remains devastatingly effective year after year, namely social engineering. Unlike technical exploits that target system vulnerabilities, social engineering attacks exploit the most unpredictable element in any security system, human psychology. In 2025, these attacks have become more sophisticated, widespread, and damaging than ever before.
Understanding social engineering is no longer optional for businesses, organizations, or individuals who want to protect themselves in the digital age. This comprehensive guide breaks down everything you need to know about social engineering attacks, how they work, and most importantly, how to defend against them.
Understanding Social Engineering: The Human Hack
Social engineering is a manipulation technique that exploits human psychology to gain unauthorized access to systems, data, or physical locations. Instead of hacking technology directly, attackers hack people, using deception, urgency, authority, and trust to trick individuals into divulging sensitive information or performing actions that compromise security.
According to the 2025 Unit 42 Global Incident Response Report:
“social engineering accounts for 36% of all security incidents, making it the single most effective entry point for cybercriminals.”
These attacks succeed not because of technological sophistication but because they understand and exploit fundamental human behaviors. The power of social engineering lies in its ability to bypass even the most advanced security measures. A company might invest millions in firewalls, encryption, and endpoint protection, yet a single employee falling for a convincing phishing email can provide attackers complete access to the network.
Social engineering works because it leverages psychological principles that include:
- Authority (people obey figures of power)
- Urgency (rushed decisions lead to mistakes)
- Fear (threats motivate immediate action)
- Trust (we believe people we think we know)
- Helpfulness (humans naturally want to assist others)

Source: Social Engineering Psychological
The Alarming Statistics of Social Engineering in 2025
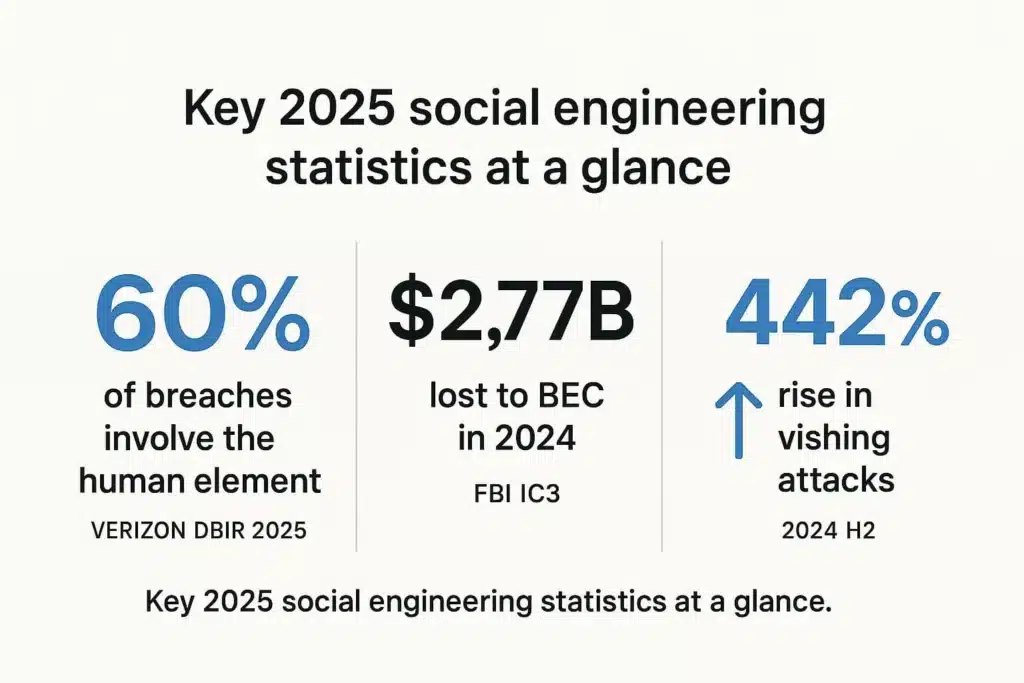
The scale and impact of social engineering attacks have reached unprecedented levels in 2025, with several concerning trends emerging from recent data.
Prevalence and Growth
According to Secureframe’s comprehensive statistics:
“The human element, including social engineering, user error, and privilege misuse, factors into approximately 60% of all data breaches in 2025.”
This highlights that human interaction remains the primary pathway for attackers. More specifically, 36% of all incidents in incident response caseloads began with a social engineering tactic. The CX Quest analysis shows that:
“66% of social engineering attacks target privileged accounts, while 60% lead to data exposure.”
Phishing remains the most common breach vector, accounting for roughly 16% of breaches with an average cost of $4.88 million per incident. The Anti-Phishing Working Group recorded over 1 million phishing attacks in Q1 2025 and 1.13 million in Q2 2025, representing a 13% quarter-over-quarter increase.
Financial Impact
The financial consequences of social engineering attacks are staggering. The FBI reports that Business Email Compromise (BEC) caused $2.77 billion in losses during 2024. The median loss from a single BEC incident is around $50,000, but individual cases can reach tens of millions.
The average cost of a social engineering attack reached $130,000 in 2024, with BEC attacks averaging $4.89 million. Spacelift’s research indicates that:
“89% of social engineering attacks between May 2024 and May 2025 were financially motivated.”
AI-Enhanced Threats
Perhaps most concerning is the integration of artificial intelligence into social engineering tactics. According to Secureframe’s data:
“91% of security professionals said their organizations faced AI-enabled email attacks in the past six months.”
Deepfake-enabled vishing (voice phishing) surged by over 1,600% in the first quarter of 2025. Voice cloning technology now requires just three seconds of audio to create convincing replicas that pass both automated systems and human verification.
Source: Social Engineering Statistics Dashboard
Major Types of Social Engineering Attacks
Social engineering manifests in numerous forms, each exploiting different psychological vulnerabilities. Understanding these attack types is essential for recognizing and preventing them.
Phishing Attacks
Phishing represents the most prevalent social engineering technique. These attacks involve fraudulent communications, typically emails, designed to entice recipients into sharing sensitive information or clicking malicious links. Messages often depict urgency or intrigue and appear to come from legitimate senders like CEOs, banks, or trusted companies.
According to Doppel’s security analysis:
“94% of organizations faced phishing attacks in 2024, with 96% of successful incidents causing negative business impacts.”
The Cofense Phishing Defense Center analyzed an average of one malicious email every 42 seconds throughout 2024. Common phishing channels include email (the primary vector), fake websites designed to look like legitimate login pages, social media platforms where attackers impersonate contacts, and SMS messages (smishing).
The most imitated brands in phishing attacks include Microsoft, Google, Amazon, DHL, DocuSign, PayPal, and various financial institutions. Attackers continuously update their tactics to mimic current trends and trusted services.
Spear Phishing
Spear phishing takes traditional phishing to a more targeted, personalized level. Instead of casting a wide net, attackers research specific individuals or organizations and tailor messages based on that information.
These attacks might reference recent activities, known contacts, or current projects to build credibility. An employee might receive an email that appears to come from a colleague mentioning a real ongoing project, making the deception far more convincing than generic phishing.
Business Email Compromise (BEC)
Business Email Compromise involves attackers gaining access to corporate email accounts and impersonating the owner to defraud the company, employees, customers, or partners. These attacks typically focus on employees with access to company finances, tricking them into conducting unauthorized wire transfers.
CEO fraud, a specific BEC variant, involves impersonating executive leadership to leverage authority and pressure employees into immediate action. A finance employee might receive what appears to be an urgent request from the CEO for an immediate wire transfer to complete a time-sensitive deal.
Vishing (Voice Phishing)
Vishing uses phone calls to manipulate victims into revealing sensitive information. Attackers often impersonate IT support, bank representatives, or government officials to create urgency and authority.
Deep Strike’s analysis shows:
“vishing surged 442% in late 2024, driven largely by AI-powered voice cloning technology.”
The 2023 MGM Resorts breach began with vishing when attackers impersonated an employee during a call to the IT help desk, ultimately gaining access to internal systems.
Pretexting
Pretexting involves creating a fabricated scenario or identity to trick people into revealing sensitive information or taking harmful actions. The attacker builds a convincing story that justifies their request for information.
Common pretexting scenarios include impersonating IT support requesting login credentials, posing as vendors needing account verification, pretending to be coworkers who forgot passwords, or claiming to be conducting security audits.
Baiting
Baiting attacks offer something enticing to lure victims into a trap. This might be physical (infected USB drives left in parking lots) or digital (free software downloads that contain malware).
The psychology relies on curiosity and the desire for free items. An employee finding a USB drive labeled “Salary Information 2025” in the company parking lot might plug it into their work computer, unknowingly installing malware.
Quid Pro Quo
Quid pro quo attacks offer services or benefits in exchange for information or access. The classic example involves someone calling employees pretending to be IT support, offering to fix a problem in exchange for login credentials.
These attacks exploit the natural human tendency toward reciprocity. When someone offers help or value, we feel obligated to provide something in return.
Tailgating and Piggybacking
These physical security attacks involve unauthorized persons gaining access to restricted areas by following authorized personnel. An attacker might carry boxes while approaching a secured door, hoping someone will hold it open out of courtesy.
Despite being low-tech, these methods remain effective because they exploit social norms around politeness and helpfulness.
Watering Hole Attacks
Watering hole attacks compromise websites frequently visited by target groups. Like predators waiting at literal watering holes, attackers infect trusted sites that specific user groups regularly visit.
When victims visit these compromised sites, malicious code deploys onto their systems. This method is particularly effective against organizations in specific industries that rely on common resource websites.
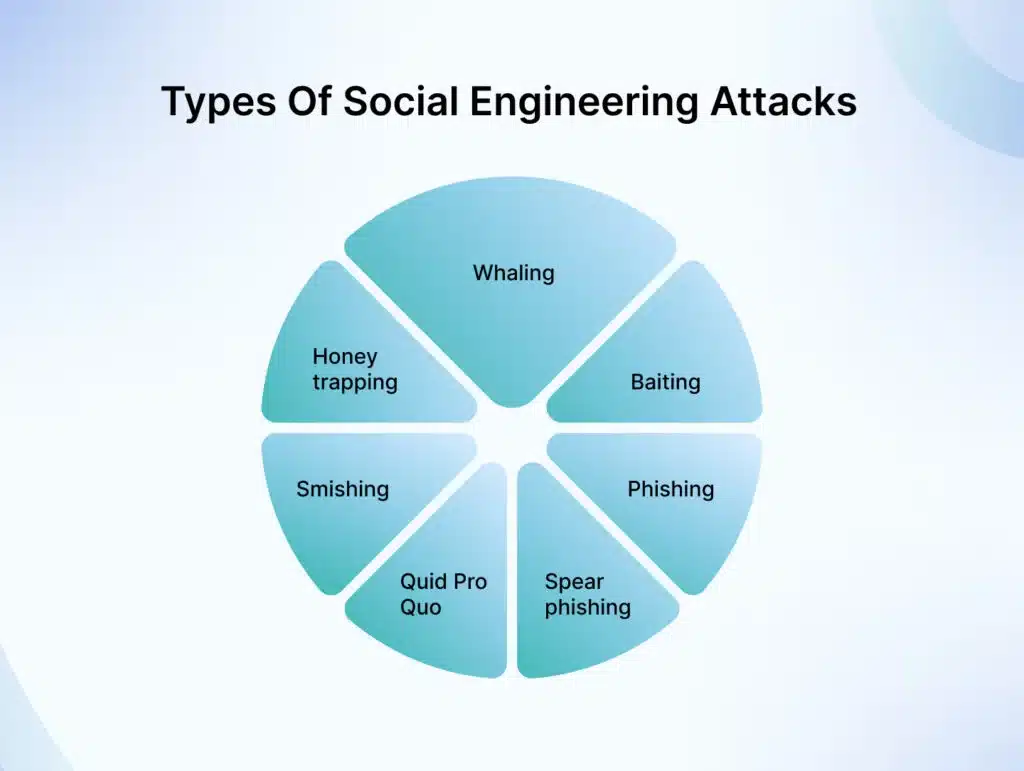
Source: Types of Social Engineering Attacks
The Role of AI in Modern Social Engineering
Artificial intelligence has fundamentally transformed the social engineering landscape, creating unprecedented challenges for security teams.
Three Layers of AI-Enabled Attacks
According to CX Quest’s threat analysis:
“cybercriminals now use three distinct layers of AI-enabled tooling.”
Automation streamlines traditional attack methods, allowing criminals to launch campaigns at massive scale with minimal manual effort. Generative AI creates highly personalized, human-like content across multiple channels, making attacks virtually indistinguishable from legitimate communications.
Agentic AI executes complex, multi-step attacks with minimal human oversight, including creating synthetic identities for insider campaigns that can persist undetected for extended periods.
Deepfake Technology
Voice cloning exemplifies AI’s impact on social engineering. With just three seconds of audio, attackers can create convincing voice replicas that fool both automated systems and human listeners. In one high-profile case, criminals used deepfake audio to impersonate a CEO and authorize a $25.6 million transfer.
Video deepfakes are becoming equally sophisticated, with AI-generated video calls featuring fake executives authorizing fraudulent transactions. These attacks succeed because they exploit fundamental trust in audiovisual verification.
ClickFix Campaigns
ClickFix represents the scalable side of modern social engineering. These attacks use fake browser alerts, fraudulent update prompts, and SEO poisoning to trick users into initiating their own compromise.
Between May 2024 and May 2025, ClickFix served as the initial access vector in at least eight confirmed incident response cases. The technique succeeds by mimicking trusted workflows like Microsoft update notifications or Google CAPTCHA verifications.
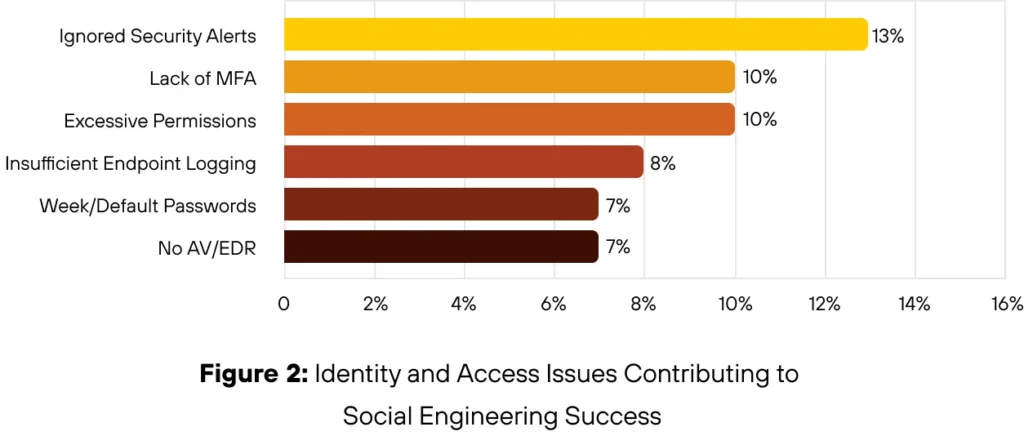
Source: Social Engineering Success
Comprehensive Prevention Strategies
Defending against social engineering requires a multi-layered approach combining technology, processes, and most importantly, educated humans.
Security Awareness Training
According to Secureframe’s prevention guide:
“regularly conducting security awareness training is the foundational defense.”
Organizations should educate employees at least annually, preferably quarterly, about different forms of social engineering attacks. Training should be practical and engaging, using real-world examples and interactive scenarios. Simulated phishing exercises help employees practice recognizing and reporting suspicious communications in a safe environment.
Key training topics include recognizing phishing emails and messages, verifying unexpected requests through alternative channels, understanding pretexting tactics, identifying urgency and authority manipulation, protecting sensitive information, and reporting suspicious activities immediately.
Multi-Factor Authentication (MFA)
Implementing phishing-resistant multi-factor authentication across all critical systems provides essential protection. Even if attackers obtain login credentials through social engineering, MFA creates an additional security barrier.
The Unit 42 report emphasizes:
“using phishing-resistant MFA methods like hardware tokens or biometric authentication rather than SMS-based codes, which can be intercepted.”
Email Security Controls
Deploy advanced email security solutions that filter and detect phishing attempts. Implement email authentication standards like DMARC, DKIM, and SPF to prevent email domain spoofing.
Advanced URL filtering blocks access to malicious infrastructure. These controls help detect and prevent social engineering attacks that rely on spoofed domains, typo-squatting, and link-based credential theft.
Verification Protocols
Establish clear, non-digital protocols for verifying unusual requests, especially those involving money transfers or sensitive data. Integrity360’s security recommendations suggest:
“For financial requests, require dual authorization and callback verification using known phone numbers (not numbers provided in the request).”
For sensitive data requests, confirm through separate communication channels. For urgent executive requests, establish pre-agreed verification methods like codewords.
Access Controls and Least Privilege
Limit access to sensitive systems and data based on job requirements. The principle of least privilege ensures employees only access resources necessary for their roles, reducing the impact of compromised accounts.
Regular access reviews identify and remove unnecessary permissions. Strong credential hygiene practices and limiting password reuse across systems prevent chained exposure when one account is compromised.
Incident Response Planning
Have a well-documented incident response plan ready. When social engineering attacks occur, quick, coordinated action minimizes damage.
The plan should include procedures for identifying compromised systems, isolating affected accounts and networks, containing the breach, conducting forensic analysis, communicating with stakeholders, and recovering operations.
Source: Security Framework Diagram
Technical Security Measures
While human awareness remains paramount, technical controls provide essential defense layers.
Identity Threat Detection and Response (ITDR)
Few organizations have implemented ITDR or user and entity behavior analytics (UEBA), yet these capabilities are increasingly vital for detecting social engineering attacks and preventing account takeover.
These systems establish behavioral baselines for users and flag anomalous activities like unusual login locations, unexpected data access patterns, or abnormal transaction volumes.
Endpoint Detection and Response (EDR)
Comprehensive EDR solutions with robust logging provide visibility into endpoint activities. Without clear indicators and behavioral baselines, analysts struggle to distinguish routine activity from compromise signs.
EDR tools can detect lateral movement attempts, unusual process executions, and suspicious file access patterns that indicate successful social engineering attacks.
DNS Security and Web Filtering
Advanced DNS security and URL filtering block access to malicious infrastructure. These controls are particularly effective against phishing attacks, watering hole attacks, and ClickFix campaigns that rely on malicious websites.
Network Segmentation
Proper network segmentation limits how far attackers can move after initial compromise. Even if social engineering grants initial access, segmentation prevents lateral movement to critical systems.
Data Loss Prevention (DLP)
DLP solutions detect and prevent sensitive data from leaving the organization through unauthorized channels. These tools can stop data exfiltration attempts even when attackers successfully compromise accounts through social engineering.
Responding to Social Engineering Attacks
Despite best efforts, some attacks will succeed. Effective response minimizes damage.
Immediate Actions
Doppel’s incident response guide recommends:
“Immediately identifying compromised systems, accounts, or networks and disconnecting them from broader infrastructure.”
Reset credentials for affected accounts and any accounts that might have been exposed. Enable enhanced monitoring for related systems and users.
Investigation and Containment
Determine the full scope of the compromise. What data was accessed? What systems were affected? How did the attack occur? What vulnerabilities were exploited?
Contain the damage by closing attack vectors, patching vulnerabilities, and preventing continued unauthorized access. Preserve evidence for forensic analysis and potential law enforcement involvement.
Communication
Notify affected parties according to regulatory requirements and organizational policies. Transparency about breaches builds trust, while attempted coverups destroy it.
Communicate with employees about what happened, what is being done, and what they should do. Provide clear guidance without creating panic.
Recovery and Remediation
Safely restore affected systems and data from clean backups. Implement additional security controls to prevent recurrence. Update incident response plans based on lessons learned.
Conduct post-mortem analysis to document what happened, what worked in the response, what did not work, and what changes are needed. Share these lessons across the organization.
Conclusion
Social engineering represents the most persistent and successful cyberattack method in 2025, exploiting the weakest link in any security system: human psychology. With 60% of data breaches involving human elements and attacks becoming increasingly sophisticated through AI enhancement, organizations cannot afford to treat security awareness as an afterthought.
Effective defense requires combining technical controls (MFA, email filtering, EDR, ITDR) with comprehensive security awareness training and a culture that values vigilance. No single measure provides complete protection, but layered defenses significantly reduce risk.
The human factor will always remain in cybersecurity. Attackers will continue innovating new ways to manipulate, deceive, and exploit people. However, informed, vigilant humans equipped with proper tools and protocols can recognize and thwart even sophisticated social engineering attempts.
As technology evolves, so must our defenses. Organizations that invest in ongoing security awareness training, implement robust technical controls, and foster security-conscious cultures will be best positioned to defend against the evolving threat landscape of social engineering.
Frequently Asked Questions
What is the most common type of social engineering attack in 2025?
Phishing remains the most common social engineering attack, accounting for approximately 65% of social engineering-driven intrusions. Email phishing, in particular, affects 94% of organizations, with over 1 million phishing attacks recorded quarterly. The prevalence exists because phishing requires minimal technical skill, reaches massive audiences, and successfully manipulates human psychology around urgency, authority, and trust.
How can individuals protect themselves from social engineering attacks?
Individuals should verify sender identities before clicking links or downloading attachments, enable multi-factor authentication on all accounts, be skeptical of urgent requests, especially those involving money or personal information, verify unusual requests through alternative communication channels, never share passwords or sensitive information via email or phone, keep software and systems updated, and report suspicious communications to IT or security teams immediately. Healthy skepticism and verification are the best personal defenses.
What should I do if I think I have fallen victim to a social engineering attack?
Act immediately to minimize damage. Change passwords for compromised accounts and any accounts using the same credentials. Notify your IT or security team about the incident, providing details about what happened. Disconnect affected devices from networks if malware might be involved. Monitor accounts for unauthorized activity and freeze credit if financial information was exposed. Report the incident to appropriate authorities, potentially including law enforcement for significant breaches. Document everything for investigation and future prevention.
How are companies using AI to combat AI-enhanced social engineering attacks?
Organizations deploy AI-powered security tools that analyze email patterns to detect sophisticated phishing attempts, monitor user behavior to identify anomalous activities suggesting account compromise, use machine learning to detect deepfake audio and video, automate threat intelligence gathering and sharing, and power adaptive security systems that learn from attack patterns. AI versus AI has become a critical battleground, with defenders using machine learning to stay ahead of AI-enhanced attacks.
What are the legal and financial consequences of social engineering attacks for businesses?
Financial consequences include direct losses from fraudulent transfers (averaging $50,000 for BEC incidents but reaching millions in major cases), costs associated with breach response, investigation, and remediation, regulatory fines and penalties for inadequate security practices, legal expenses from lawsuits by affected customers or partners, reputational damage leading to lost business, and increased insurance premiums. Beyond financial impact, according to research, 65% of consumers lose trust in businesses after data breaches, with many vowing never to return. Organizations also face enhanced disclosure requirements and potential criminal liability in cases of gross negligence.
